Google has open-sourced OSV-Scanner, a command-line vulnerability scanner designed to help developers identify security risks in their software dependencies. The tool addresses a critical gap in modern software development where projects often include hundreds of third-party dependencies, many of which may contain known vulnerabilities.
Key Takeaways
- Google has open-sourced OSV-Scanner, a vulnerability scanner that maps project dependencies against the OSV database across 11+ ecosystems.
- It features guided remediation and call analysis to reduce false positives.
What Google Built
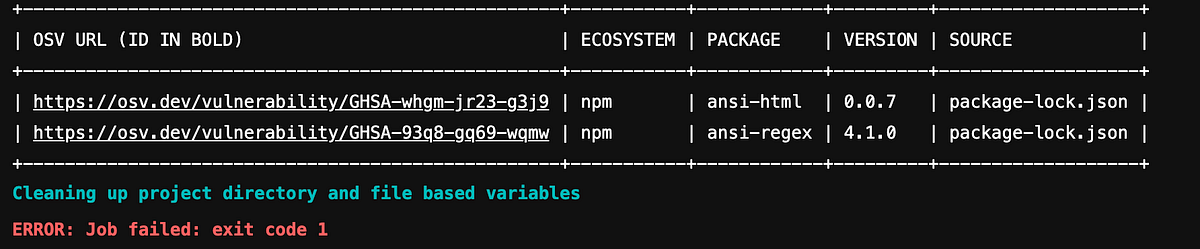
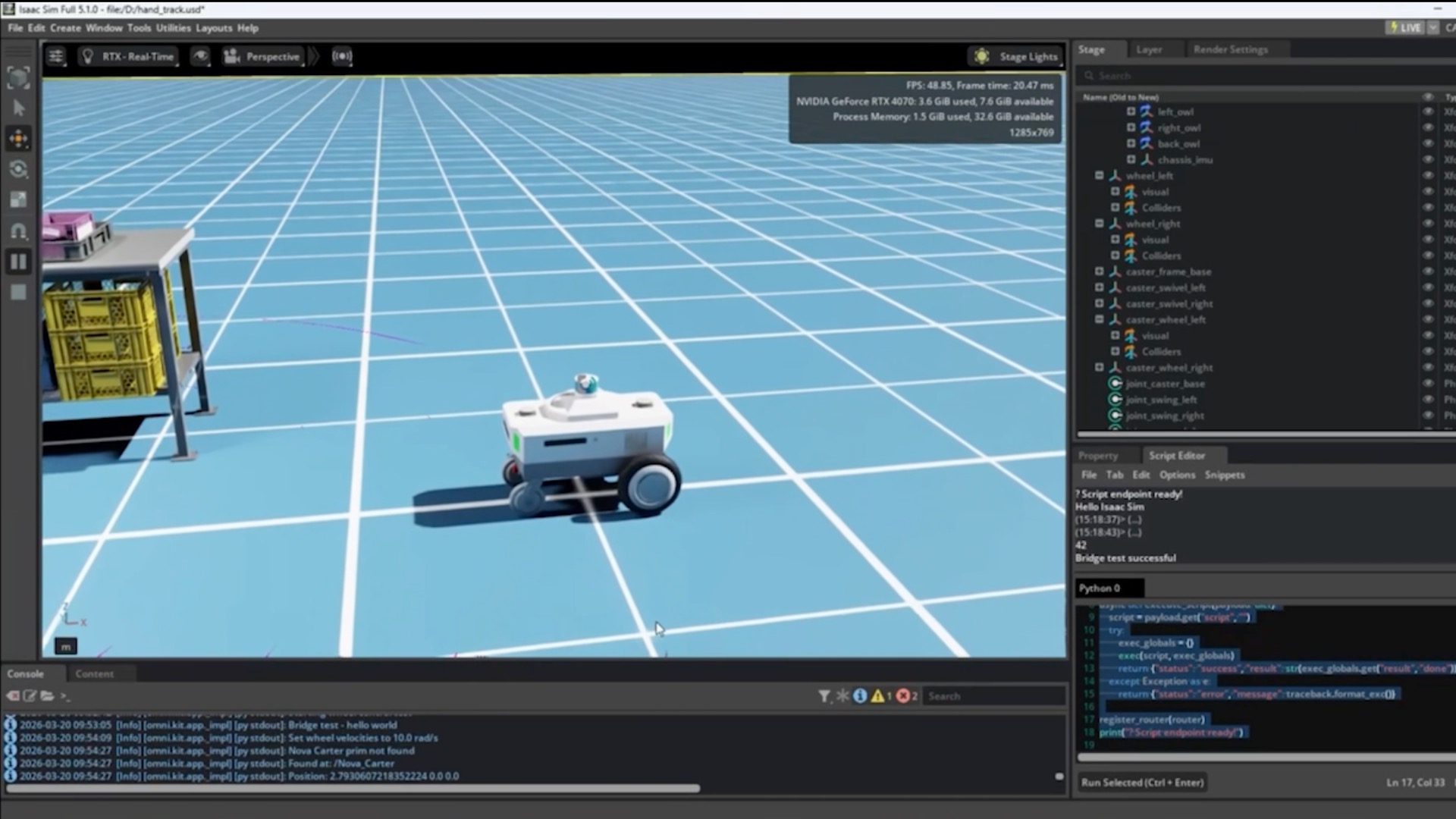
OSV-Scanner is a standalone tool that scans a project's entire dependency tree—including lockfiles, containers, and even vendored C/C++ code—and maps each dependency against the Open Source Vulnerabilities (OSV) database. The OSV database is an open, distributed vulnerability database that aggregates security advisories from multiple sources.
Unlike generic vulnerability scanners, OSV-Scanner provides guided remediation that doesn't just list problems but recommends specific version upgrades that fix the most issues with the least risk. The tool also includes call analysis that filters alerts to only those vulnerabilities in functions your code actually calls, significantly reducing noise.
Key Features & Technical Details
Multi-Ecosystem Support: OSV-Scanner supports 11+ package ecosystems including npm, pip, Cargo (Rust), Maven (Java), Go modules, RubyGems, and more. This broad coverage makes it applicable to polyglot codebases common in modern development.
Offline Operation: The tool can download the vulnerability database once and perform scans without an internet connection, making it suitable for air-gapped environments or CI/CD pipelines with restricted network access.
Simple Command-Line Interface: A single command scans an entire directory:
osv-scanner scan source -r ./
Integration-Friendly: The tool outputs results in JSON format, making it easy to integrate with existing CI/CD pipelines, security dashboards, or automated remediation workflows.
How It Works
OSV-Scanner operates through several key components:
Dependency Discovery: The tool parses project files (package.json, requirements.txt, Cargo.toml, etc.) to build a complete dependency graph, including transitive dependencies.
Vulnerability Matching: Each dependency is matched against the OSV database using precise version matching. The OSV database uses a structured schema that includes affected version ranges, making matching more accurate than CVE-based scanners.
Call Analysis (Optional): When enabled, the tool performs static analysis to determine whether vulnerable functions are actually called in the codebase, filtering out theoretical vulnerabilities that don't affect the specific application.
Remediation Guidance: Using constraint solving algorithms, the tool recommends the minimal set of version upgrades that address the most critical vulnerabilities while maintaining compatibility with other dependencies.
Why This Matters
Dependency vulnerabilities represent one of the most significant attack vectors in modern software. The 2024 State of Open Source Security Report found that 84% of codebases contain at least one known vulnerability in open-source dependencies, with the average application having 49 vulnerabilities.
Traditional vulnerability scanners often produce overwhelming numbers of false positives or require security expertise to interpret. OSV-Scanner's guided remediation and call analysis address these pain points directly, making vulnerability management more accessible to development teams without dedicated security staff.
Google's decision to open-source the tool follows their broader strategy of improving open-source security infrastructure. The OSV database itself was launched by Google in 2021 as part of their Assured Open Source Software initiative.
Competitive Landscape
OSV-Scanner enters a crowded market of software composition analysis (SCA) tools, but with several differentiating factors:
OSV-Scanner Google (Open Source) Guided remediation, call analysis, offline operation Free Snyk Commercial IDE integration, automatic PR creation, license compliance Paid GitHub Dependabot Microsoft/GitHub Native GitHub integration, automated dependency updates Free for public repos Trivy Aqua Security (Open Source) Container/image scanning, infrastructure as code Free Dependency-Check OWASP (Open Source) Extensive plugin ecosystem, mature codebase FreeOSV-Scanner's strongest advantage is its tight integration with the OSV database, which provides more precise version matching than CVE-based alternatives. The guided remediation feature also appears more sophisticated than the basic upgrade suggestions provided by tools like Dependabot.
Limitations & Considerations
While OSV-Scanner represents a significant advancement, developers should be aware of several limitations:
- Static Analysis Limitations: The call analysis feature uses static analysis, which may miss vulnerabilities in dynamically called code or through reflection.
- Database Coverage: The OSV database, while comprehensive, may not include all vulnerabilities, particularly those in less popular packages.
- Remediation Complexity: In complex dependency graphs with conflicting requirements, the "least risk" upgrade path may still break functionality.
- Language Support: While 11 ecosystems are supported, some niche or proprietary package managers are not included.
gentic.news Analysis
Google's release of OSV-Scanner represents a strategic move in the ongoing battle for developer tooling mindshare. This follows Google's February 2025 release of CodeGemma, their code-specific LLM, and aligns with their broader push into AI-assisted development tools. The pattern is clear: Google is systematically addressing the entire software development lifecycle with AI-powered tools, from code generation (CodeGemma) to code review (this follows their 2024 research on LLM-based code review systems) to now security scanning.
This release also represents a direct challenge to Microsoft's dominance in developer tools through GitHub. While GitHub offers Dependabot for dependency updates, OSV-Scanner's guided remediation appears more sophisticated, particularly for complex dependency graphs. The timing is notable—coming just months after Microsoft's acquisition of Snyk competitor Mend.io in late 2025 for $1.5 billion, which signaled Microsoft's doubling down on developer security.
From a technical perspective, the most interesting aspect is the call analysis feature. By determining whether vulnerable functions are actually called, OSV-Scanner addresses the primary complaint about traditional SCA tools: alert fatigue. This approach mirrors techniques used in Google's earlier research on precise program analysis for security, particularly their work on Amandroid for Android app analysis, now adapted for broader application.
For practitioners, the key takeaway is that dependency vulnerability management is moving from "find all problems" to "find problems that actually matter." OSV-Scanner's philosophy of reducing noise through precise analysis represents the next evolution of security tooling—one that respects developer time while improving security outcomes.
Frequently Asked Questions
What is the OSV database?
The Open Source Vulnerabilities (OSV) database is an open, distributed vulnerability database launched by Google in 2021. It aggregates security advisories from multiple sources using a structured schema that includes precise version ranges for affected packages. This makes it more accurate for vulnerability matching than traditional CVE databases, which often lack precise version information.
How does OSV-Scanner compare to Snyk or GitHub Dependabot?
OSV-Scanner is open-source and free, while Snyk is a commercial product with more extensive features like IDE integration and license compliance scanning. Compared to GitHub Dependabot, OSV-Scanner offers more sophisticated remediation guidance (suggesting upgrades that fix multiple issues with minimal risk) and works offline. Dependabot is tightly integrated with GitHub but requires internet access and provides simpler upgrade suggestions.
Can OSV-Scanner be integrated into CI/CD pipelines?
Yes, OSV-Scanner is designed for CI/CD integration. It can be run as a single command-line tool, outputs results in JSON format for easy parsing, and supports offline operation—making it suitable for environments with restricted network access. Many teams are already using it in GitHub Actions, GitLab CI, and Jenkins pipelines.
Does OSV-Scanner only work with open-source dependencies?
Primarily yes, as the OSV database focuses on open-source vulnerabilities. However, the tool can scan any dependency listed in supported package manager files, including private packages. The vulnerability matching will only work for packages with entries in the OSV database, which is predominantly open-source software.
Is the call analysis feature reliable for all programming languages?
The call analysis uses static analysis techniques that work better for some languages than others. It's most reliable for statically-typed languages like Go, Java, and Rust, and less reliable for dynamically-typed languages like Python and JavaScript where call graphs are harder to determine statically. Google acknowledges this limitation in their documentation.