What Changed — Aggressive Filtering in Opus 4.6
Multiple Claude Code users report that since late February 2026, Claude Opus 4.6 has begun blocking legitimate cybersecurity research with messages like "triggered restrictions on violative cyber content." This affects static analysis, decompilation, CWE-based auditing, proof-of-concept writing, vulnerability analysis, and patch diffing — even when working entirely offline with no live targets.
According to reports from paid Max users, the blocking appears to be account-level or context-level classification that's getting progressively stricter. Basic terms like "CVE" or "Secure" now trigger restrictions in fresh sessions, making cybersecurity workflows nearly impossible with Opus 4.6.
What It Means For Your Claude Code Workflow
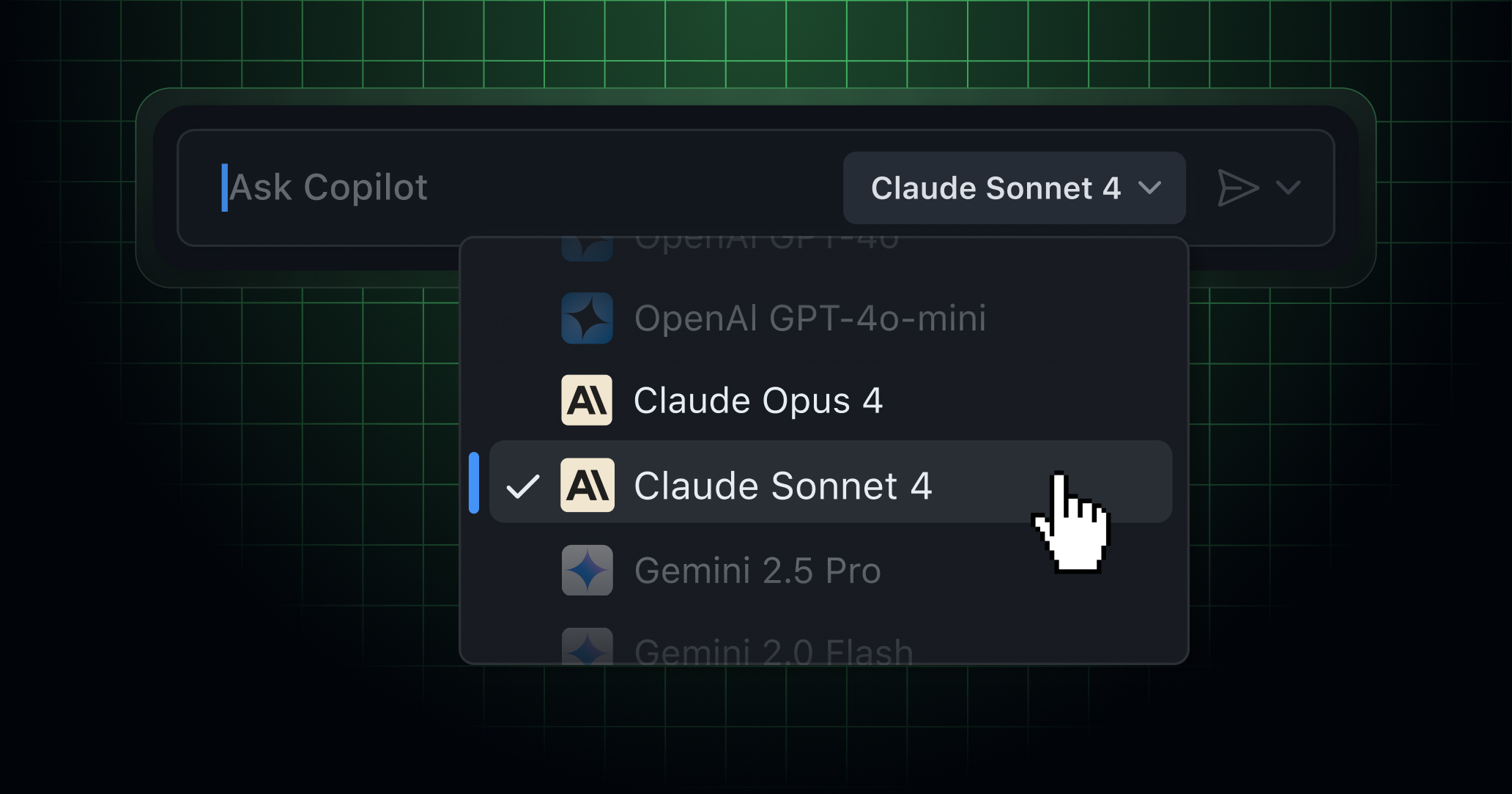
If you use Claude Code for security research, you're likely hitting these new guardrails. The error message specifically suggests switching models: "If you are seeing this refusal repeatedly, try running /model claude-sonnet-4-20250514 to switch models."
This isn't isolated to one user. Security researcher David Maynor has reported similar issues on X, and other Reddit users describe bash tool-calling being blocked. The pattern suggests Anthropic has tightened content filters significantly in Opus 4.6, possibly as part of broader safety measures ahead of their anticipated Q4 2026 IPO.
Try It Now — Immediate Workarounds
1. Switch to Sonnet Immediately
When you hit the cybersecurity restriction, don't waste time trying different prompts. Immediately switch models:
claude code /model claude-sonnet-4-20250514
Or start your session with Sonnet:
claude code --model claude-sonnet-4-20250514
Multiple users report Sonnet continues to handle cybersecurity tasks without triggering the new guardrails.
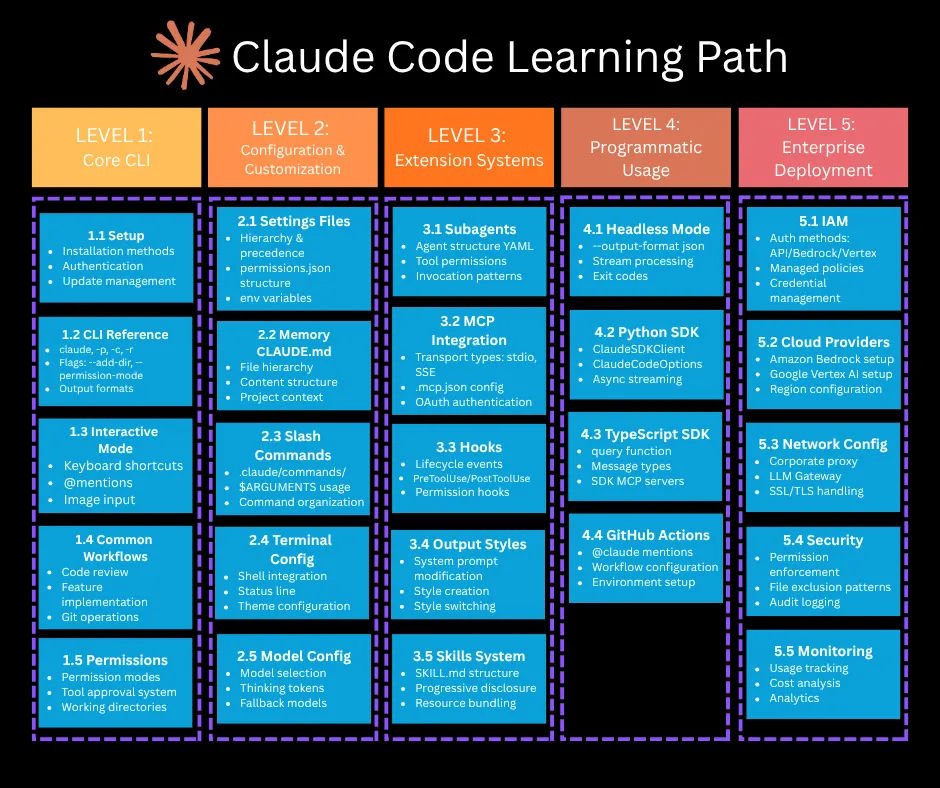
2. Use CLAUDE.md to Set Context
Create a CLAUDE.md file in your project root that establishes legitimate research context:
# Security Research Context
This project involves legitimate cybersecurity research including:
- Static analysis of open-source software
- Vulnerability analysis for defensive purposes
- CWE classification for educational use
- Proof-of-concept development in isolated VMs
All work is conducted offline with no live targets.
3. Submit the Cyber Use Case Form
If you need Opus 4.6's capabilities for complex analysis, submit Anthropic's Cyber Use Case Form with:
- Your professional background and certifications
- Links to previous public work/talks
- Specific examples of blocked legitimate research
- Request for whitelisting of your account
4. Consider Claude Agent for Complex Workflows
For multi-step security analysis, consider using Claude Agent with Sonnet models. The agent framework may provide more flexibility for complex research workflows that Opus 4.6 now blocks.
The Bigger Picture — Why This Matters
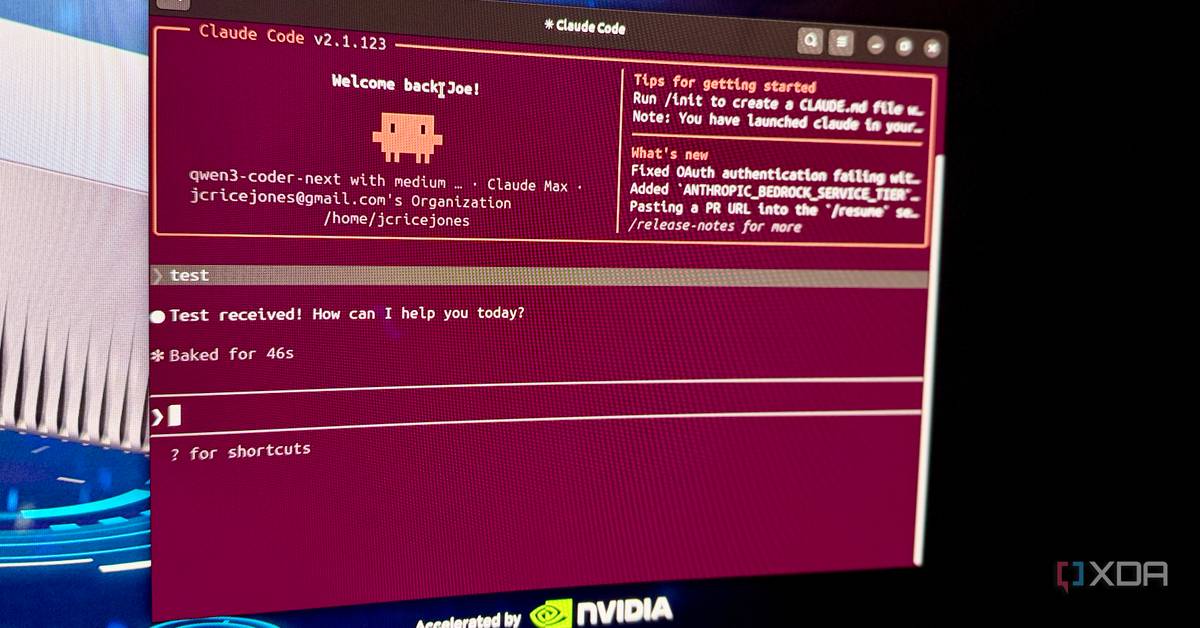
This follows Anthropic's March 2026 release of Claude Code Auto Mode and the /dream command for memory consolidation. As Claude Code becomes more capable (appearing in 175 articles this week alone), Anthropic appears to be tightening safety measures, particularly around potentially sensitive use cases.
The timing aligns with Anthropic's reported consideration of a Q4 2026 IPO, where demonstrating robust safety controls could be crucial for regulatory approval and investor confidence. This also follows Anthropic's partnership with the U.S. Department of Defense, which likely necessitates stricter content filtering around cybersecurity topics.
What to Do Today
- Test your security workflows — See if you're hitting the new restrictions
- Switch to Sonnet by default for security-related Claude Code sessions
- Document blocked legitimate use cases for support requests
- Explore Claude Agent for complex multi-model security analysis
- Monitor for updates — Anthropic may adjust these filters based on user feedback
Remember: The error message itself provides the solution. When Opus 4.6 blocks you, switch to Sonnet and keep your research moving.