What Happened
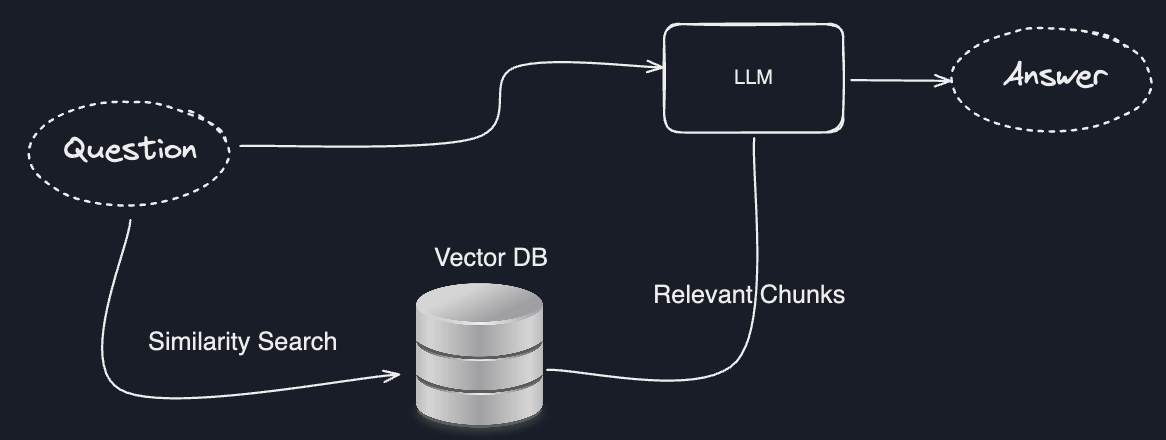
A new research paper, "Supercharging Federated Intelligence Retrieval," proposes a novel architecture to solve a fundamental limitation of standard Retrieval-Augmented Generation (RAG). The core problem is that RAG typically assumes all documents are available in a centralized index. This breaks down in real-world enterprise and retail scenarios where critical knowledge—such as supplier contracts, regional sales data, or exclusive design archives—is locked in separate, private data silos, often for security, compliance, or competitive reasons.
The proposed system, built using the federated learning framework Flower, re-architects RAG to keep sensitive data in place. Instead of moving documents to a central server, the retrieval step happens locally within each private data silo. Only the most relevant document chunks (or their secure representations) are then sent to a central server for aggregation and final LLM text generation.
Technical Details
The paper's innovation lies in its layered security and novel inference approach:
Confidential Compute for the Aggregator: The server-side component that aggregates retrieved chunks and runs the LLM operates inside an attested, confidential compute environment (e.g., using Intel SGX or AMD SEV). This means the server's memory and processing are encrypted and isolated, even from the cloud provider or a compromised operating system. This protects the query context and the generated response from "honest-but-curious" or malicious server administrators.
Cascading Inference with Third-Party LLMs: A particularly clever addition is a "cascading inference" approach. The system can incorporate a powerful, non-confidential third-party LLM (the paper uses the hypothetical Amazon Nova as an example) as an auxiliary source of general knowledge or reasoning. Crucially, this is done without exposing the private, retrieved documents to that external model. The confidential LLM acts as a gatekeeper, using the secure context to formulate a safe sub-query to the external model, then integrating that public knowledge into its final, confidential response.
In essence, it creates a secure, federated knowledge graph where the LLM can "see" across silos without any single party—not even the central coordinator—having unfettered access to all raw data.
Retail & Luxury Implications
This research, while academic, points directly to a critical, unsolved problem in luxury and retail AI: how to build cohesive intelligence across fiercely guarded data domains.

Cross-Departmental Intelligence: Imagine a concierge-style AI for a top client. To answer "What exclusive items from the upcoming collection might suit my client in Milan?", a perfect RAG system would need to access the Milan flagship's local client notes (CRM silo), the global design archive (product silo), and regional inventory logs (supply chain silo). Today, this is often impossible without risky data consolidation. Federated RAG provides a architectural blueprint for such a system.
Secure Supplier & Partner Collaboration: Brands co-develop products with external ateliers or manufacturers. A federated RAG system could allow an LLM to answer technical questions by retrieving from both the brand's internal material specs and the partner's confidential production documents—without either party surrendering their data.
Preserving Data Sovereignty: For global groups like LVMH or Kering, data residency laws (e.g., GDPR) and regional business practices often mandate data stay within geographic boundaries. A federated system could enable a global CEO's query to pull insights from EU customer data, APAC supply logs, and US financial forecasts while complying with all local regulations.
The reference to Amazon Nova is also telling. It highlights the industry trajectory towards leveraging massive, general-purpose foundation models (from Amazon, OpenAI, Anthropic) while keeping proprietary data utterly separate. This aligns with the cloud "Bedrock" and partnership strategies seen in the Knowledge Graph (e.g., Amazon's investments in Anthropic).
The Gap: This is a research proposal, not a production-ready library. The engineering complexity of managing a federated system with confidential compute across multiple corporate entities is significant. Latency, synchronization, and debugging in such a secure, distributed environment are non-trivial challenges. However, it provides a crucial north star for enterprise AI architects.