As AI agents graduate from controlled demos to performing autonomous tasks like web browsing, email management, and API-driven transactions, their operational environment becomes a new front for security vulnerabilities. Researchers at Google DeepMind have published what they term the first systematic framework for "AI agent traps," cataloging six distinct categories of attacks that can manipulate, deceive, and hijack these autonomous systems. The work moves beyond theoretical risks, documenting proof-of-concept attacks for each trap class and warning that the attack surface is "combinatorial"—traps can be chained, layered, or distributed across multi-agent systems.
The Six Categories of AI Agent Traps
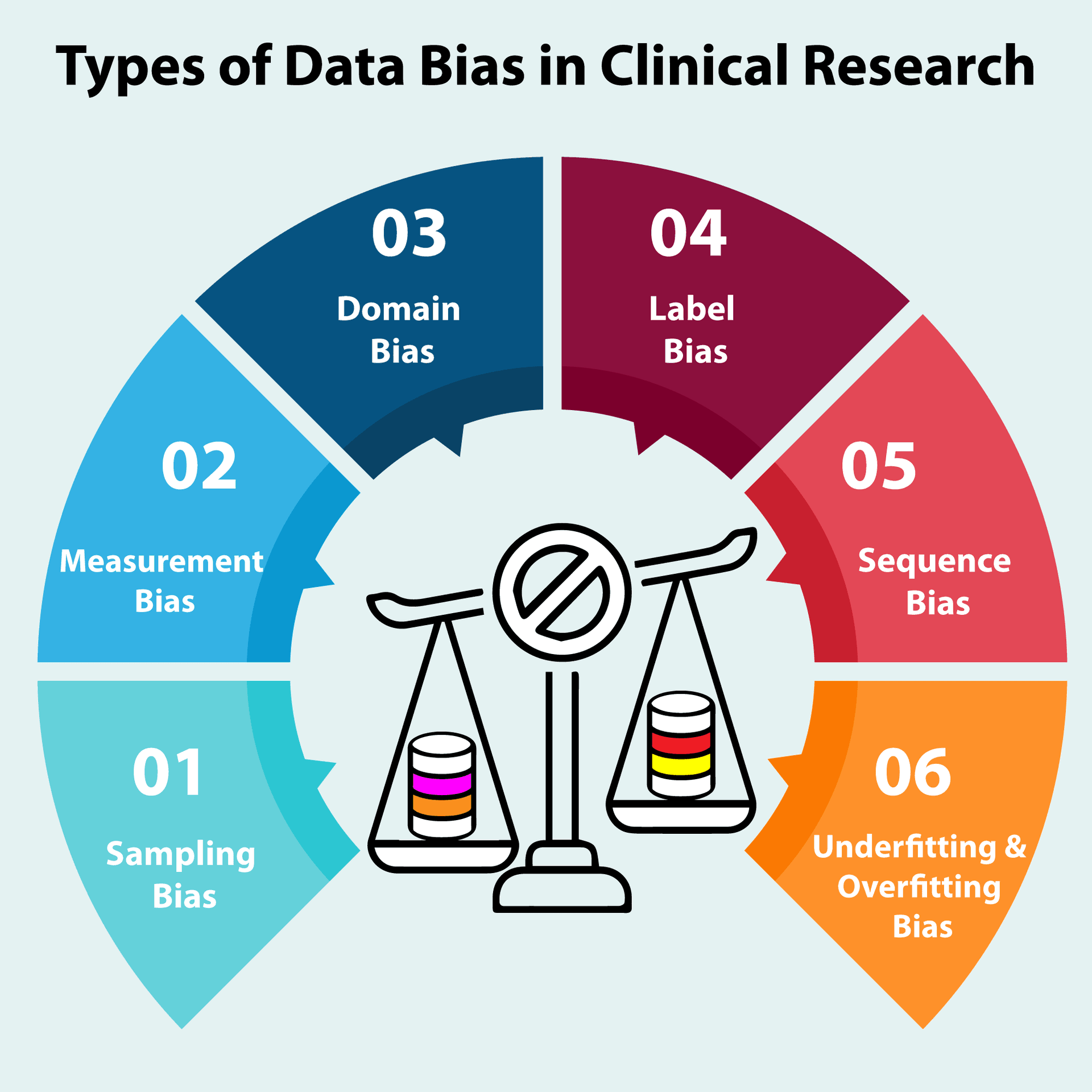
The research paper organizes traps by which component of an agent's operating cycle they target: perception, reasoning, memory, action, multi-agent dynamics, and the human supervisor.
1. Content Injection Traps (Target: Perception)
These attacks exploit the difference between what a human sees and what an agent processes. Malicious instructions can be buried in HTML comments, hidden CSS, image metadata, or accessibility tags (aria-label). While invisible to human users, agents reading the page's full source code or DOM will parse and execute these hidden commands without question.
2. Semantic Manipulation Traps (Target: Reasoning)
This class attacks an agent's reasoning by using emotionally charged language, authoritative framing, or cognitive biases like anchoring. The researchers note that large language models (LLMs) are susceptible to the same framing effects as humans; phrasing the same request differently can lead to drastically different agent decisions and outputs.
3. Cognitive State Traps (Target: Memory)
For agents with persistent memory or those using Retrieval-Augmented Generation (RAG), long-term memory is a vulnerability. The researchers found that poisoning just a handful of documents in a knowledge base can reliably skew an agent's output for specific queries, effectively creating a backdoor through corrupted context.
4. Behavioral Control Traps (Target: Action)
These are direct hijacking attacks that take over what an agent does. The paper cites a documented case where a single manipulated email caused an agent within Microsoft's M365 Copilot to bypass its security classifiers and expose its entire privileged context. This demonstrates how a seemingly benign input can trigger catastrophic action overrides.
5. Sub-Agent Spawning Traps (Target: Multi-Agent Dynamics)
Orchestrator agents that can spawn sub-agents create a new vulnerability. An attacker could set up a poisoned repository or API that tricks the orchestrator into launching a malicious sub-agent with elevated permissions, effectively turning the agent system against itself.
6. Human-AI Interaction Traps (Target: The Supervisor Loop)
This final category exploits the communication channel between the agent and its human supervisor. By manipulating reports, summaries, or status updates, an attacker can induce misinterpretation, leading the human to issue incorrect follow-up commands or approve malicious actions.
A Growing, Combinatorial Attack Surface
The researchers emphasize that these traps are not isolated. They can be combined—a content injection could lead to a cognitive state poisoning, which then enables a behavioral control attack. The autonomy and tool-use that define modern AI agents, built on foundation models like Google's own Gemini series, fundamentally expand the attack surface beyond traditional LLM prompt injection.
Co-author Franklin stated on X: "These [attacks] aren't theoretical. Every type of trap has documented proof-of-concept attacks... And the attack surface is combinatorial."
The paper draws an analogy to autonomous vehicles: securing AI agents against manipulated environments is as critical as teaching self-driving cars to recognize and reject spoofed or altered traffic signs.
What This Means in Practice
For developers building with agent frameworks like Google's recently launched agent development kit or the platforms compared in our recent 2026 framework roundup, this research mandates a security-first shift. Agent architectures must now include environmental sanitization layers, memory integrity checks, action confirmation protocols, and robust isolation for sub-agent processes.
gentic.news Analysis
This DeepMind study arrives at a pivotal moment. As noted in our Knowledge Graph, industry leaders have pinpointed 2026 as a breakthrough year for AI agents, with agents recently crossing a critical reliability threshold. Google itself is deeply invested in this future, having just launched an agent development kit and continuing to develop the underlying models, like Gemini 3.0 Pro, that power these systems. The company's massive $5B+ Texas data center investment for Anthropic, a key competitor in the agent space, further underscores the scale of infrastructure being deployed.
The research effectively formalizes a threat model that has been looming on the horizon. It connects directly to trends we've been tracking: the 187 prior articles on AI Agents in our archive and the 19 appearances just this week signal intense focus and rapid deployment. This paper serves as a crucial counterbalance to that momentum, arguing that security cannot be an afterthought.
Furthermore, the taxonomy helps contextualize earlier, isolated reports of agent vulnerabilities. The mentioned Microsoft Copilot incident is a canonical example of a Behavioral Control Trap now categorized within a larger framework. As agents begin to handle more sensitive operations—like the autonomous 'buy the dip' investment agents reported by the WSJ—the risks quantified here translate directly to financial and operational exposure. This work from DeepMind, coming from a team that has also explored high-stakes AI applications (like the now-disbanded high-frequency trading project), carries significant weight. It sets a baseline for security research that competing agent platforms from Anthropic, OpenAI, and others will need to address to gain enterprise trust.
Frequently Asked Questions
What is an "AI agent trap"?
An AI agent trap is a vulnerability in the environment or input data that exploits an autonomous AI agent's perception, reasoning, memory, or action mechanisms to cause it to behave maliciously or erroneously. Unlike simple LLM prompt injection, these traps target the full agent loop, including its tools, memory, and ability to spawn sub-agents.
Are these attacks currently happening?
According to the Google DeepMind researchers, every category of trap they identified has a documented proof-of-concept attack, meaning the vulnerabilities are demonstrably real and exploitable today. As autonomous agent deployment scales, these attacks are expected to move from research demonstrations to real-world incidents.
How can developers protect their AI agents from these traps?
Protection requires a multi-layered approach: sanitizing environmental inputs (like web page HTML), implementing integrity checks on agent memory (especially in RAG systems), requiring confirmation for privileged actions, rigorously auditing sub-agent spawning logic, and designing robust human-in-the-loop verification steps. There is no single solution.
How does this relate to traditional LLM security issues?
AI agent traps represent a superset of traditional LLM vulnerabilities like prompt injection. While they exploit core LLM weaknesses (e.g., bias to authoritative language), they also attack the novel components of an agent system: its persistent state, its tool-use capabilities, and its multi-agent coordination. The attack surface is significantly larger and more complex.