The Hidden Risk in Your MCP Gateway
You've set up an MCP gateway. Your agents connect centrally, you've solved auth translation, and you have observability logs. You're following the standard guides from Docker, Traefik, or Composio. But there's a critical gap that won't be obvious until your first major cost incident.
Here's the scenario that happens at Level 2 gateways: A research agent connects with access to both a cheap code search tool ($0.001/call) and an expensive code analysis tool that invokes an LLM ($2.00/call). The agent calls the expensive tool 800 times in two hours. Your gateway logs every call, your metrics spike, your alert fires—but the damage is already done: $2,400 in compute costs from a single agent.
Standard authentication confirmed the agent was valid. Standard authorization confirmed the agent could use the tool. Observability recorded everything. Rate limiting counted requests. None of these stopped the bleeding because they don't understand economic cost.
Layer 5: Economic Governance
Economic governance adds three capabilities your MCP gateway needs:
1. Per-Tool Cost Modeling
Every tool in your MCP catalog needs an economic weight. Your gateway should know that search_code costs virtually nothing while generate_analysis costs real money.
tools:
github.search_code:
cost: 1 credit # ~$0.001
analysis.review_code:
cost: 50 credits # ~$0.50 (invokes LLM)
analysis.generate_report:
cost: 200 credits # ~$2.00 (long-form generation)
With cost modeling, rate limiting becomes budget limiting. An agent with 500 credits can make 500 searches, or 10 code reviews, or 2 report generations.
2. Budget-Aware Tokens
Standard bearer tokens say "this agent is authenticated." Budget-aware tokens say "this agent is authenticated and has 1,000 credits remaining."
SatGate implements this with macaroon tokens—a cryptographic credential format that supports embedded caveats. A macaroon can encode total budget, expiration time, allowed tools, and delegation chains.
The critical property: macaroons support attenuation. A parent token can mint child tokens with fewer permissions, never more. An orchestrator with 10,000 credits can delegate 2,000 to a research sub-agent. That sub-agent can delegate 500 to a search specialist. Authority flows downward and diminishes—exactly what multi-agent architectures need.
3. Pre-Call Enforcement
This is the distinction between observability and governance. Observability logs a tool call after it happens. Governance decides whether the call happens at all.
# Gateway decision flow:
1. Agent calls tools/call with macaroon token
2. Gateway validates macaroon signature ✓
3. Gateway checks: is this tool allowed? ✓
4. Gateway looks up tool cost: 50 credits
5. Gateway checks remaining budget: 30 credits
6. 30 < 50 → DENY with structured 402 response
The denial is structured. The agent gets machine-readable context: how much it has, how much it needs, and what cheaper alternatives exist. Compare this to a rate-limit 429, which just says "try again later" and triggers a retry loop.
The MCP Gateway Maturity Model
Think of your gateway deployment as a progression:
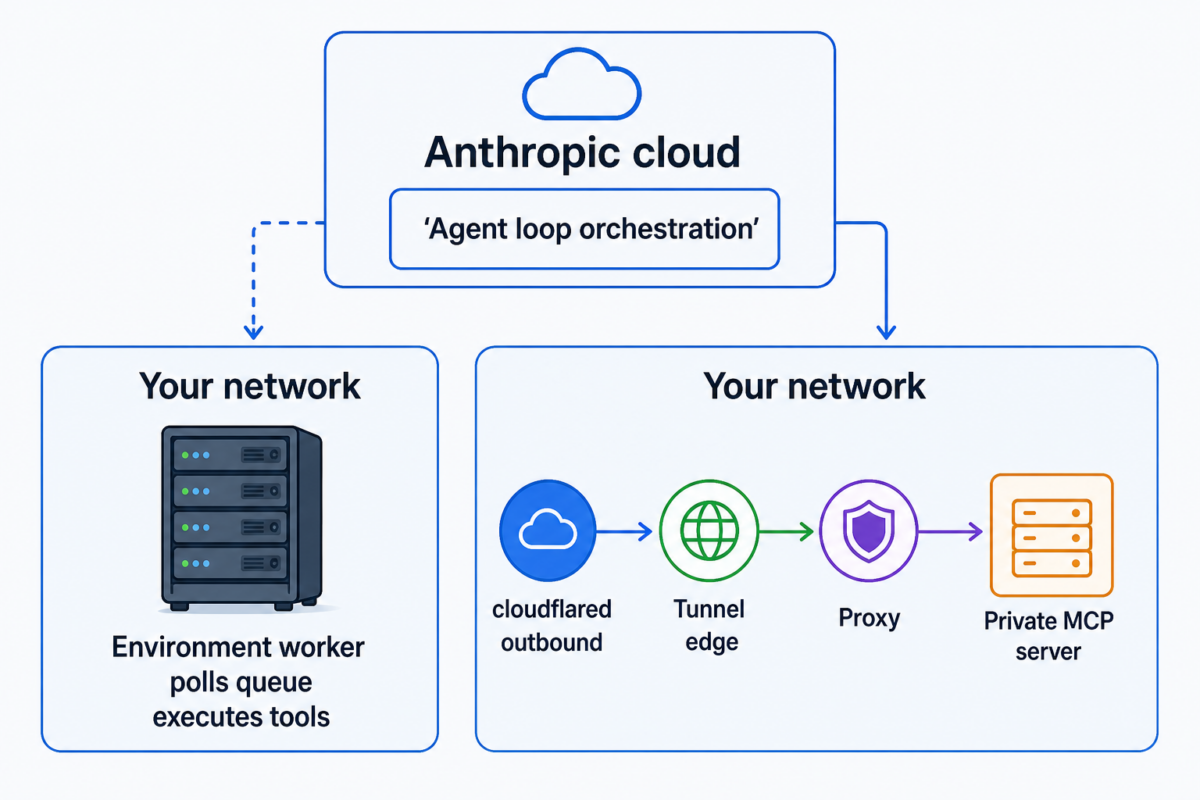
- Level 0: Direct connections. Each agent connects to each server. Works for prototypes.
- Level 1: Routing gateway. Centralized connections, auth translation, tool aggregation. This is where most guides end.
- Level 2: Observable gateway. Add structured logging, metrics, and alerting. You know what happened. You can't prevent it.
- Level 3: Governed gateway. Add cost modeling, budget enforcement, and hierarchical delegation. You control what happens, in real time.
Most teams are at Level 1 or 2. The cost incidents that push them to Level 3 are predictable and preventable.
Getting Started with SatGate
SatGate adds economic governance to your MCP gateway. It's open source:
go install github.com/satgate-io/satgate/cmd/satgate-mcp@latest
Economic governance isn't about distrust—it's about enabling autonomy safely. Agents with clear budget boundaries can operate more independently because the organization knows the blast radius is contained. The gateway doesn't slow agents down. It lets you give them a longer leash.
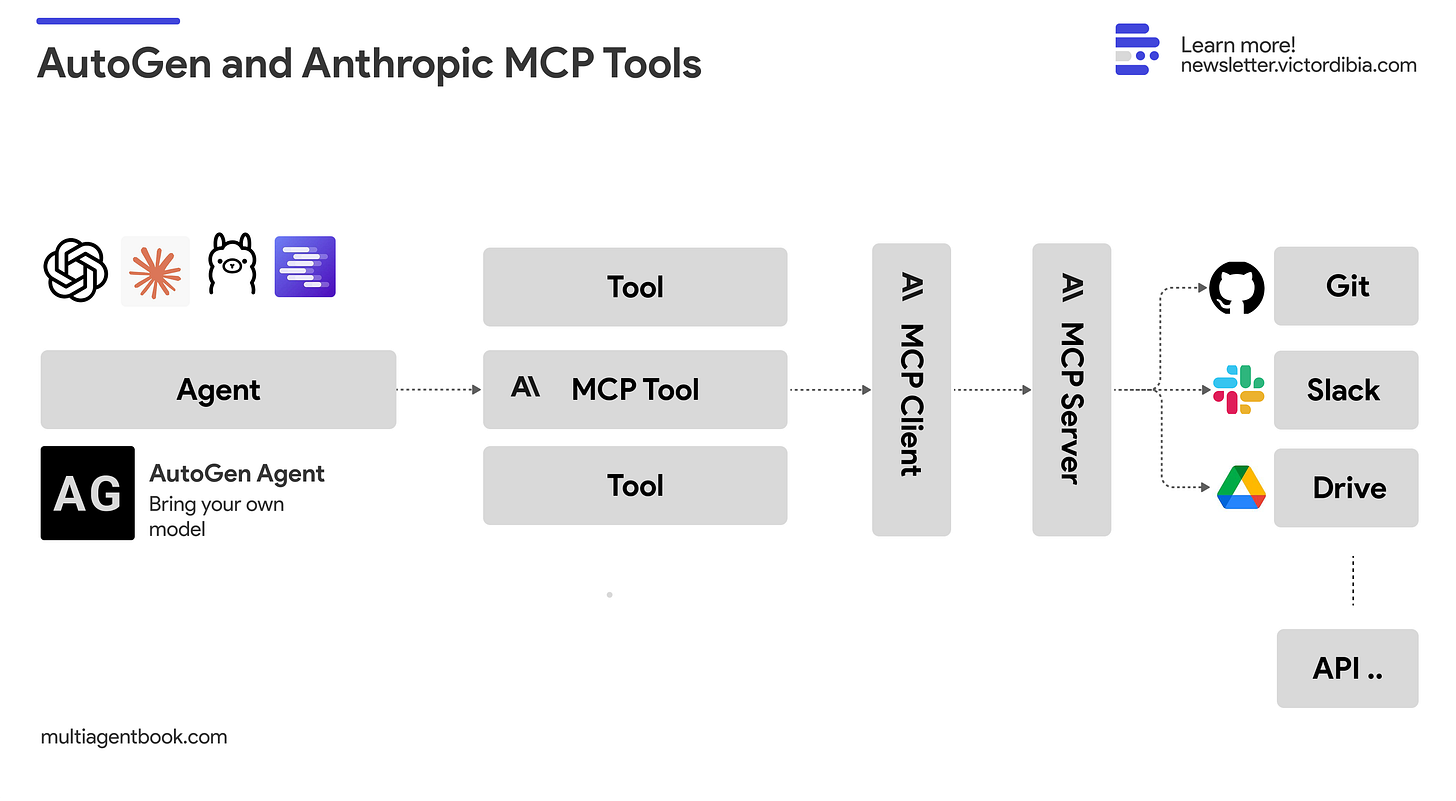
Why This Matters for Claude Code Users
If you're using Claude Code with MCP servers (like the Atlassian MCP Server that reached GA on February 4, 2026, or community alternatives like sooperset/mcp-atlassian with 4,700 stars), you're already in multi-tool territory. Each tool call has a different economic impact.
This follows the broader MCP ecosystem growth we've seen, including BitGo's institutional-grade crypto infrastructure MCP server launch. As more enterprise tools adopt MCP, the need for economic governance becomes critical.
Start by adding cost annotations to your MCP tool definitions. Even simple credit-based modeling prevents the worst-case scenarios. Then implement budget-aware tokens so your Claude Code agents can delegate work to sub-agents without risking budget overruns.