Keygraph, a company focused on AI-driven security, has launched a new product called Shannon. According to an announcement by CEO Gurinder Singh, Shannon is a "fully autonomous AI agent" designed to hack web applications. The core proposition is that Shannon proactively discovers and exploits security vulnerabilities before malicious actors can, turning offensive security techniques into a continuous, automated defense mechanism.
What Happened
Based on the announcement, Keygraph has developed and released Shannon. The AI operates autonomously, meaning it can be tasked with a target (like a web application URL) and will independently attempt to find and exploit security weaknesses. This process mimics the actions of a penetration tester or a malicious hacker, but with the goal of surfacing flaws for the development or security team to patch.
Context: The Shift to Offensive AI in Security
The field of application security testing is traditionally divided into two approaches:
- Static Application Security Testing (SAST): Analyzes source code for vulnerabilities.
- Dynamic Application Security Testing (DAST): Tests running applications, similar to how Shannon operates.
DAST tools and manual penetration testing are resource-intensive. Shannon represents a move towards fully automating the offensive security process using AI agents. This isn't the first attempt at using AI for vulnerability discovery; several research projects and startups have explored machine learning for fuzzing, code analysis, and attack simulation. However, a productized, fully autonomous agent marketed in this direct manner signals a maturation of the technology and its commercial readiness.
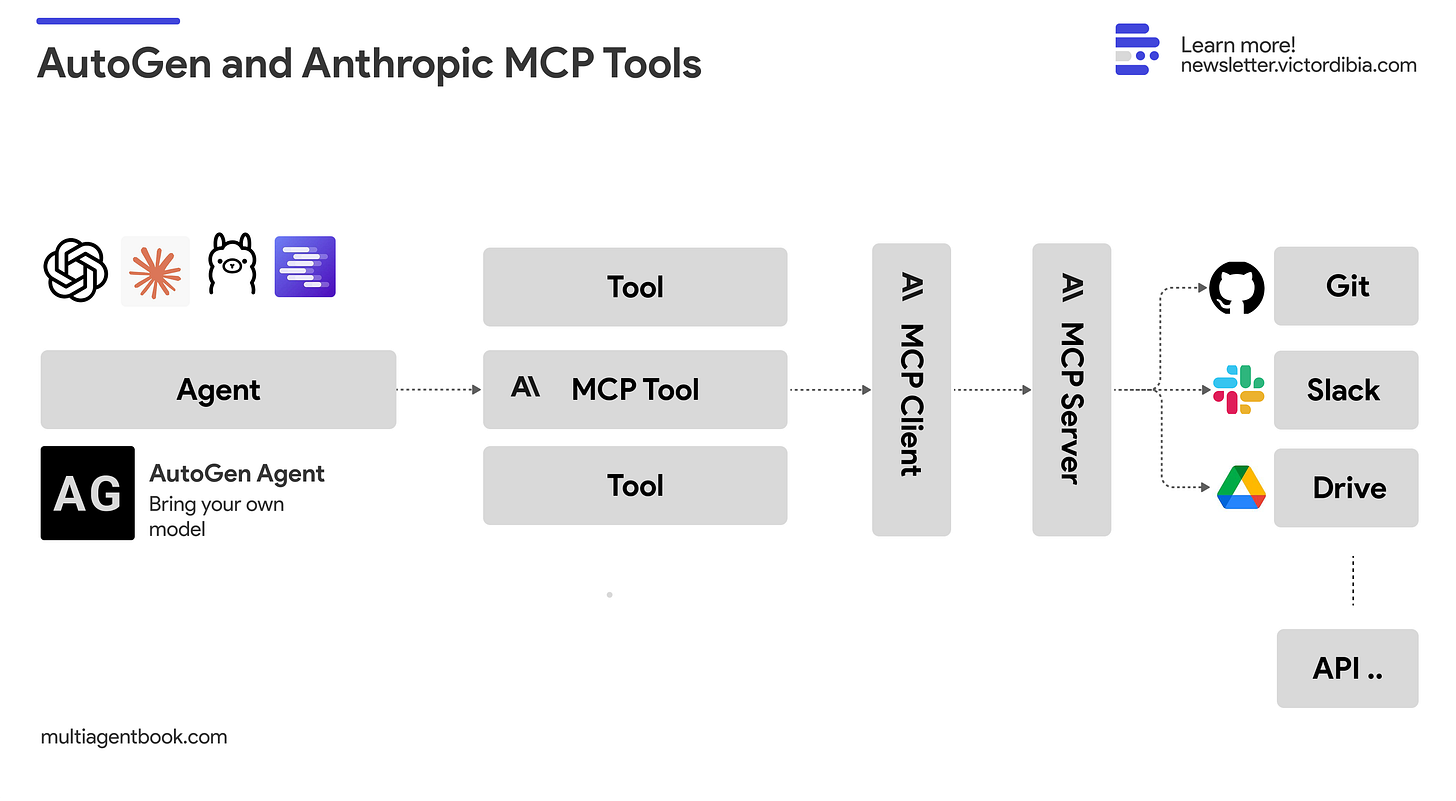
The launch follows a broader industry trend of applying large language models (LLMs) and agentic frameworks to complex, multi-step tasks. Security testing is a natural fit, as it requires understanding application structure, generating test payloads, interpreting responses, and adapting strategies—all capabilities advanced AI agents are now demonstrating.
What This Means in Practice
For development and security teams, a tool like Shannon could potentially:
- Run continuous, automated security tests alongside development cycles.
- Reduce reliance on scarce, expensive human penetration testers for initial scans.
- Simulate novel attack chains that rule-based scanners might miss.
However, the announcement lacks critical technical and practical details necessary for a full assessment. Key questions remain regarding Shannon's operational scope, accuracy, and integration.
Key Unanswered Questions & Considerations
The source announcement is high-level. Practitioners will need answers to the following before evaluating Shannon:
- Scope & Safety: What types of vulnerabilities does it target (e.g., OWASP Top 10, business logic flaws)? What safeguards prevent it from causing damage (e.g., data corruption, denial-of-service) during testing?
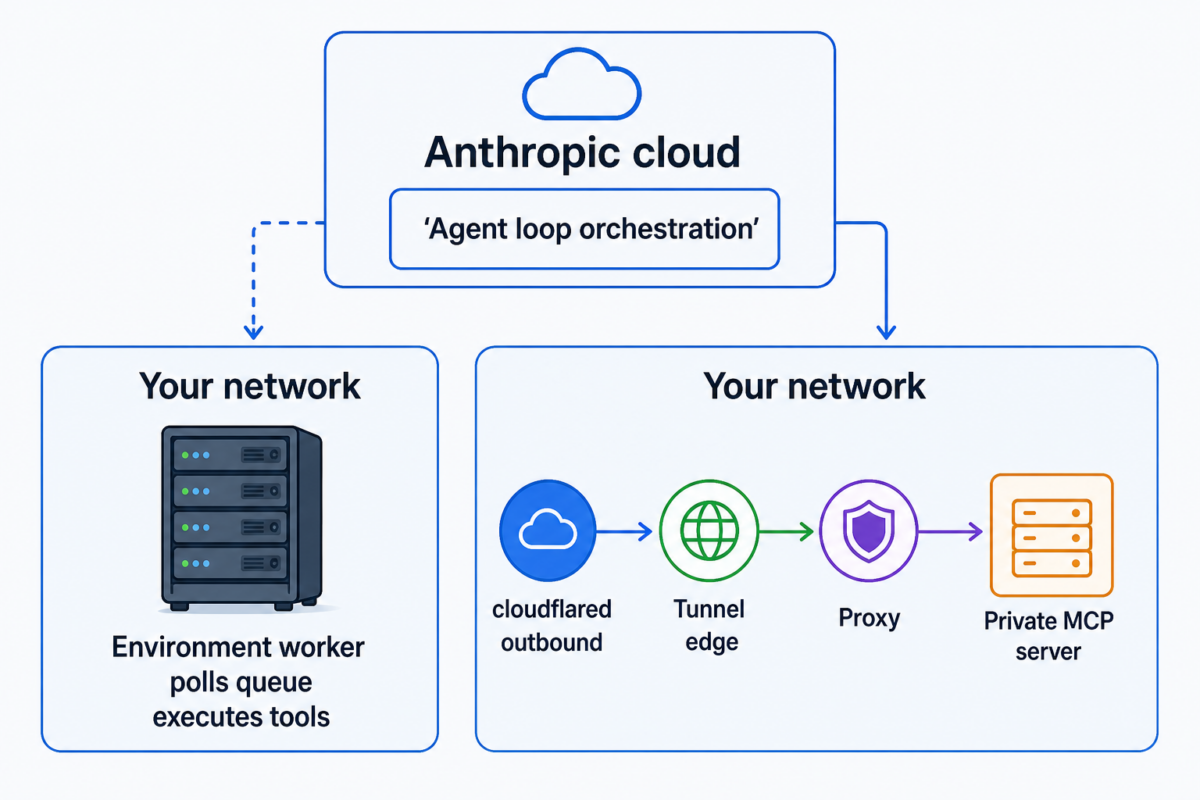
- Technical Architecture: Is it a cloud service, an on-premise deployment, or an API? How does it authenticate and interact with applications? What is its underlying model?
- Accuracy & False Positives: What is its rate of false positives and false negatives? How are its findings validated and presented?
- Compliance & Legal: How does its automated "hacking" align with authorized testing protocols and compliance requirements?
gentic.news Analysis
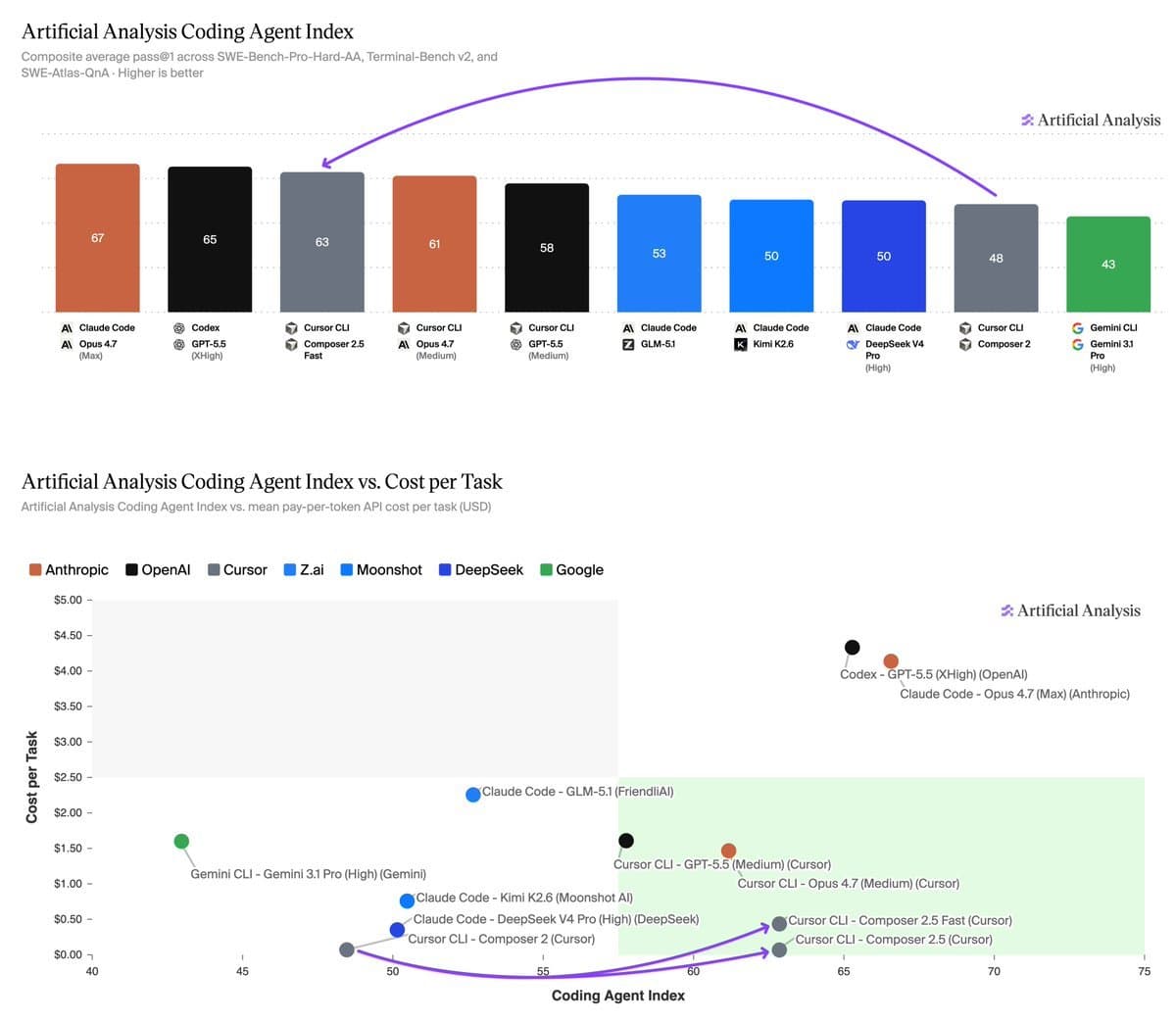
Keygraph's launch of Shannon is a bold entry into the rapidly evolving AI-powered cybersecurity market. It directly competes with established application security platforms like Snyk, Checkmarx, and Palo Alto Networks' Prisma Cloud, which have been integrating AI-assisted features, but positions itself further along the autonomy spectrum. This move is less about incremental improvement to existing SAST/DAST and more about a paradigm shift towards agentic, continuous offensive security.
This development aligns with the trend we identified in our coverage of Hunters' AI SOC platform and the rise of AI security co-pilots. The industry is bifurcating: one path uses AI to augment human analysts (co-pilots), while the other, exemplified by Shannon, seeks to fully automate specific analyst roles (autonomous agents). The success of the latter hinges on overcoming the "trust barrier"—security teams are notoriously risk-averse and will require transparent, verifiable results before allowing an AI agent loose on production systems.
Financially, this is a high-stakes bet. The application security market is large and growing, but crowded. Keygraph will need to demonstrate not just that Shannon can find bugs, but that it does so more efficiently, comprehensively, and cost-effectively than the combination of existing tools and human experts. Early adopters will likely be tech-forward companies with mature DevOps pipelines looking to add another layer of automated assurance. If Shannon can prove its value there, it could catalyze a wider adoption of autonomous offensive security agents.
Frequently Asked Questions
What is Keygraph's Shannon AI?
Shannon is an autonomous AI agent developed by Keygraph designed to automatically find and exploit security vulnerabilities in web applications. It performs automated penetration testing with the goal of identifying flaws before malicious hackers can discover and abuse them.
How is an AI hacking tool legal?
Tools like Shannon are intended for authorized security testing only. They are used by application owners, security teams, or authorized penetration testers on systems they have explicit permission to test. Using such a tool without authorization is illegal hacking. Responsible vendors build in safeguards and require proof of authorization.
How does AI-based security testing differ from traditional tools?
Traditional Dynamic Application Security Testing (DAST) tools often rely on predefined signatures and rules to find known vulnerability patterns. An AI agent like Shannon potentially uses machine learning to understand application behavior, generate novel attack payloads, and adapt its testing strategy in real-time, which could help uncover more complex or previously unknown vulnerability chains.
What are the risks of using an autonomous AI security agent?
The primary risks include the potential for the AI to cause unintended damage (like corrupting data or crashing a service), generating a high volume of false positives that waste analyst time, or missing critical vulnerabilities (false negatives), creating a false sense of security. Effective deployment requires careful scoping, monitoring, and validation of the AI's actions and findings.