What Happened
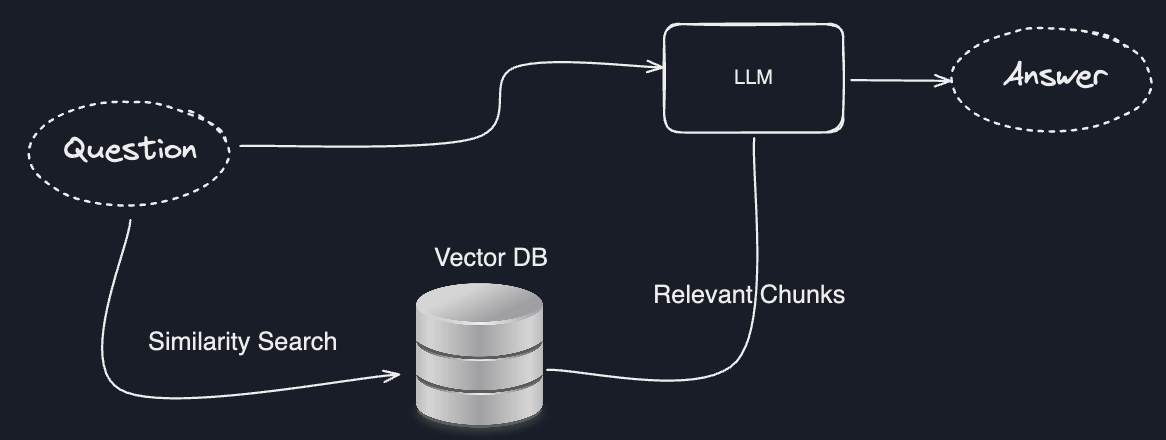
A new research paper, "Defending Against Knowledge Poisoning Attacks During Retrieval-Augmented Generation," has been posted to arXiv. The work addresses a critical security vulnerability in Retrieval-Augmented Generation (RAG) systems, which are widely used to ground large language models (LLMs) in external, up-to-date knowledge.
The core problem is a knowledge poisoning attack dubbed PoisonedRAG. In this scenario, an attacker compromises the external knowledge source (e.g., a vector database of product manuals, policy documents, or style guides) by injecting adversarial texts. When a user asks a specific "target question," the RAG system retrieves this poisoned text, which is designed to steer the LLM to generate an attacker-chosen, incorrect, or malicious response.
Technical Details
The researchers propose two novel defense methods: FilterRAG and ML-FilterRAG. The core of their approach is the identification of a new, distinct property that differentiates adversarial texts from clean ones within a knowledge source. While the paper abstract does not specify the exact property (likely detailed in the full paper), it is described as a measurable characteristic of the text that reveals its adversarial nature.
- FilterRAG employs this property directly to filter out suspected adversarial texts from the retrieved context before it is passed to the LLM for answer generation.
- ML-FilterRAG builds upon this, presumably using the identified property as a feature within a machine learning classifier to perform the filtering with greater sophistication.
The evaluation on benchmark datasets shows that both proposed defenses are effective. Crucially, their performance in generating correct answers is reported to be close to that of the original, uncompromised RAG systems, indicating they successfully block the attack without significantly degrading the utility of the system.
Retail & Luxury Implications
For retail and luxury brands deploying RAG systems, this research highlights a previously underexplored operational risk with direct business consequences.

Potential Attack Vectors in Retail:
- Customer-Facing Chatbots & Virtual Assistants: A poisoned knowledge base could cause a brand's AI assistant to give wildly incorrect product information (e.g., "This handbag is machine washable"), misquote pricing or promotion details, or provide harmful usage instructions.
- Internal Knowledge Management: RAG systems used by customer service agents or retail staff for accessing internal manuals, return policies, or inventory data could be manipulated, leading to inconsistent service, policy violations, or operational errors.
- Content & Campaign Management: If a RAG system is used to inform marketing copy or campaign planning by retrieving from a repository of brand guidelines and past campaigns, poisoned data could lead to off-brand or damaging communications.
The PoisonedRAG attack is particularly insidious because it doesn't require breaching the core LLM API or model weights. It only requires the ability to insert documents into the retrievable knowledge source. This could be achieved through compromised data ingestion pipelines, insider threats, or by poisoning publicly scraped data used to populate the knowledge base.
The proposed FilterRAG and ML-FilterRAG defenses represent a necessary layer in the security stack for production RAG. For technical leaders, this paper is a signal to audit their RAG data pipelines for integrity and to consider implementing similar adversarial detection mechanisms as part of their retrieval or re-ranking steps. The goal is to ensure that the "augmentation" in RAG is from trusted, verified knowledge, not a vector for misinformation.