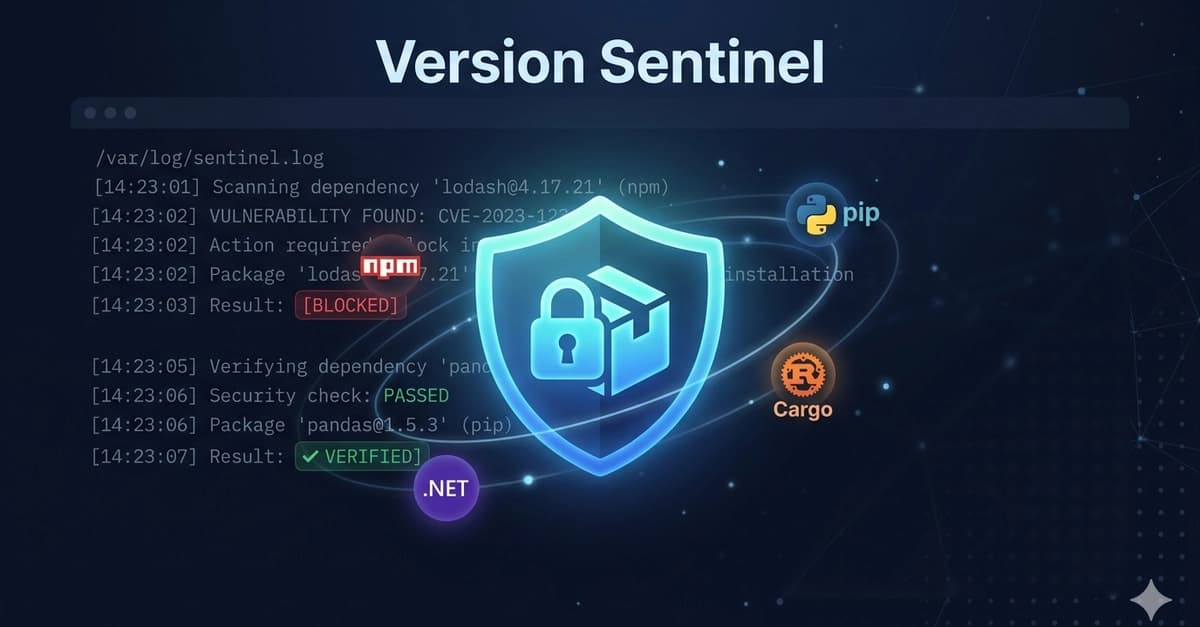
What Changed
If you've used Claude Code for any length of time, you've seen it do this:
npm install lodash@4.17.21
...when the latest version is actually 4.17.21 (or worse, a version that doesn't exist on the registry at all). Claude hallucinates package versions just like it hallucinates anything else — and that's a supply-chain risk.
Developer KSEGIT built Version Sentinel, a Claude Code plugin that uses the hook system to hard-block any dependency change until you've verified the version is real and current.
How It Works
Version Sentinel intercepts two types of actions via PreToolUse hooks:
- Manifest file edits — changes to
package.json,requirements.txt,pyproject.toml,Cargo.toml,*.csproj - Install commands —
npm install,pip install,cargo add,dotnet add
If there's no fresh version check on record → the action is blocked with exit code 2. You then run WebSearch to verify the latest version, use /vs-record to log it, and Claude retries the action.
PostToolUse hooks auto-record successful installs, so verified packages stay unblocked for future sessions.
Try It Now
claude plugin add KSEGIT/Version-Sentinel

Prerequisites: bash, jq, curl, python3
Once installed, you also get the /check-versions command — it audits ALL dependencies in your project against upstream registries. It reports drift without blocking, showing you which deps are outdated and which are intentionally pinned.
Why This Matters
This is a concrete example of using Claude Code's hook system to build guardrails around a specific failure mode. The same pattern could be applied to:
- Blocking
rm -rf /or other destructive shell commands - Requiring confirmation before modifying production config files
- Enforcing that API keys or secrets aren't written to source files
Version Sentinel is MIT-licensed and available on GitHub at KSEGIT/Version-Sentinel.
gentic.news Analysis
This plugin addresses a real pain point that's been discussed extensively in the Claude Code community. As we've covered in previous articles on Claude Code's hook system, the PreToolUse and PostToolUse hooks are still underutilized by most developers. Version Sentinel demonstrates the pattern well: intercept, verify, then proceed.
Anthropic (the company behind Claude Code, founded 2021, HQ San Francisco) has been rapidly iterating on the Claude Code product since its 2025 launch. The hook system was added in response to developer feedback about safety and control — and this plugin is exactly the kind of community-built guardrail they envisioned.
For developers managing large projects with Claude Code (like the parallel instance architecture we covered last week), this plugin could be a critical safety net. When you're running 10+ instances simultaneously, you can't manually verify every package version Claude suggests.
What to do: Install Version Sentinel today, then think about what other guardrails you could build using the same hook pattern. The plugin's source code is MIT-licensed, so you can fork it and adapt it for your own failure modes.