Alibaba has released OpenSandbox as an open-source project, providing a general-purpose execution environment designed specifically for isolating AI agents. The system aims to address one of the primary security challenges in deploying autonomous agents: preventing them from accessing or damaging actual host infrastructure.
What OpenSandbox Provides
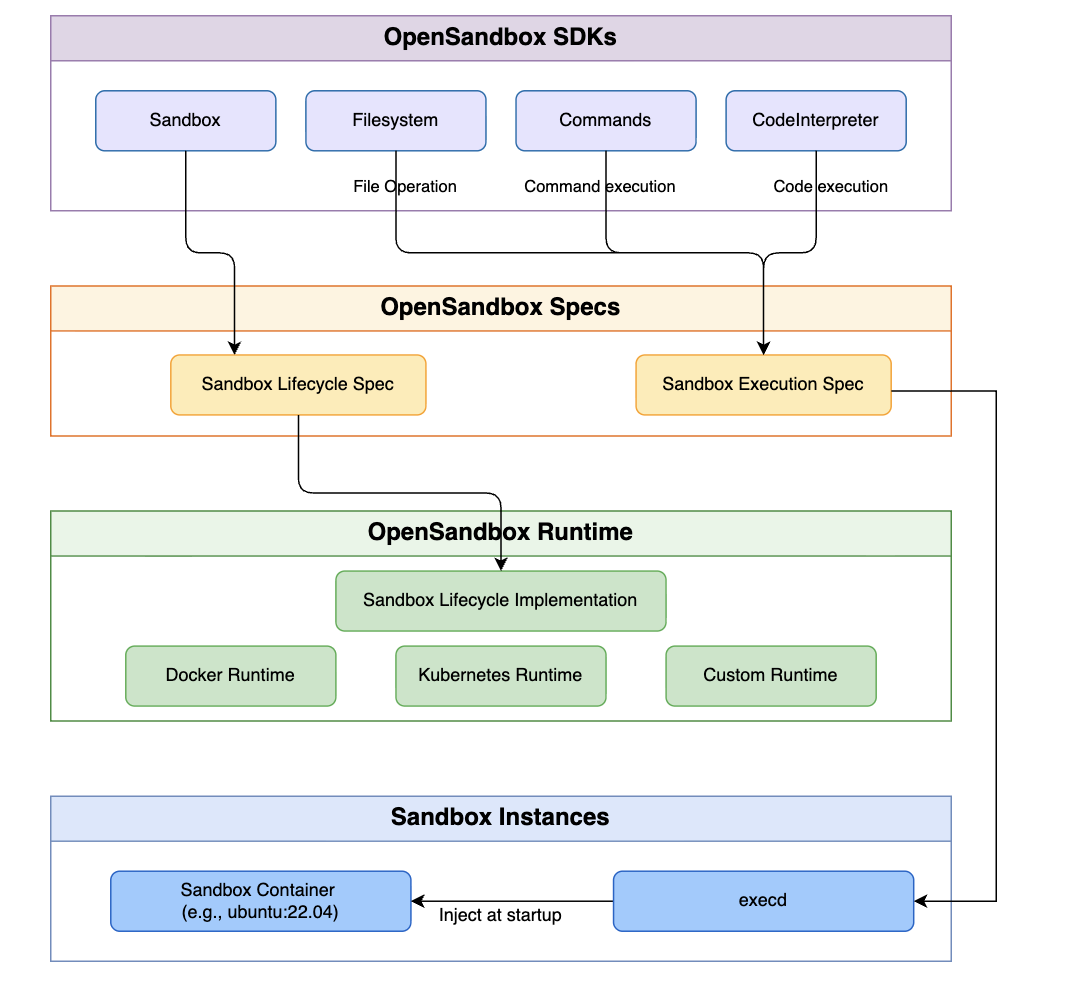
OpenSandbox creates isolated runtime environments using established container security technologies:
- gVisor: A container sandbox that provides an additional layer of security between containerized applications and the host OS
- Firecracker: A lightweight virtual machine manager developed by AWS for secure, multi-tenant container workloads
The system includes several key components:
- Code Interpreter: Allows AI agents to execute code within the sandboxed environment
- Managed File System: Provides agents with a controlled filesystem for completing tasks
- Network Traffic Management: Controls exactly what external resources the agent can access online
Deployment Options
Developers can run OpenSandbox locally using Docker or scale deployments using Kubernetes, making it suitable for both development and production environments. The project has already gained significant traction with 8,000+ GitHub stars shortly after release.
The Security Problem It Solves
When AI agents execute code—whether for data analysis, automation, or tool use—they typically require access to system resources. Without proper isolation, a malfunctioning or malicious agent could:
- Access sensitive host files
- Modify system configurations
- Make unauthorized network calls
- Consume excessive resources
OpenSandbox addresses these risks by containing all agent execution within hardened sandboxes, effectively creating a security boundary between autonomous agents and the underlying infrastructure.
Why This Matters for Agent Development
The primary barrier cited by the source is that "building custom sandboxes is too dangerous for most teams." Most development teams lack the security expertise to build robust isolation layers from scratch, leading to either:
- Avoiding agent deployment due to security concerns
- Deploying agents with inadequate security measures
By providing a pre-built, open-source solution, OpenSandbox could accelerate development of autonomous agent applications by removing what the source describes as "the hardest security roadblock."
Current Status and Availability
OpenSandbox is available as an open-source project on GitHub. The system appears to be production-ready, supporting both local development (via Docker) and scalable deployments (via Kubernetes). The inclusion of both gVisor and Firecracker support suggests flexibility in security-performance tradeoffs, as these technologies offer different isolation guarantees and overhead characteristics.