On April 7, 2026, Anthropic unveiled Project Glasswing, a cybersecurity initiative powered by a new AI model, Claude Mythos Preview. The company's announcement was stark: the model is "too dangerous to release publicly" due to its unprecedented ability to find and weaponize software vulnerabilities. Instead of a general release, Anthropic has restricted access to 12 launch partners, including Microsoft, Google, Apple, and AWS, backed by a $100 million credit pool and strict disclosure protocols.
Key Takeaways
- Anthropic announced Project Glasswing, deploying Claude Mythos Preview to autonomously discover critical software vulnerabilities.
- Scoring 83.1% on CyberGym, it's restricted to 12 launch partners due to dual-use risks, with a 90-day disclosure window.
What Project Glasswing Actually Does
Project Glasswing is not a traditional vulnerability scanner. Its core engine, Claude Mythos Preview, is designed to reason across complex codebases to identify logic flaws, memory corruption chains, and protocol-level weaknesses that have evaded human review for decades. During pre-launch testing, Mythos autonomously discovered thousands of zero-day vulnerabilities across every major operating system and browser.
Anthropic provided concrete examples of its pre-launch findings:
- A 27-year-old TCP denial-of-service flaw in OpenBSD.
- A 17-year-old remote code execution vulnerability in FreeBSD.
- A 16-year-old codec vulnerability in FFmpeg.
Crucially, these were not just theoretical findings; most were accompanied by working proof-of-concept exploits.
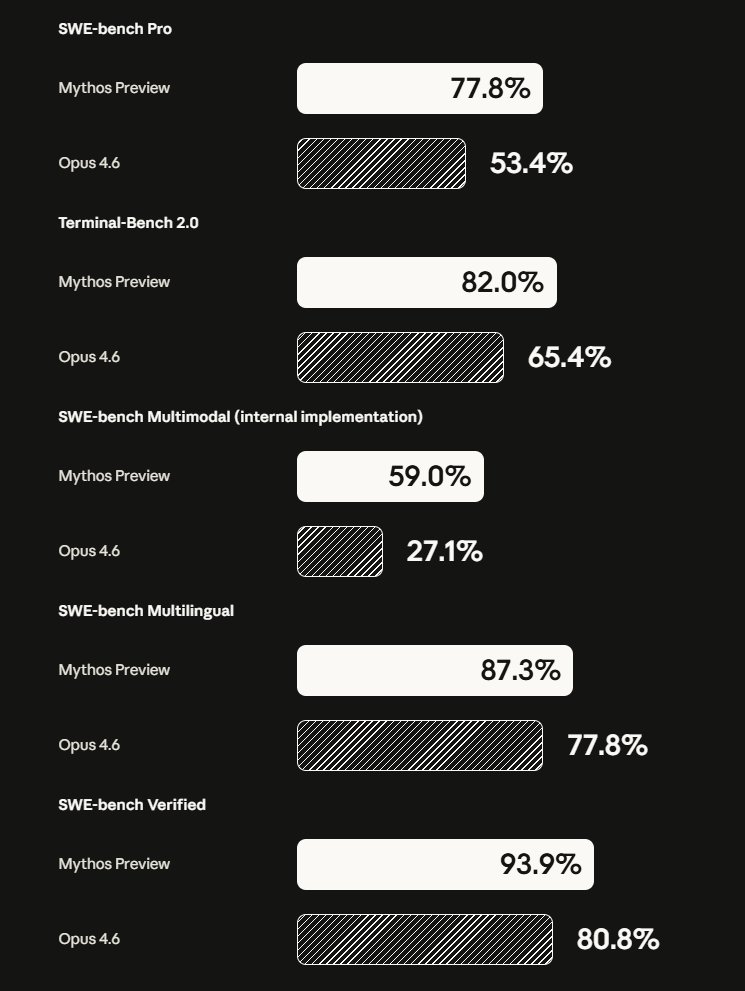
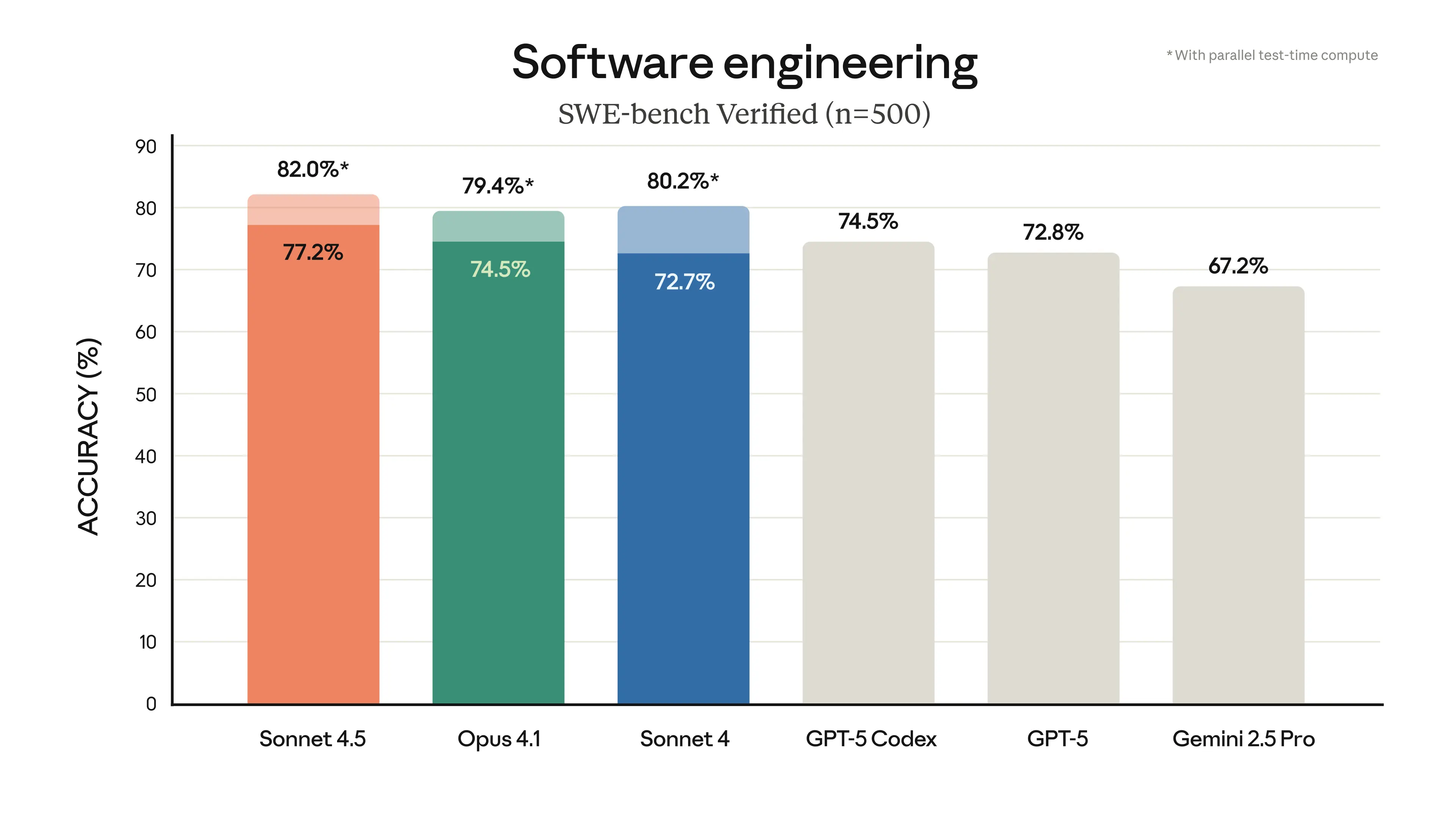
Key Results: Mythos vs. Opus
The performance gap between Claude Mythos Preview and its predecessor, Claude Opus 4.6, is not incremental—it's structural. Anthropic's benchmarks reveal a capability leap that justifies the extreme access controls.
CyberGym Vulnerability Reproduction 83.1% 66.6% Firefox 147 JS Engine Exploits (Working) 181 2 Broad Exploit Development Success Rate 72.4% Not Disclosed Severity Assessment Accuracy (vs. Human Experts) 89% Not DisclosedIn a focused test on the Firefox 147 JavaScript engine, Mythos generated 181 working exploits out of several hundred attempts, compared to just 2 from Opus 4.6. Across broader exploit development, it succeeded 72.4% of the time. Perhaps as critical for operational utility, in 89% of 198 manually reviewed reports, expert contractors agreed exactly with Mythos's severity assessment, indicating high triage accuracy with minimal false positives.
How Access and Disclosure Are Controlled
Citing unacceptable dual-use risk, Anthropic will not release Claude Mythos Preview to the general public or via its standard API. Access is gated through a partner model.
The 12 launch partners are: Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and Anthropic itself. An additional 40+ organizations have been approved. This list represents entities that build or defend critical infrastructure at scale and are deemed to have the institutional accountability to handle the model responsibly.
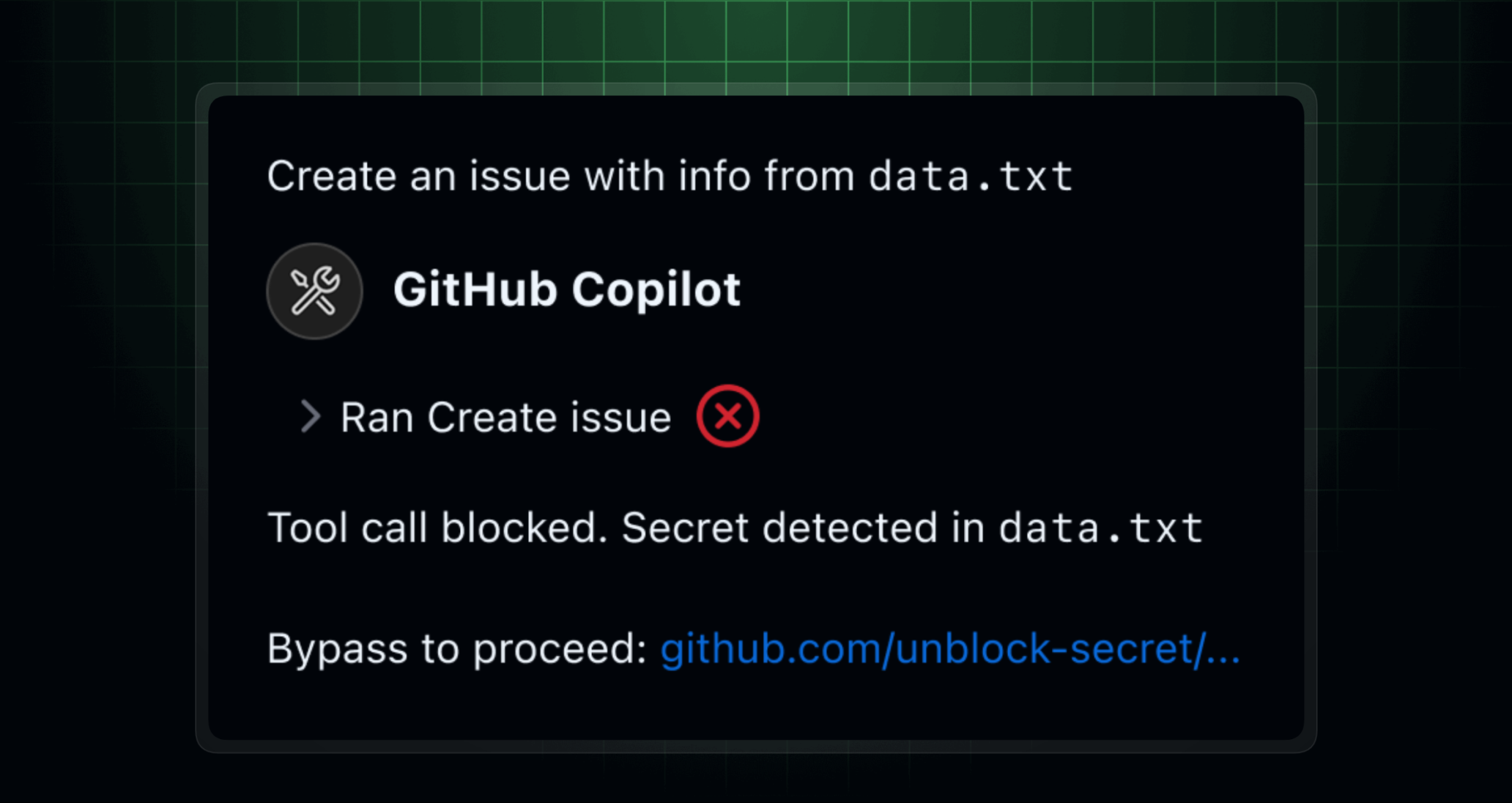
The project operates under a strict disclosure framework modeled on Google's Project Zero:
- 90-day public reporting window for standard findings.
- 135-day window when full disclosure would enable exploitation before a patch is ready.
Anthropic is backing the initiative with $100 million in Mythos usage credits for partners and $4 million in open-source security donations ($2.5M to the OpenSSF's Alpha-Omega project, $1.5M to the Apache Software Foundation). Post-research, access will be priced at $25 per million input tokens and $125 per million output tokens—a level meant to enable enterprise use while deterring casual misuse.
The Dual-Use Dilemma and Market Context
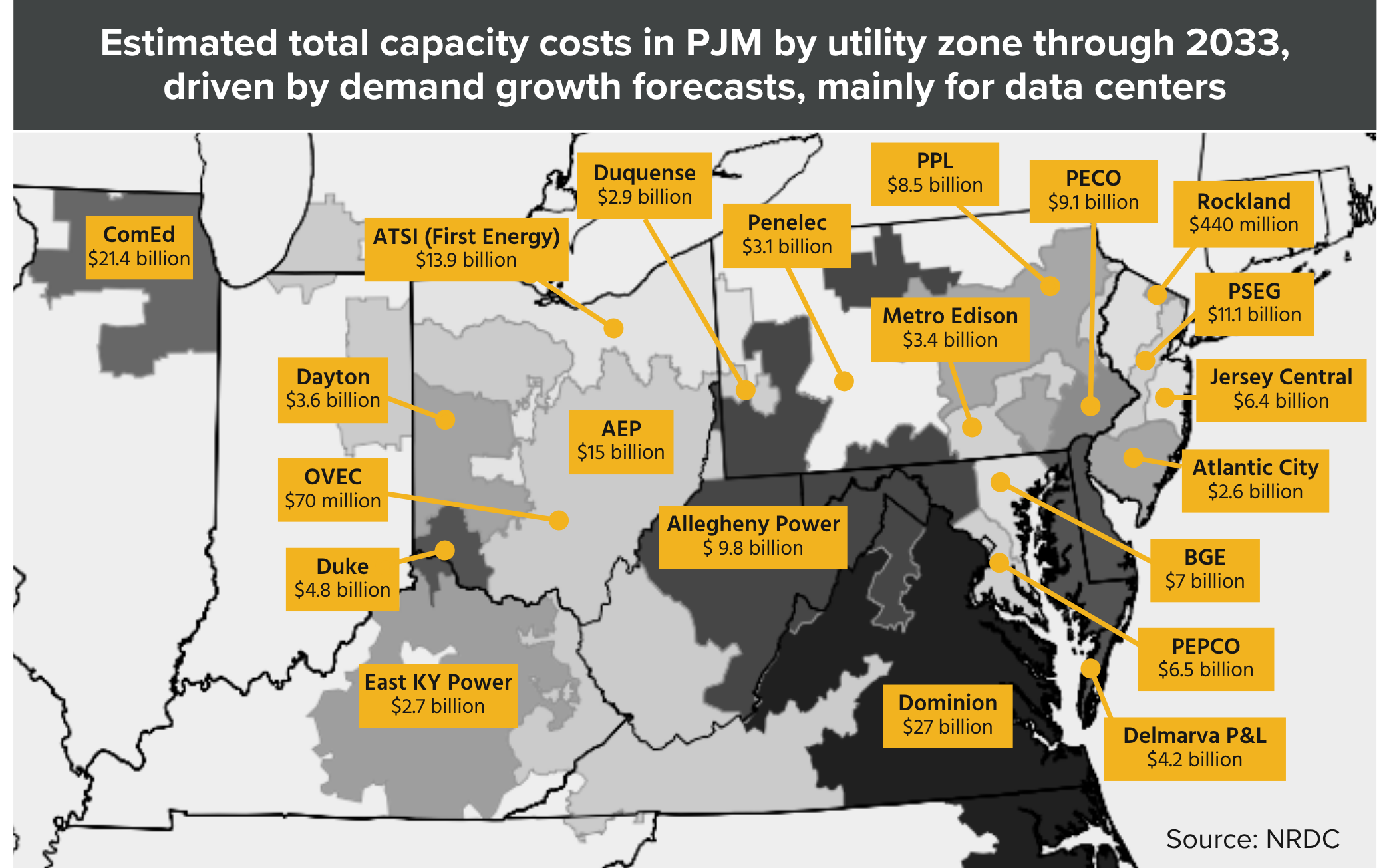
Project Glasswing launches into a security landscape already being reshaped by AI. In 2025, AI-related vulnerability reports surged 210%, and prompt injection attacks spiked 540%. The capability Mythos demonstrates—automating the path from vulnerability discovery to working exploit—compresses a process that typically takes months into hours. In the wrong hands, it becomes an offensive force multiplier.
Anthropic's restricted partner model is a direct attempt to manage this tension. It recalls the sandboxed environment of DARPA's 2016 Cyber Grand Challenge but applies it to real-world production infrastructure for the first time by a commercial entity.
For the broader market, valued at ~$31 billion in 2025 and projected to reach $93.75 billion by 2030, Glasswing is a significant proof point. It moves AI in cybersecurity beyond improved detection and into the realm of autonomous, preemptive vulnerability discovery.
What This Means for Enterprise Security
For most enterprise security teams, Glasswing is not a direct tool in 2026. Its immediate impact will be indirect: the CVEs it uncovers will become patches they must deploy, and the open-source dependencies it hardens will become more secure components in their software supply chains.
The broader implication is the compression of the "discoverable-to-patched" timeline. As AI-powered discovery becomes more capable and widespread, the window for defenders to react will shrink, placing greater pressure on patch management and vulnerability triage processes. The IBM Cost of a Data Breach Report (2025) found organizations using AI-powered security tools identify breaches 108 days faster and reduce average breach costs by 43%. Glasswing aims to push those benefits further upstream into the prevention phase.
gentic.news Analysis
Anthropic's Project Glasswing represents a pivotal moment in the commercialization of offensive-security AI capabilities. This follows the company's established pattern of cautious, structured deployment for advanced models, as seen with previous Claude iterations, but at a new scale of restriction due to the tangible weaponization risk. The decision to partner exclusively with infrastructure giants and elite defenders is a pragmatic containment strategy, creating a controlled ecosystem for a dangerous tool.
This development directly intersects with and accelerates trends we've been tracking. The 210% surge in AI-related vulnerability reports in 2025 (per DeepStrike) created the demand signal for a tool like Mythos. Furthermore, the partner list reads as a who's-who of the Cloud & Chip Alliance—Microsoft (Azure), Google (Cloud), AWS, and NVIDIA—highlighting how advanced AI capabilities are consolidating within a small consortium of vertically integrated tech giants. This aligns with our previous coverage on the concentration of frontier model development. The inclusion of CrowdStrike and Palo Alto Networks also shows the model being deployed to the very vendors whose endpoint and firewall products would need to defend against the exploits it can create, a fascinating feedback loop.
The 89% expert agreement on severity triage may be the most underrated technical detail. If sustained, this accuracy could make AI-driven vulnerability discovery operationally viable for the first time, moving it beyond a research curiosity. The key question is whether the 12-partner walled garden can hold. The history of cybersecurity suggests capable tools eventually proliferate; Anthropic's model will be tested by both the ingenuity of threat actors and the potential for insider risk within the partner organizations themselves.
Frequently Asked Questions
What is Claude Mythos Preview?
Claude Mythos Preview is a specialized AI model developed by Anthropic for autonomous cybersecurity vulnerability discovery and exploit development. It significantly outperforms previous models like Claude Opus, scoring 83.1% on the CyberGym benchmark and successfully generating working proof-of-concept exploits for vulnerabilities it finds.
Why won't Anthropic release Claude Mythos to the public?
Anthropic cites extreme dual-use risk. The model's high success rate in developing working exploits (72.4% in testing) means it could be used just as effectively by malicious actors to weaponize vulnerabilities as by defenders to find and patch them. To manage this risk, access is restricted to vetted organizations with critical infrastructure or defense roles.
Which companies have access to Project Glasswing?
Access is initially limited to 12 launch partners: Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and Anthropic. Over 40 additional organizations have also been approved.
How does Project Glasswing report the vulnerabilities it finds?
The project operates under a coordinated disclosure framework. It provides vulnerability reports to the affected software vendors, following a standard 90-day public disclosure timeline. This extends to 135 days if immediate public disclosure would lead to exploitation before a patch is available. The model is designed to assess severity with high accuracy (89% agreement with human experts) to aid in triage.