What Was Leaked — And Why It Matters to Developers
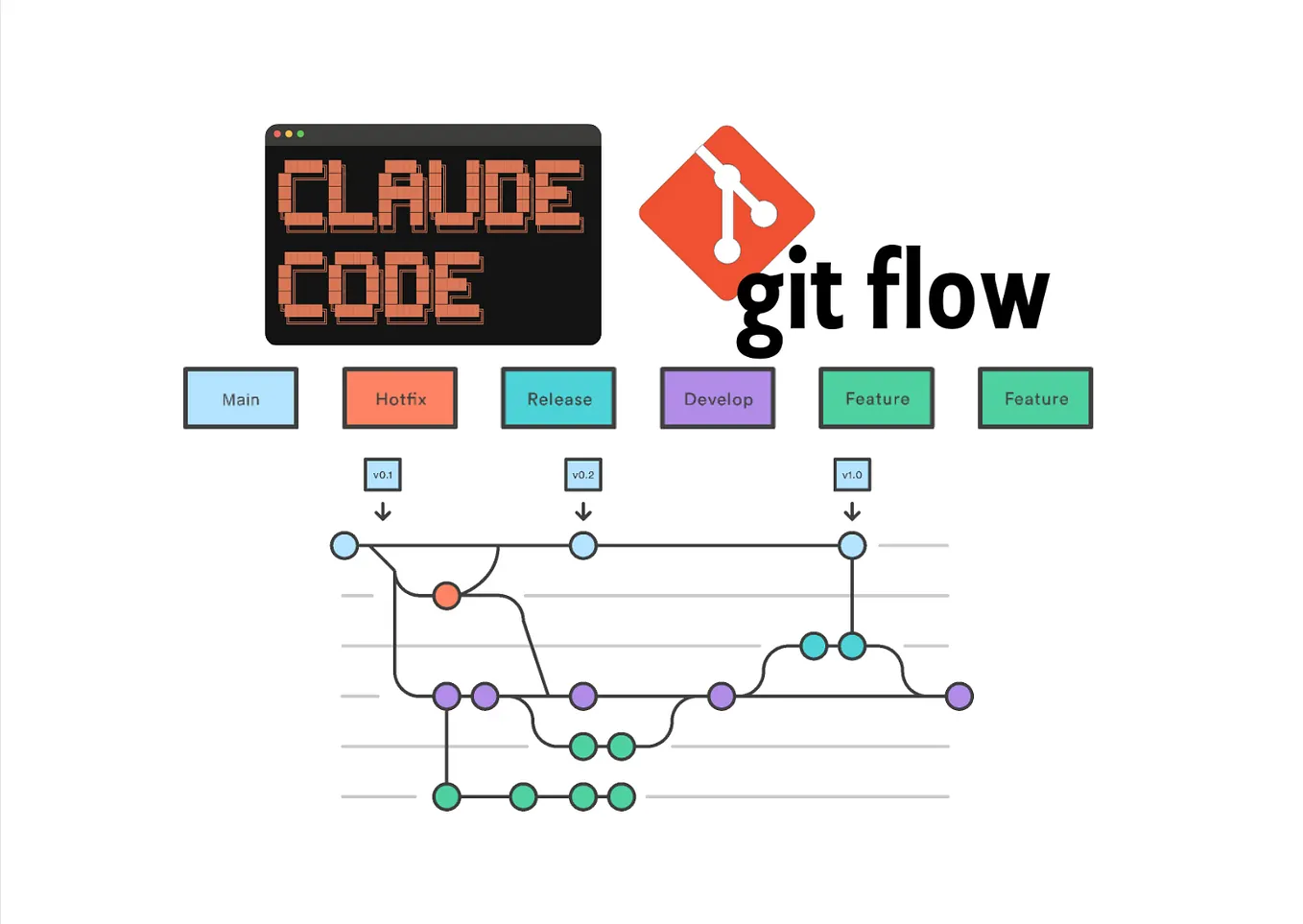
In late March 2026, Claude Code's full TypeScript implementation was exposed through what appears to be an inadvertent package distribution. This wasn't a model weights breach—the Claude model itself remains proprietary. What leaked was the engineering architecture that makes Claude Code work: the patterns, prompts, and safety systems that turn a language model into a reliable coding agent.
For developers using Claude Code daily, this leak provides unprecedented visibility into how Anthropic's team built one of the most sophisticated AI coding agents available. You're not just using the tool—you can now study exactly how it works under the hood.
Key Patterns You Can Learn From
The leaked code reveals several production-grade patterns that are directly applicable to developers building their own agents or customizing Claude Code workflows:
1. Multi-Step Tool Orchestration
The source shows how Claude Code manages complex tool-calling workflows. Instead of simple one-off commands, it implements stateful orchestration where tools can depend on previous outputs, handle partial failures gracefully, and maintain context across multiple operations.
This explains why Claude Code feels so reliable when you ask it to "refactor this entire module"—it's not just making sequential calls but managing a workflow with error recovery built in.
2. Context Window Management
One of the most valuable insights is how Claude Code handles the token limit. The leaked code shows sophisticated context pruning strategies—it doesn't just truncate but intelligently summarizes or removes less relevant parts of the conversation while preserving critical information.
You can apply similar strategies in your own CLAUDE.md files by explicitly marking which sections should be prioritized for retention versus which can be summarized.
3. Security and Sandboxing Architecture
The leak reveals how Claude Code isolates file-system access, validates tool inputs to prevent prompt injection, and implements permission hierarchies. This is particularly relevant for developers using Claude Code with sensitive codebases or in production environments.
Look for patterns around:
- Input validation before tool execution
- Path sanitization for file operations
- Permission escalation controls for different operations
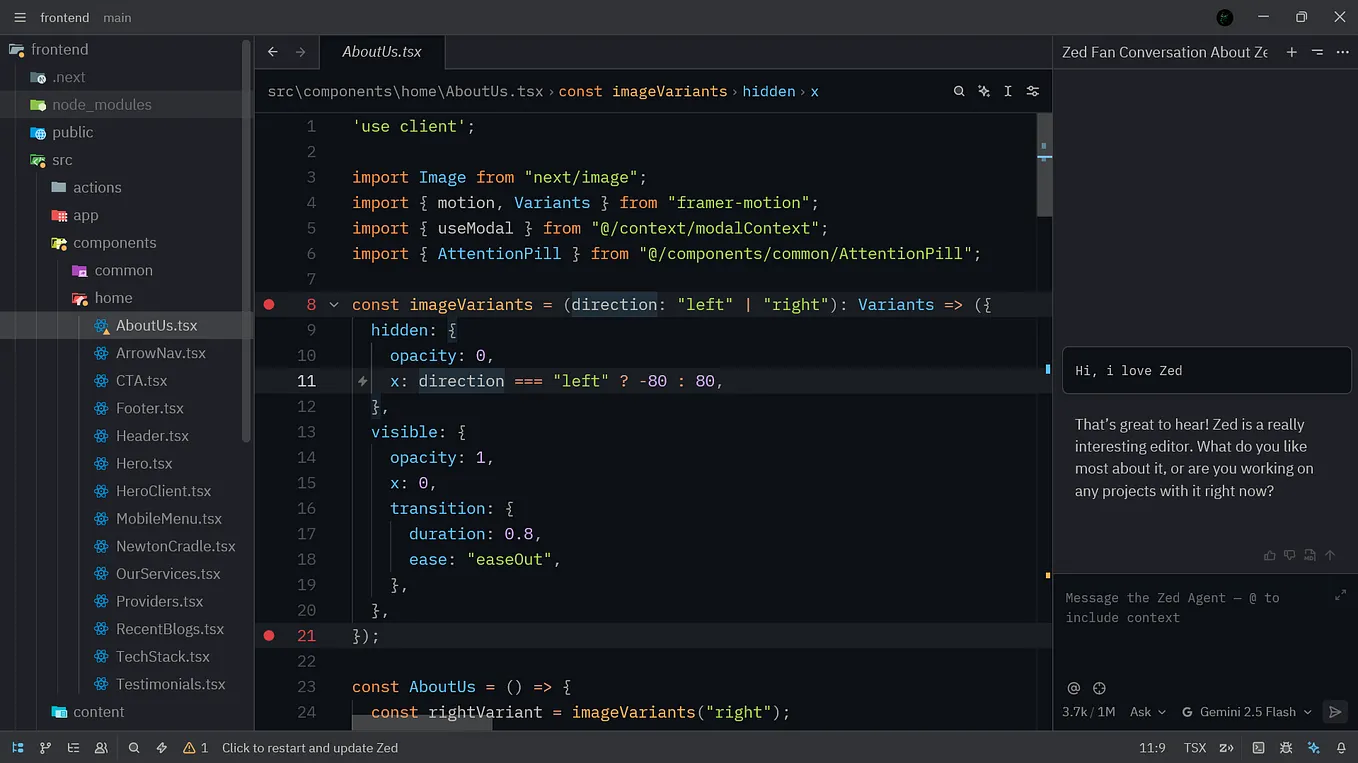
4. Terminal UI and Developer Experience
The CLI interface patterns are fully exposed. This includes:
- Progress indicators for long-running operations
- Error presentation that's actually helpful
- Interactive confirmation flows
- Output formatting that works across different terminal environments
What This Means for Your Claude Code Usage
While you can't (and shouldn't) use the leaked code directly, you can study the architectural patterns to improve your own workflows:
Better CLAUDE.md Files
Understanding Claude Code's internal prompt structure helps you write more effective CLAUDE.md files. The leak shows that Claude Code uses hierarchical prompting—system-level instructions, followed by project-specific context, followed by task-specific guidance.
Try structuring your CLAUDE.md similarly:
# System-level constraints and safety rules
# Project architecture and patterns
# Current task context and requirements
# Output formatting preferences
Improved Error Handling
Study how Claude Code recovers from tool failures. You'll notice it doesn't just retry—it analyzes why the failure occurred, adjusts its approach, and sometimes provides alternative solutions. You can prompt Claude Code to use similar strategies:
When you encounter an error:
1. First, analyze why it failed
2. Check for common solutions
3. If stuck, suggest alternative approaches
4. Never get stuck in retry loops
Security Best Practices
The sandboxing patterns are particularly valuable for enterprise users. While you can't modify Claude Code's security layer, you can implement similar protections in your development environment:
- Use Docker containers for Claude Code operations
- Implement file permission boundaries
- Validate all generated code before execution
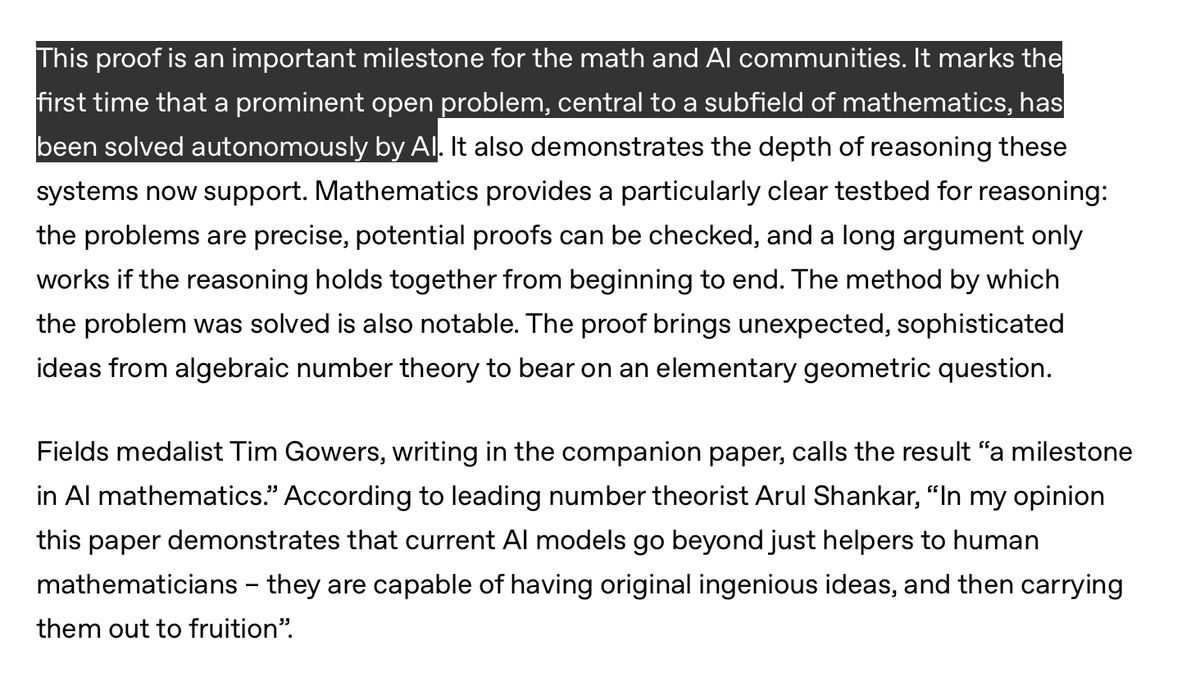
The Bigger Picture for AI Development Tools
This leak accelerates a trend we've been tracking: the democratization of agent engineering. Just as open-source models like DeepSeek have made powerful AI accessible, leaked production architectures make sophisticated agent patterns available to everyone.
For Claude Code users specifically, this means:
- Better understanding of limitations—you now know exactly where the guardrails are
- More effective prompting—you can align your requests with the underlying architecture
- Improved integration patterns—you can build complementary tools that work with Claude Code's strengths
What You Should Do Next
- Don't download or use the leaked code—it's proprietary and using it could have legal implications
- Do study the architectural patterns discussed in analysis articles (like this one)
- Apply the learnings to your workflows through better prompting and environment setup
- Watch for official updates—Anthropic will likely respond with new features or security improvements
The most immediate takeaway: Claude Code's reliability comes from sophisticated engineering patterns that you can now understand and, to some extent, emulate in your own AI-assisted development workflows.