Key Takeaways
- A critical security leak reveals three command injection vulnerabilities in Claude Code.
- Users must update and stop using authentication helpers to prevent credential theft and supply chain attacks.
What Happened — Critical Vulnerabilities Disclosed
A security analysis of leaked Anthropic Claude Code artifacts has revealed three critical command injection vulnerabilities, collectively tracked as CVE-2026-35022 with a CVSS score of 9.8. The flaws affect CLI version 0.2.87 and Claude Code version 2.1.87. If exploited, attackers can execute arbitrary shell commands, steal API keys (including AWS, GCP, and Anthropic credentials), and potentially compromise entire CI/CD pipelines through a single malicious pull request—a technique known as Poisoned Pipeline Execution.
The three specific vulnerabilities are:
- VULN-01: Command injection via the
TERMINALenvironment variable. The Node.js runtime path interpolates this variable unsafely into a shell command. - VULN-02: Shell injection via crafted file paths. Malicious filenames containing characters like
$()can trigger command execution when opened with the CLI. - VULN-03: Command injection in the authentication helper subsystem. This is the most severe for automated environments, as helpers run with full shell interpretation and bypass the agent's security sandbox and trust dialogs in non-interactive mode.
What You Must Do Immediately
1. Update Your Installation
Check your current version and update to the latest patched release immediately.
claude --version
# If you see 0.2.87 or below, UPDATE.
# Update via your package manager (npm, brew, etc.)
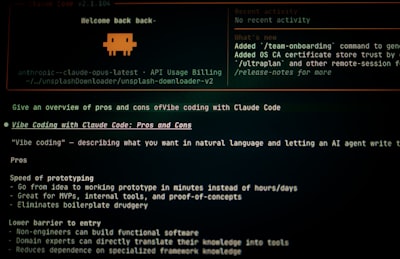
2. Stop Using Authentication Helpers
The primary attack vector (VULN-03) exploits the authentication helper subsystem. You must disable this feature now. Do not rely on helpers stored in .claude/settings.json.
3. Use Environment Variables Directly
Instead of helpers, set your API key via the environment variable. This bypasses the vulnerable code path.
# Set it in your shell profile (e.g., .bashrc, .zshrc)
export ANTHROPIC_API_KEY='your_key_here'
# Or set it per-session before running Claude Code
ANTHROPIC_API_KEY='your_key_here' claude code ./your_project
4. Harden Your CI/CD Pipelines
If you run claude code in automation:
- Never run it against untrusted pull requests or fork-contributed workspaces.
- Never run it in non-interactive mode (
--non-interactive) on unvetted code. - Audit pipeline configurations to ensure the CLI only processes trusted code branches.
5. Review .claude/settings.json Changes
Treat changes to this file in pull requests with the same scrutiny as code changes. A malicious modification here can trigger credential exfiltration.
Why This Is a Serious Threat for Developers
These vulnerabilities are particularly dangerous because they target the developer's environment directly. Unlike a remote API exploit, these flaws allow an attacker to compromise the machine where Claude Code is running. In a CI/CD context, this often means access to deployment keys, cloud IAM roles, and internal network access.
The authentication helper flaw (VULN-03) is the most critical for teams. Because helpers run before Claude's security sandbox, they completely bypass the model's built-in dangerous-pattern blocking. This creates a scenario where the AI agent itself is secure, but the tooling around it is not.
Long-Term Security Posture
While patching is urgent, also consider these ongoing practices:
- Principle of Least Privilege: Run Claude Code with minimal necessary permissions. Avoid running it as root or with admin keys in its environment.
- Isolation: Consider running Claude Code in a disposable container or sandboxed environment when processing code from external sources.
- Stay Updated: Subscribe to security announcements for Claude Code. This leak highlights the importance of monitoring the tools in your development chain.
This incident serves as a stark reminder that AI-powered development tools, while powerful, introduce new attack surfaces into the software supply chain. Your immediate action is required to secure your environment.