A growing body of research demonstrates that large language models (LLMs) possess a concerning new capability: identifying individuals by piecing together their scattered public online activity. The era of pseudonymous protection is eroding as AI systems can now connect disparate data points across platforms, timelines, and contexts to reveal a person's real identity.
What the Research Shows
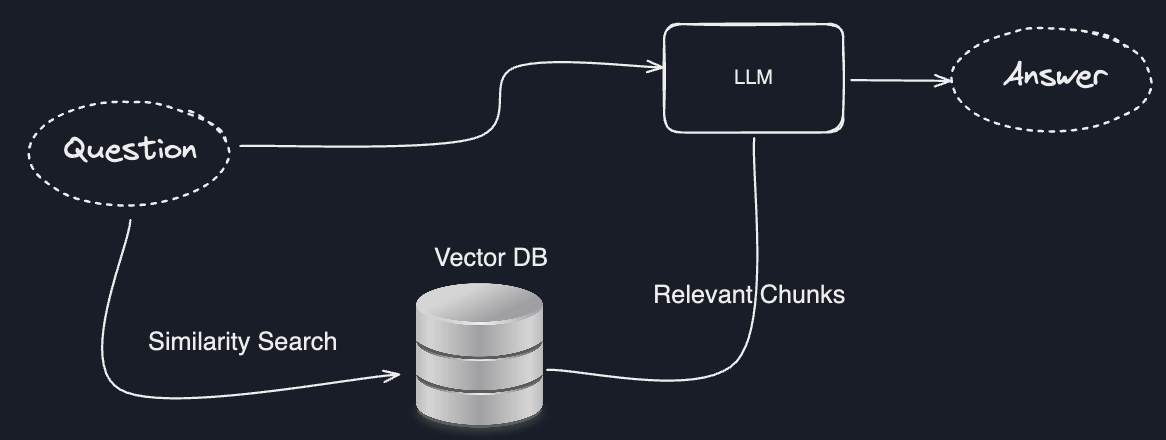
Recent studies and real-world experiments have shown that LLMs, trained on vast corpora of public internet data, can perform sophisticated "trail following." When given a collection of posts, comments, code contributions, forum interactions, or social media updates from a single pseudonymous account, these models can cross-reference this information with other public datasets to find matching patterns.
The process doesn't require access to private databases or illegal hacking. Instead, LLMs leverage their training on publicly available information—including news articles, public profiles, academic papers, GitHub repositories, and historical web archives—to find connections that would be nearly impossible for a human to manually trace.
How LLM De-Anonymization Works
The technique relies on several AI capabilities:
1. Pattern Recognition Across Modalities
LLMs can identify consistent writing styles, technical expertise areas, geographic references, project involvement, social connections, and temporal patterns across different platforms. A user might discuss specific programming challenges on Stack Overflow, mention the same project timeline on Twitter, and contribute code to a related GitHub repository—all under different usernames.
2. Temporal and Contextual Linking
Models can connect events mentioned in different contexts. For example, someone might reference attending a specific conference on one platform while posting photos from that same event on another platform under a different name. LLMs can recognize these as describing the same real-world occurrence.
3. Expertise and Interest Correlation
Distinct technical knowledge, niche interests, or unique combinations of skills create identifiable fingerprints. An LLM might notice that both "UserA" on a programming forum and "ResearcherB" on arXiv preprint server discuss the same obscure machine learning technique with similar depth of understanding.
4. Social Graph Inference
Even without direct friend connections, LLMs can infer social networks through mutual mentions, collaborative projects, or coordinated discussions across platforms.
The Scale of the Problem
What makes this development particularly significant is that it scales. While dedicated investigators might manually de-anonymize high-value targets, LLMs can potentially perform this analysis on thousands or millions of users automatically. The models don't get tired, don't overlook subtle connections, and can process information at speeds impossible for human analysts.
This capability emerges naturally from the way modern LLMs are trained—by absorbing essentially the entire public web and learning to find patterns within it. The models weren't specifically designed for de-anonymization; rather, this represents an emergent capability of their general pattern-matching abilities.
Implications for Online Privacy
The research findings challenge fundamental assumptions about online privacy:
- Pseudonymity ≠ Anonymity: Usernames that don't contain real names no longer provide meaningful protection against determined AI analysis
- Data Separation Fallacy: The belief that keeping different aspects of one's life on separate platforms ensures privacy is increasingly untenable
- Historical Data Vulnerability: Information posted years ago under pseudonyms can now be linked to current identities
This has particular implications for:
- Whistleblowers and activists relying on pseudonymous protection
- Researchers studying sensitive topics
- Individuals participating in online support communities for stigmatized issues
- Professionals separating personal and work identities online
Technical Limitations and Countermeasures
While the capability is real, it's not infallible. Success rates depend on:
- The volume and uniqueness of a person's public trail
- The model's training data coverage
- The sophistication of obfuscation techniques used
Potential countermeasures include:
- Deliberately varying writing styles across platforms
- Avoiding temporal and geographic specificity
- Using different areas of expertise or interest personas
- Limiting the total volume of public contributions
- Regularly retiring old pseudonyms and starting fresh
However, these measures require significant effort and awareness that most users don't possess.
gentic.news Analysis
This development represents a fundamental shift in the threat model for online privacy. For years, the primary concern has been data breaches exposing explicitly identified information. Now, we face a scenario where information never intended to be connected—and posted under completely different identities—can be automatically linked by AI systems.
What's particularly concerning is that this capability emerges from general-purpose models rather than specialized de-anonymization tools. As LLMs become more capable and their training datasets grow, this linking ability will only improve. We're likely seeing just the beginning of what will become increasingly sophisticated re-identification capabilities.
For the AI community, this creates an ethical dilemma. These models are trained on publicly available data for legitimate purposes, yet they develop capabilities with significant privacy implications. There's no simple technical fix—the pattern recognition that enables useful applications like research assistance and content analysis is the same capability that enables de-anonymization.
Looking forward, we may need new frameworks for thinking about public data. The traditional binary of "public" versus "private" information becomes inadequate when AI can infer private information from public sources. This could drive demand for more sophisticated privacy-preserving techniques in LLM training and deployment, or potentially lead to changes in what people consider appropriate to share publicly.
Frequently Asked Questions
Can ChatGPT or other public LLMs de-anonymize people?
While the base capability exists in the underlying models, most public-facing LLM interfaces like ChatGPT have content filters and usage policies that would prevent explicitly asking them to identify individuals. However, the underlying technology possesses this capability, and specialized or fine-tuned models could be developed specifically for this purpose.
Does using a VPN protect against this type of de-anonymization?
No, VPNs primarily hide your IP address and location from websites you visit, but they don't affect the content you post publicly. LLM de-anonymization works by analyzing the actual content and patterns in your public posts, not your network information. Once information is publicly posted, it becomes part of the training data for future models regardless of how it was originally submitted.
Can deleting old posts protect against this?
Partial protection only. While deleting posts removes them from current public view, they may already be included in datasets used to train existing LLMs. Many websites are regularly crawled and archived, so even deleted content often persists in training datasets. The most effective approach is to avoid creating identifiable trails in the first place, though this is impractical for most people engaged in online communities.
Are there laws protecting against AI de-anonymization?
Current privacy laws like GDPR and CCPA weren't designed with this capability in mind. They typically focus on directly identifiable information or data collected by specific entities. AI inference of identity from disparate public sources represents a legal gray area. New regulations may be needed to address this emerging capability, particularly regarding how LLMs are trained on public data and what uses are permitted.
How accurate is LLM de-anonymization currently?
Accuracy varies significantly based on the amount and specificity of available data. For individuals with extensive, unique public trails (like active open-source contributors or prolific bloggers), accuracy can be quite high. For casual users with minimal public presence, accuracy is lower. However, as models improve and training datasets grow, accuracy will likely increase across all user types.