What Happened — A Supply Chain Attack Targeting AI Workflows
A critical supply chain attack hit the popular JavaScript HTTP client axios at version 1.14.1. The compromised package silently pulls in plain-crypto-js@4.2.1, an obfuscated Remote Access Trojan (RAT) dropper. While npm has pulled the malicious version, the window of exposure was significant—especially for developers using AI coding tools like Claude Code.
The attack specifically exploits the "vibe coding" pattern: letting Claude write code, running npm install without scrutiny, and trusting the AI's package selections. Attackers are targeting developers who scaffold projects with AI assistants and execute installs without reviewing package.json diffs.
What It Means For Claude Code Users — Your Workflow Is the Target
If you've used Claude Code for any JavaScript/Node.js project in the last 48 hours, you need to audit your dependencies immediately. The risk isn't just in new projects—Claude Code's ability to modify existing codebases means it could have updated axios to the compromised version during routine maintenance or feature additions.
This follows a concerning trend of AI-assisted development expanding attack surfaces. Just last week, Claude Code launched its Computer Use feature with app-level permissioning, giving the agent more autonomy—and more potential to execute malicious code if dependencies are compromised.
Check Your Machines — Right Now
Run these commands in any project directory where you've used Claude Code recently:
# Check for the malicious dependency in your lockfile
grep -r "plain-crypto-js" package-lock.json
grep -r "axios@1.14.1" package-lock.json
# Check for persistence artifacts on your system
# macOS
ls -la /library/caches/com.apple.act.mond
# Linux
ls /tmp/ld*
If you find axios@1.14.1 in your lockfile:
- Immediately roll back to
axios@1.14.0 - Rotate ALL credentials: AWS keys, API tokens, SSH keys, everything
- Assume your machine may be compromised
Update Your Claude Code Workflow — Add Security Gates
Modify your CLAUDE.md or project instructions to include dependency auditing steps. Here's a template to add:
## Security Protocol for Package Changes
Before running `npm install` or similar commands:
1. Always show me the exact `package.json` diff first
2. If adding/updating packages, include a brief security rationale
3. Never automatically install packages without explicit approval
4. After installation, run: `npm audit --audit-level=high`
For existing projects, add this to your Claude Code session:
/context Please audit all dependencies in this project for known vulnerabilities,
with special attention to axios versions. Show me the npm audit output.
Prevent Future Attacks — Pinning and Automation
- Pin your versions: Use
npm install axios@1.14.0 --save-exactto lock to specific versions - Automate checks: Add this to your pre-commit hooks or CI pipeline:
#!/bin/bash
# check-axios.sh
if grep -q "axios@1.14.1" package-lock.json; then
echo "CRITICAL: Compromised axios version detected"
exit 1
fi
- Use dependency monitoring: Tools like Socket.dev or Snyk can alert you to suspicious packages
The Bigger Picture — AI Trust Requires Verification
This incident highlights a fundamental tension in AI-assisted development: speed versus security. When Claude Code suggests adding a package, we're tempted to trust the recommendation. But AI models don't have real-time knowledge of package compromises—they're working with training data that's inherently outdated for security threats.
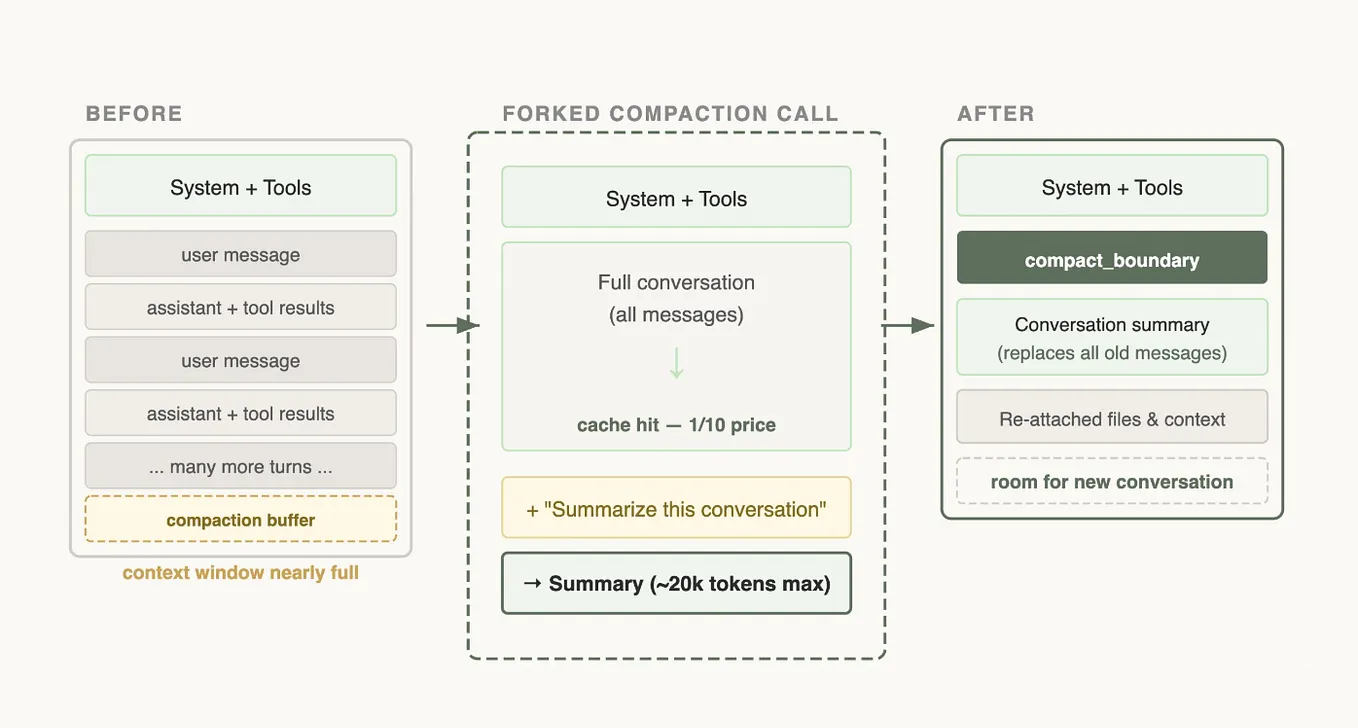
Your new rule: Never let Claude Code run npm install without showing you the package.json diff first. Use the /compact flag to see changes clearly, then manually verify before proceeding.
Sources for Verification
- Socket.dev analysis: https://socket.dev/blog/axios-npm-package-compromised
- Aikido.dev investigation: https://www.aikido.dev/blog/axios-npm-compromised-maintainer-hijacked-rat