The Problem: AI Agents Install Without Asking
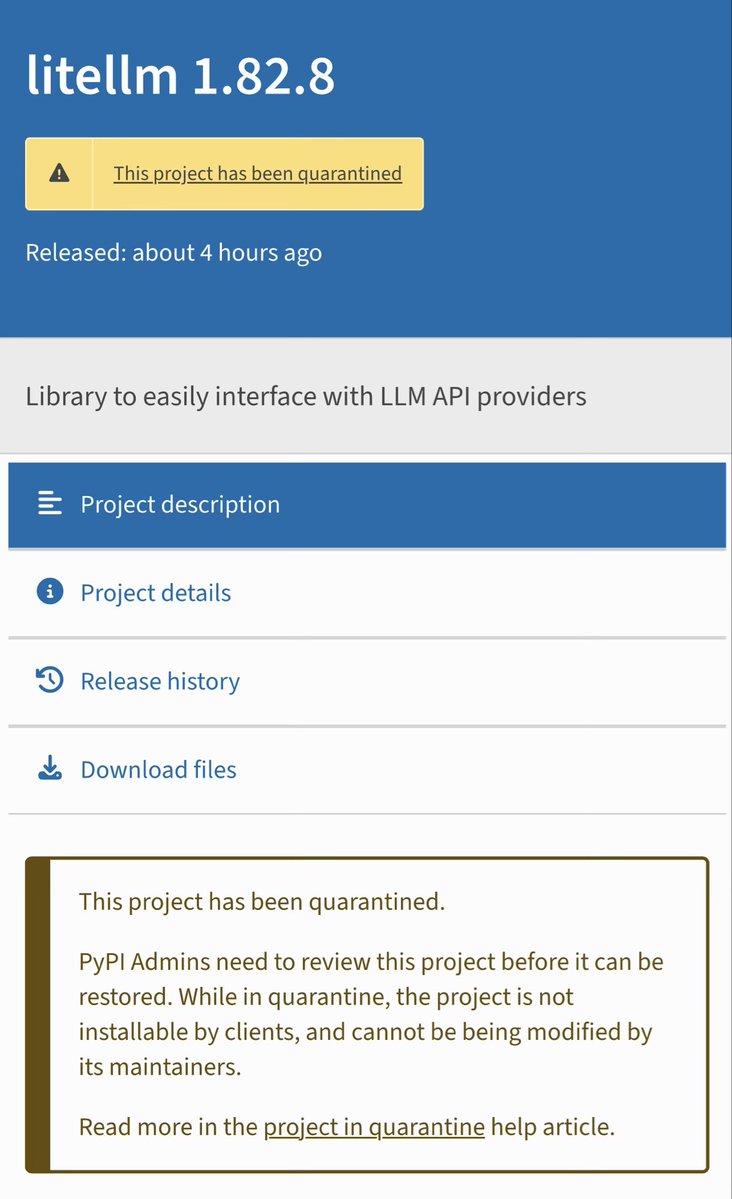
When you tell Claude Code to add a dependency, it runs npm install or pip install immediately. There's no safety check. Last week, axios@1.14.1 was hijacked on npm. Days before, litellm@1.82.8 on PyPI. Both were compromised versions published through hijacked maintainer accounts.
Claude Code would have installed both without hesitation. By the time you notice, the malicious code has already executed.
The Solution: attach-guard Plugin
attach-guard is an open-source Claude Code plugin that intercepts every package install command before execution. It evaluates packages against Socket.dev's supply chain risk data and blocks them if they fail security policies.

Critical distinction: This uses Claude Code's PreToolUse hooks, not skills or MCP servers. Hooks run automatically on every matching tool call—Claude cannot skip or override them. This is enforcement, not advice.
How It Works
When Claude runs npm install axios, attach-guard:
- Intercepts the command before it executes
- Scores the package via Socket.dev's API (malware detection, maintainer history, code changes)
- Blocks if it fails policy (malware, score below 50, published <48 hours ago)
- Rewrites to safe version when possible, doesn't just say "no"
Real examples from the developer:
npm install axios→ latest (1.14.1) scores 40/100 → blocked → rewrites toaxios@1.14.0(71/100)pip install litellm==1.82.8→ compromised → denied
What it catches:
- Known malware and compromised packages
- Packages published less than 48 hours ago (too new to trust)
- Low supply chain scores (below 50 = denied, 50-70 = flagged)
- Supports npm, pip, Go, and Cargo
Install in 2 Commands
claude plugin marketplace add attach-dev/attach-guard
claude plugin install attach-guard@attach-dev
During setup, it prompts for a Socket.dev API token (free tier available). The plugin is MIT licensed with no data collection.
Why This Matters Now
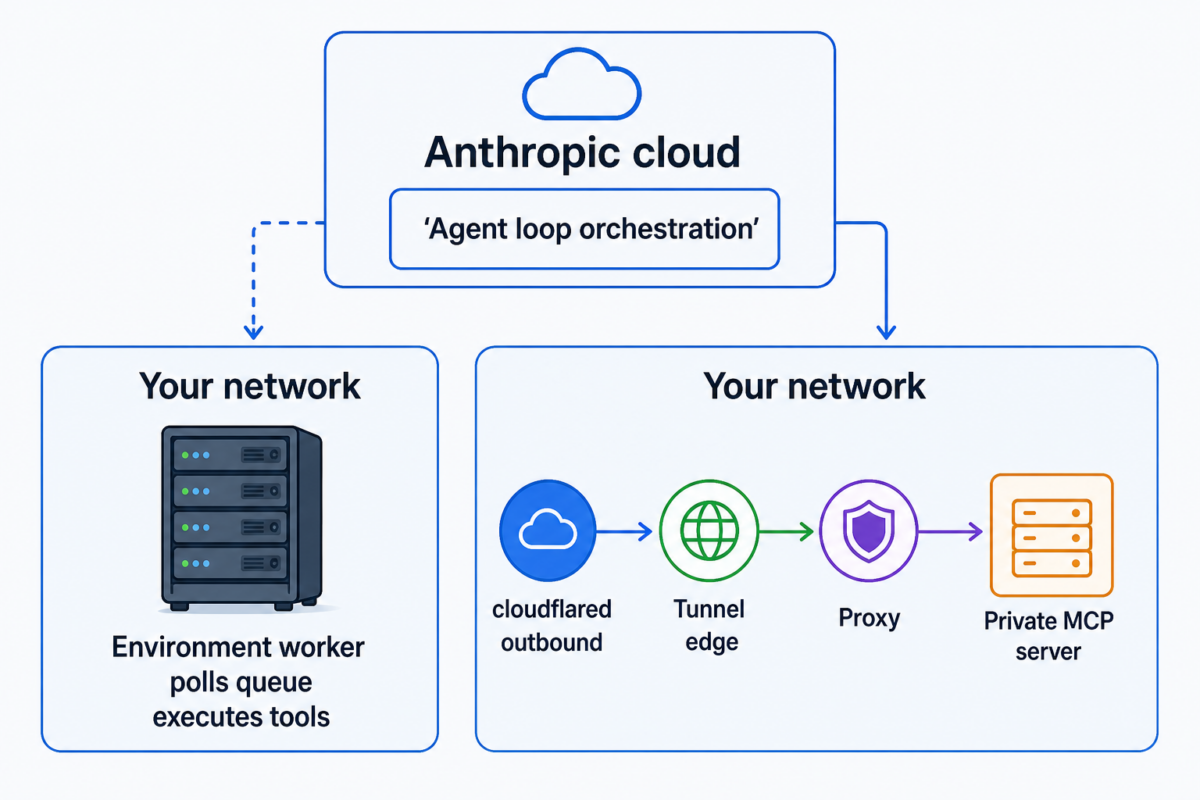
Supply chain attacks are increasing. AI coding agents like Claude Code execute commands autonomously, creating new attack surfaces. This follows Claude Code's recent Computer Use feature launch (March 30, 2026), which expanded app-level permissioning and potential attack vectors.
Without tools like attach-guard, you're trusting every package registry to be perfectly secure—which recent history proves isn't true.
Configuration Tips
After installation, you can customize policies in your Claude Code configuration:
- Adjust score thresholds (default: deny <50, flag 50-70)
- Change the "new package" window from 48 hours
- Enable/disable specific package managers
The plugin works silently in the background. You'll only see output when it blocks or flags something, keeping your workflow clean.
gentic.news Analysis
This plugin represents a critical security layer for Claude Code's autonomous execution model. It directly addresses the risk highlighted in our March 30 coverage of Claude Code's Computer Use feature, which expanded attack surfaces by granting app-level permissions.
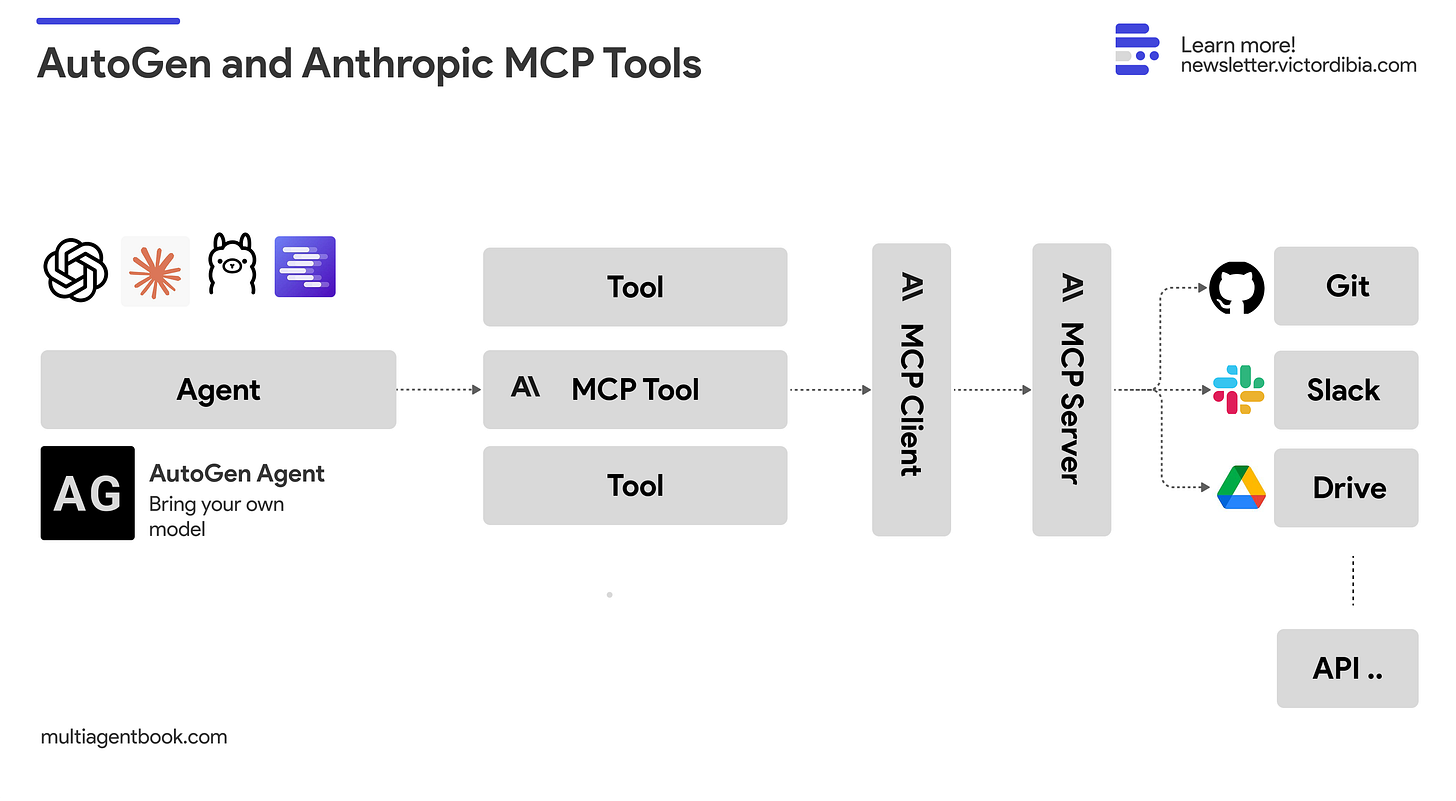
The use of PreToolUse hooks is significant—it ensures enforcement rather than advisory protection. This aligns with the broader trend of Model Context Protocol (MCP) integration (mentioned in 77 prior articles), where Claude Code's architecture connects to various security and tooling backends.
Interestingly, this security-focused development comes amid increased Claude Code activity (65 articles this week, 446 total), showing the ecosystem maturing from pure capability to responsible deployment. It also follows our April 3 article about ContextZip reducing token waste—both are examples of developers building essential utilities atop Claude Code's extensible platform.
As AI agents handle more critical operations, expect more security-focused plugins like attach-guard to emerge. This isn't just about preventing malware; it's about making autonomous coding tools production-ready for enterprise environments where supply chain security is non-negotiable.