On May 21, 2025, the Python Package Index (PyPI) officially marked the litellm package as "quarantined," a critical security action taken in response to a confirmed supply chain attack. The move, highlighted by developer Simon Willison, prevents the automatic installation of a compromised version of the popular AI integration library via standard package managers like pip.
What Happened
The litellm package, a widely used open-source library for standardizing calls to various large language model APIs (including OpenAI, Anthropic, and open-source models), was compromised. An attacker gained control of the PyPI account belonging to the project's maintainer and uploaded a malicious version (reportedly 1.38.2).
This malicious package contained obfuscated code designed to steal sensitive environment variables—such as API keys, database credentials, and cloud access secrets—from the systems where it was installed. The stolen data was then exfiltrated to a remote server controlled by the attacker.
PyPI's quarantine is a reactive security measure that blocks the package from being installed through normal channels. When a package is quarantined:
- Direct installation via
pip install litellmwill fail. - The package page on pypi.org displays a prominent warning.
- The package's files remain downloadable for forensic analysis, but automated tools are blocked from fetching them as dependencies.
Context: A Growing Threat to AI Infrastructure
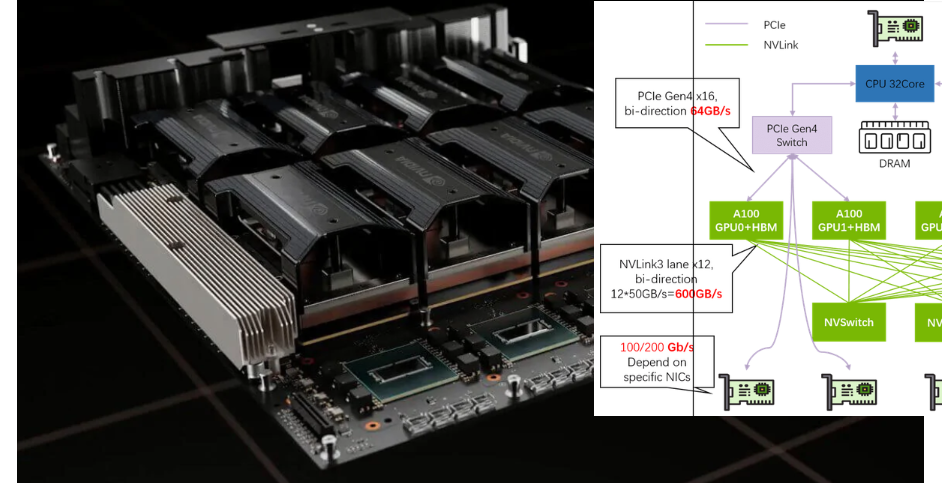
Supply chain attacks targeting open-source repositories like PyPI, npm, and RubyGems have become increasingly common and sophisticated. AI and ML infrastructure has emerged as a high-value target due to the sensitive credentials and computational resources involved.
LiteLLM's role as a unified proxy and router for multiple LLM APIs makes it a particularly attractive target. A single breach can potentially expose keys for OpenAI, Anthropic, Google Vertex AI, Azure OpenAI, and numerous self-hosted model endpoints, granting an attacker both stolen credentials and billable usage.
This incident follows a pattern of recent attacks against AI-adjacent tooling. It underscores the critical dependency the modern AI development stack has on a fragile ecosystem of open-source maintainers, where a single compromised account can have cascading security implications.
Immediate Actions for Developers and Teams
If you have deployed applications using LiteLLM, you must take immediate steps:
- Check Your Installed Version: Run
pip list | grep litellmor check yourrequirements.txt/pyproject.tomlfiles. Version 1.38.2 is confirmed malicious. - Assume Compromise: If you installed
litellm==1.38.2, you must assume your environment variables were exfiltrated. This is not a theoretical risk; the code was actively stealing data. - Rotate All Exposed Credentials: Immediately rotate every API key, database password, and secret that was stored in environment variables accessible by your Python process. This includes LLM provider keys (OpenAI, Anthropic, etc.), cloud provider keys (AWS, GCP, Azure), and database connections.
- Pin to a Known-Safe Version: Until a new, verified release is published by the legitimate maintainers, pin your dependency to a last-known safe version (e.g.,
litellm==1.38.1). Do not rely on thelatesttag. - Monitor for Official Updates: Follow the official LiteLLM GitHub repository for updates from the core team on remediation and a secure path forward.
The quarantine is a necessary stopgap, but it is not a permanent solution. The long-term integrity of the package depends on the maintainers regaining control of their PyPI account, conducting a security audit, and re-establishing a trusted release pipeline, potentially with multi-factor authentication and additional publishing safeguards.
gentic.news Analysis
This LiteLLM breach is not an isolated event but a symptom of a systemic vulnerability in the AI toolchain. As we covered in our analysis of the "LangChain Expression Language (LCEL) vulnerabilities" last year, abstraction layers that unify access to multiple LLM providers create single points of failure. LiteLLM takes this a step further by being a runtime proxy, making it a dependency in live production environments rather than just a development framework. The economic incentive for attackers is clear: a successful compromise offers a rich harvest of high-value API keys that can be resold or used for fraudulent compute consumption.
The attack vector—PyPI account takeover—is also a recurring theme. It mirrors the 2023 breach of the ctx package, where a maintainer's account was compromised to distribute information-stealing malware. This pattern highlights the inadequacy of password-only authentication for critical infrastructure packages. PyPI has made strides with mandatory 2FA for top projects, but broader enforcement and the use of API tokens or trusted publishers for all packages with significant download counts is becoming an urgent necessity.
For AI engineering teams, this incident mandates a shift in dependency management strategy. Blind trust in pip install is no longer viable. Strategies must now include:
- Vendor-ing Dependencies: Hosting approved package versions on internal artifact repositories.
- Automated SCA & SBOM: Implementing software composition analysis tools to flag suspicious package updates, like unexpected maintainer changes or obfuscated code.
- Credential Isolation: Using secret management services that inject credentials at runtime, preventing them from being accessible via
os.environto the application layer, even if the application code is compromised.
The quarantine is a effective containment tactic, but the broader lesson is that the open-source packages forming the plumbing of the AI revolution are themselves vulnerable infrastructure. Their security is now a direct component of AI system security.
Frequently Asked Questions
What does it mean that PyPI "quarantined" the LiteLLM package?
Quarantining is a security action taken by PyPI administrators that blocks the automatic installation of a package. When a package is quarantined, tools like pip cannot install it directly, and its page on pypi.org displays a major warning. The files remain available for manual download for investigation, but the package is removed from the normal distribution network to prevent further automatic infections.
I have LiteLLM in my project. What should I do immediately?
First, identify the installed version. If it is 1.38.2, you must act under the assumption that all environment variables on that system have been stolen. Your immediate priority is to rotate every exposed credential: all LLM API keys (OpenAI, Anthropic, etc.), cloud access keys, and database passwords. Then, pin your dependency to a known-safe version like 1.38.1 and monitor the official LiteLLM GitHub repository for guidance from the legitimate maintainers.
How can I prevent this from happening to my project in the future?
You cannot prevent attacks on upstream packages, but you can mitigate the impact. Implement a defense-in-depth strategy: use an internal artifact repository to vet and host dependencies, employ software composition analysis (SCA) tools to scan for vulnerabilities and malicious code in your supply chain, and most critically, avoid storing sensitive credentials in environment variables accessible to your application code. Use a dedicated secrets manager that injects them at runtime.
Is the LiteLLM project itself malicious now?
No, the LiteLLM project is the victim of an account takeover. The malicious code was uploaded by an attacker who compromised the maintainer's PyPI account. The legitimate maintainers, BerriAI, are working to regain control and restore security. The open-source code on GitHub is likely still safe, but the integrity of the PyPI release pipeline has been breached.