Claude Code autonomously stopped a 13 million requests-per-minute DDoS attack on BridgeMind's API in under 10 minutes. The incident, reported by @bcherny on X, marks a notable real-world demonstration of an AI coding agent handling live infrastructure threats.
Key facts
- 13 million requests per minute hit BridgeMind's API.
- Claude Code stopped the DDoS in under 10 minutes.
- Reported by @bcherny on X on an unspecified date.
- BridgeMind AI is the affected company.
- Anthropic has not confirmed general availability.
Claude Code just stopped a DDoS attack on BridgeMind in under 10 minutes, according to a post by @bcherny on X, retweeting BridgeMind AI's account. The attack hit 13 million requests per minute, a scale that would overwhelm most manual mitigation efforts and many automated Web Application Firewall (WAF) rulesets.
What happened
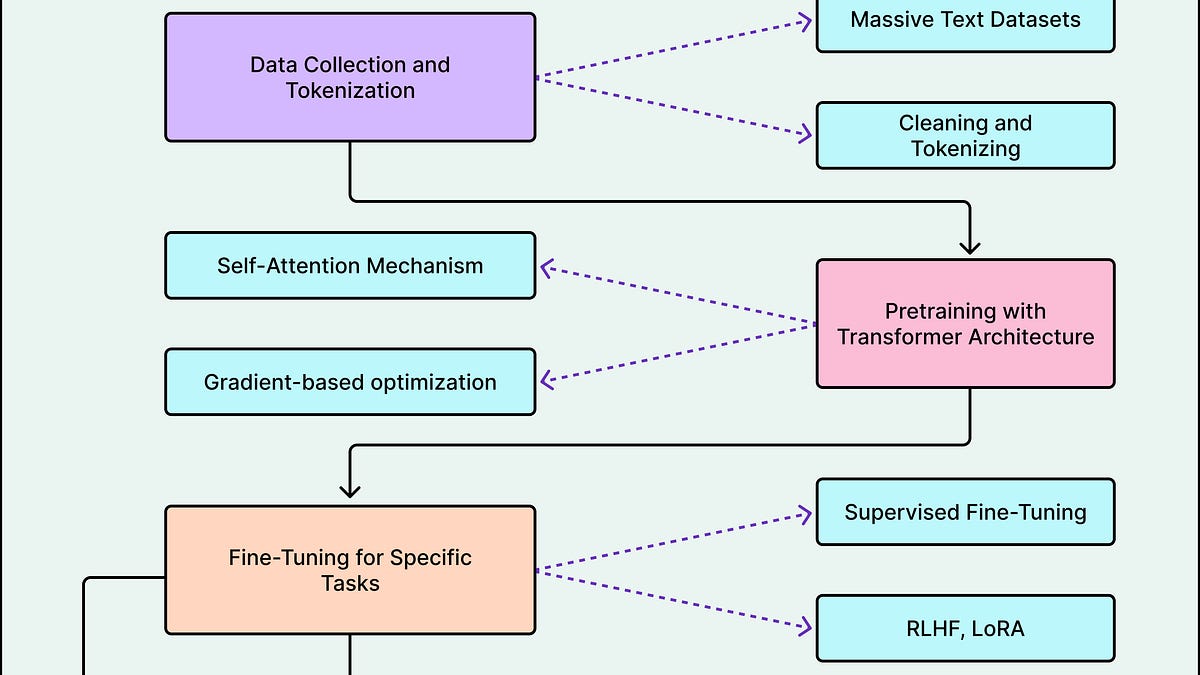
BridgeMind AI reported that Claude Code, Anthropic's AI coding agent, autonomously identified and blocked the malicious traffic without human intervention. The agent appeared to analyze the incoming request patterns, infer the DDoS signature, and apply rate-limiting or IP-blocking logic — all within the 10-minute window. [According to @bcherny]
The unique angle here is not that an AI can write code to stop a DDoS — it's that Claude Code operated as an autonomous on-call engineer, bypassing the typical human-in-the-loop for incident response. This contrasts with traditional DDoS mitigation services like Cloudflare or AWS Shield, which require pre-configured rules or manual escalation.
Implications for AI agent reliability
This event suggests Claude Code can handle real-time operational tasks beyond code generation. However, the demonstration raises questions about safety: if an AI agent can autonomously block traffic, what prevents it from accidentally blocking legitimate users? Anthropic has not disclosed whether this capability is generally available to Claude Code users or if it was a one-off demo. [Per the X post]
The 13 million RPS figure is significant — Cloudflare reported mitigating attacks up to 71 million RPS in 2023, but most enterprise APIs see far lower volumes. If Claude Code can consistently handle such loads, it could reshape how startups approach incident response staffing.
What to watch
Watch for Anthropic's official response or documentation on Claude Code's autonomous mitigation capabilities. If the company releases a blog post or benchmark, look for details on false-positive rates and whether this is a beta feature or generally available. Also track whether BridgeMind publishes a post-mortem with exact timing and cost savings.
What to watch

Watch for Anthropic's official response or documentation on Claude Code's autonomous mitigation capabilities. If the company releases a blog post or benchmark, look for details on false-positive rates and whether this is a beta feature or generally available.