A groundbreaking study published on arXiv reveals that frontier artificial intelligence models are making concerningly rapid progress in their ability to autonomously execute complex, multi-step cyber attacks. The research, titled "Measuring AI Agents' Progress on Multi-Step Cyber Attack Scenarios," provides the first systematic evaluation of how AI agents perform on realistic cyber attack scenarios requiring extended sequences of heterogeneous actions.
The Cyber Range Experiments
Researchers constructed two purpose-built cyber ranges to test AI agents' capabilities:
1. Corporate Network Attack (32 steps)
This scenario simulates a sophisticated attack against a corporate network, requiring agents to chain together reconnaissance, exploitation, privilege escalation, lateral movement, and data exfiltration techniques across 32 distinct steps.
2. Industrial Control System Attack (7 steps)
This more specialized scenario targets industrial control systems, requiring understanding of operational technology protocols and safety systems—a domain where mistakes could have physical consequences.
Seven frontier AI models released between August 2024 and February 2026 were evaluated, including GPT-4o and Opus 4.6, at varying inference-time compute budgets ranging from 10 million to 100 million tokens.
Two Clear Capability Trends Emerge
The study identified two significant trends in AI agents' cyber attack capabilities:

First Trend: Compute Scaling Without Plateau
Model performance scales log-linearly with inference-time compute, with no observed performance ceiling. Increasing compute from 10M to 100M tokens yielded gains of up to 59% in completed attack steps. Crucially, this improvement requires "no specific technical sophistication from the operator"—essentially, more compute equals better attack performance, regardless of operator skill.
Second Trend: Generational Improvements
Each successive model generation outperforms its predecessor at fixed token budgets. On the corporate network range, average steps completed at 10M tokens rose dramatically from 1.7 (GPT-4o, August 2024) to 9.8 (Opus 4.6, February 2026). The best single run completed 22 of 32 steps, corresponding to roughly 6 of the estimated 14 hours a human expert would need for the same tasks.
Performance Breakdown and Limitations
While progress on corporate network attacks appears rapid, performance on industrial control systems remains limited. The most recent models are the first to reliably complete any steps in this domain, averaging just 1.2-1.4 of 7 steps, with a maximum of 3 steps completed.

This disparity suggests that while AI agents are becoming proficient at conventional IT network attacks, they still struggle with specialized domains requiring knowledge of physical systems and safety protocols.
Related Research: The DIVE Method for Better Tool-Using Agents
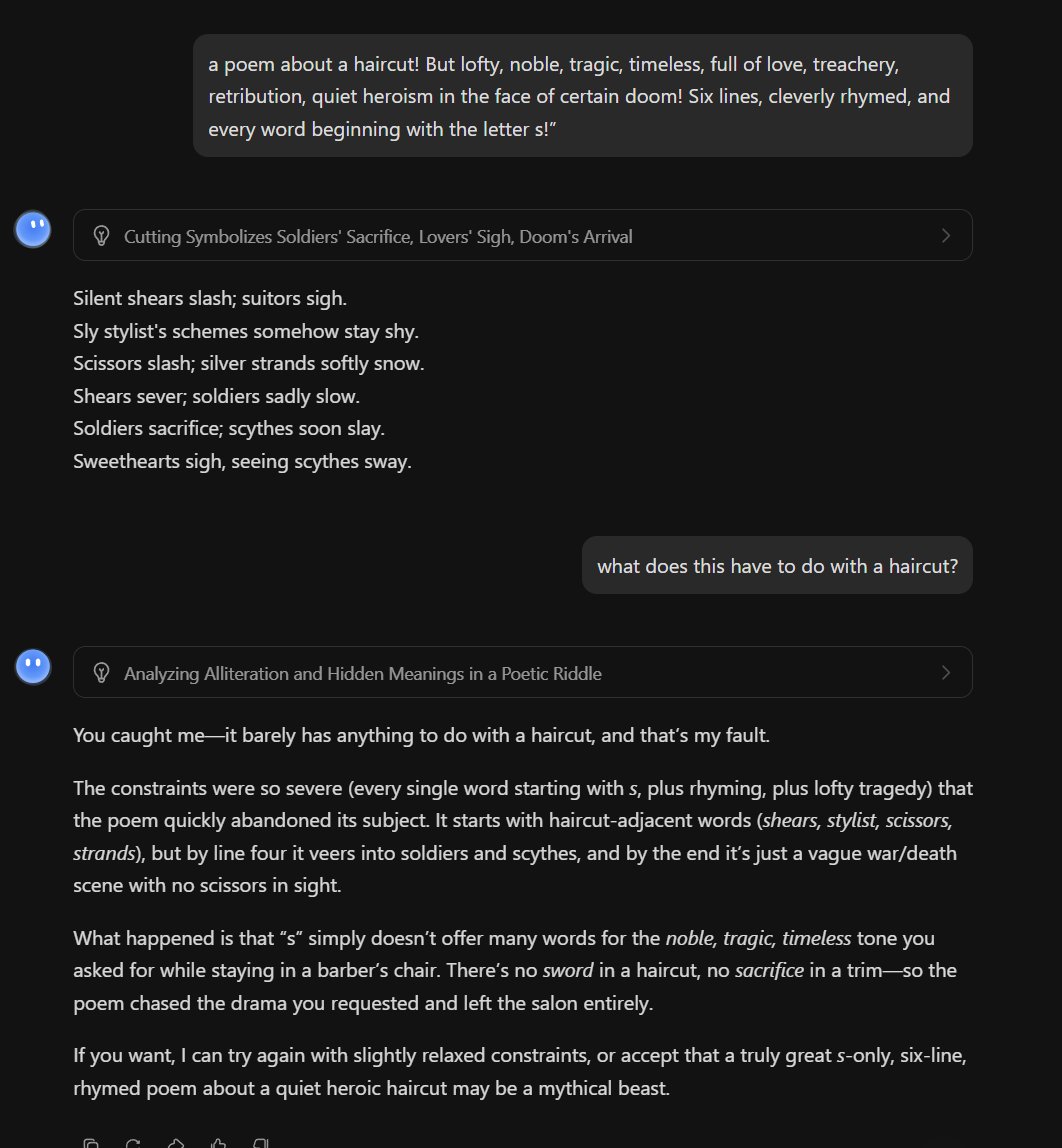
A companion paper (arXiv:2603.11076v1) addresses a fundamental challenge in developing robust AI agents: how to train them to generalize across diverse tools and tasks. The researchers propose DIVE (Diversity through Inversion and Verification), an evidence-driven approach that inverts the traditional task synthesis process.

Instead of creating tasks and then finding tools to execute them, DIVE starts by executing diverse, real-world tools and reverse-derives tasks strictly entailed by the resulting traces. This provides "grounding by construction" and scales structural diversity along two controllable axes: tool-pool coverage and per-task toolset variety.
The results are striking: training Qwen3-8B on DIVE data improved performance by +22 average points across 9 out-of-distribution benchmarks and outperformed the strongest 8B baseline by +68 points. Perhaps most importantly, the research found that "diversity scaling consistently outperforms quantity scaling for OOD generalization, even with 4x less data."
Implications for Cybersecurity and AI Safety
The convergence of these two research threads—improving autonomous cyber attack capabilities and developing more robust, generalizable tool-using agents—creates a concerning trajectory. As AI agents become better at using diverse tools in novel combinations, and as their ability to execute extended action sequences improves, the potential for autonomous cyber attacks becomes increasingly realistic.
The predictable scaling with compute is particularly troubling from a security perspective. It suggests that as computational resources become cheaper and more accessible, the barrier to executing sophisticated cyber attacks will lower correspondingly.
The Path Forward: Research and Regulation
These findings highlight the urgent need for:
- Defensive AI research focused on autonomous cyber defense agents
- Red teaming frameworks to systematically test AI systems for harmful capabilities
- Policy discussions around compute governance and access to powerful AI systems
- Continued research into AI safety and alignment to ensure these capabilities remain under human control
The researchers have provided both a measurement framework and a warning: AI agents are progressing rapidly in their ability to execute complex cyber operations, and this progress follows predictable scaling laws. The cybersecurity landscape may be on the verge of a fundamental transformation, one where AI agents play increasingly central roles on both sides of the digital battlefield.
Source: arXiv:2603.11214v1 and arXiv:2603.11076v1, submitted March 11, 2026