What Changed — The Model Update
Anthropic has unveiled Claude Sonnet 4.6 and, more importantly for developers, Claude Opus 4.6. The Opus 4.6 model represents a significant leap in security analysis capabilities. According to coverage, it has already identified 500+ high-severity open-source vulnerabilities during testing. This isn't just a general intelligence upgrade—it's a specialized enhancement for code security that's now available through Claude Code.
What It Means For Your Daily Workflow
When you run claude code with the Opus 4.6 model, you're no longer just getting a coding assistant. You're getting a security auditor that can:
- Scan dependencies automatically while you work
- Flag vulnerable patterns in real-time as you write code
- Explain security implications of different implementation choices
- Suggest secure alternatives with context about why they're safer
This changes the economics of security review. Instead of scheduling separate security audits or running specialized tools, you get continuous security feedback integrated into your development flow.
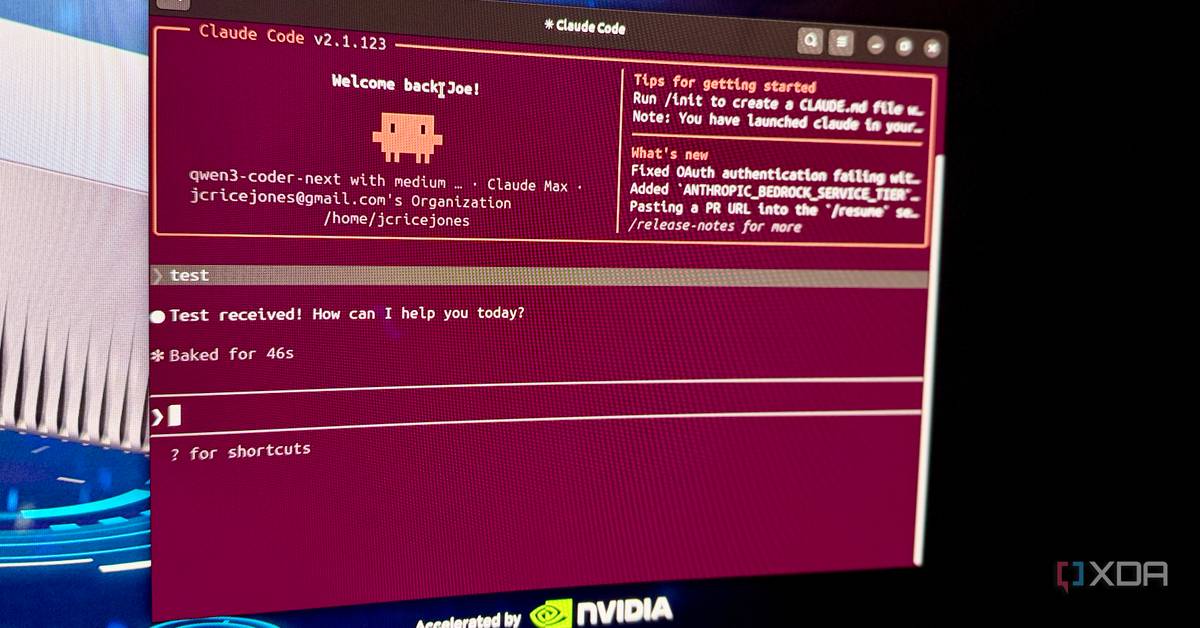
How To Use It Right Now
1. Switch to Opus 4.6
# Set Opus 4.6 as your default model
claude code config set model=claude-3-opus-4.6
# Or use it for specific security-focused sessions
claude code --model claude-3-opus-4.6
2. Add Security Prompts to Your CLAUDE.md
Add these sections to your project's CLAUDE.md file:
## Security Requirements
- Audit all third-party dependencies for known CVEs
- Flag any code patterns that could lead to injection attacks
- Suggest secure alternatives for cryptographic operations
- Review authentication and authorization logic
- Check for data leakage in error messages and logs
## Security Context
Current dependencies: [list your package.json or requirements.txt]
Known security concerns: [mention any previous audits or issues]
Compliance requirements: [SOC2, HIPAA, PCI-DSS if applicable]
3. Run Targeted Security Audits
Instead of just asking Claude Code to "write a login function," prompt it with security in mind:
# Audit a specific file for vulnerabilities
claude code "Review auth.js for security issues. Focus on session management, token handling, and rate limiting."
# Check dependencies
claude code "Analyze package.json for vulnerable dependencies. Suggest updates or alternatives."
# Security-focused refactoring
claude code "Rewrite this SQL query to prevent injection attacks while maintaining performance."
4. Integrate with Your CI/CD
While not directly mentioned in the source, the security capabilities suggest you could:
# Create a security check script
claude code "Write a script that uses the Anthropic API to audit changed files in a PR for security issues."
# Generate security test cases
claude code "Create security-focused unit tests for our user authentication module."
The Bottom Line
Claude Opus 4.6 in Claude Code isn't just another model update. It's turning your development environment into a continuous security audit platform. The 500+ high-severity vulnerabilities found during testing demonstrate this isn't theoretical—it's a proven capability you can leverage today.
Start by switching your model to Opus 4.6 for security-sensitive projects, update your CLAUDE.md with security requirements, and begin prompting with security as a first-class concern. The model's specialized training means you'll get better results than generic "be secure" prompts—it understands specific vulnerability patterns and knows how to fix them.