Key Takeaways
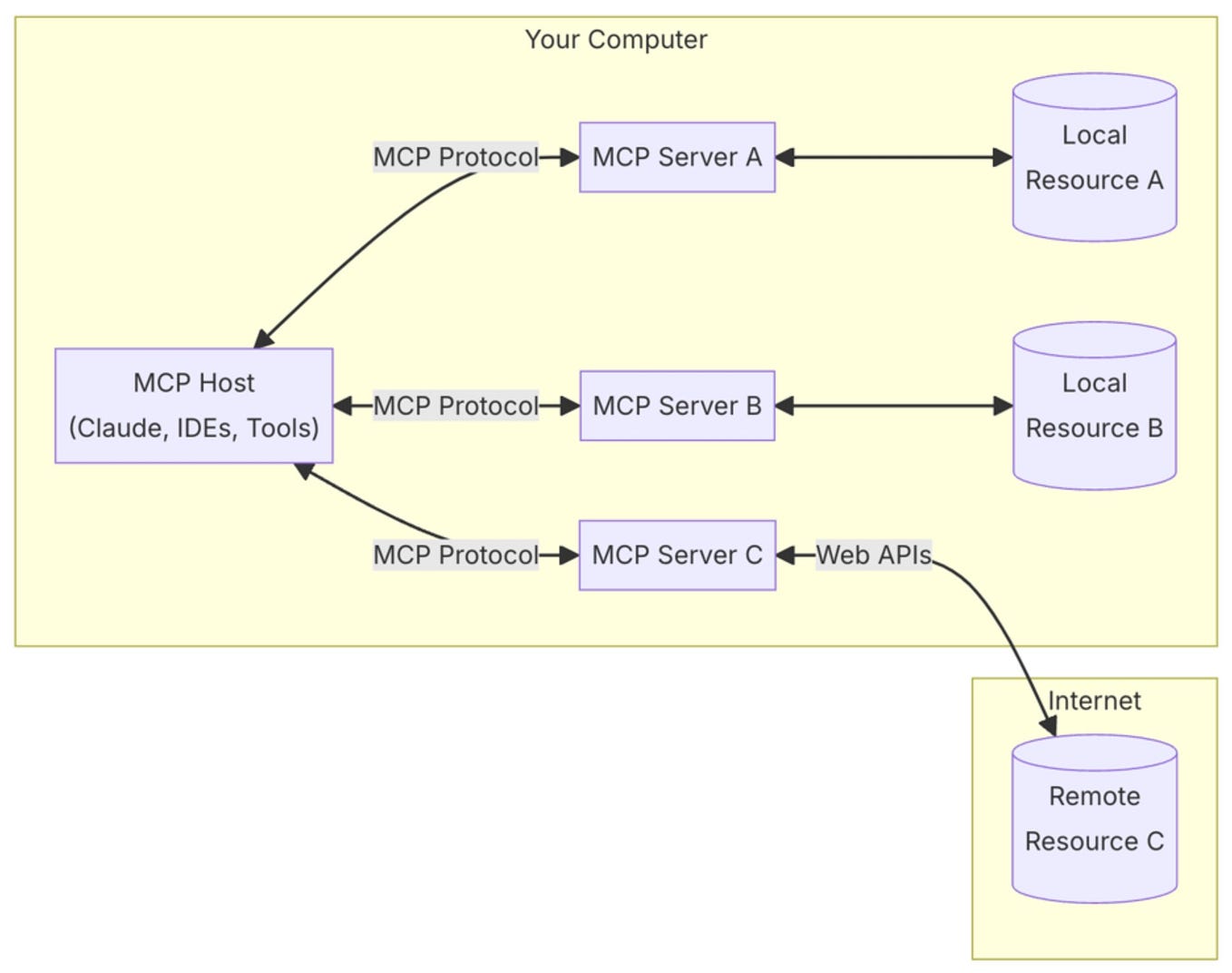
- Cloudflare's MCP portal aggregates servers behind Cloudflare Access auth, while Code Mode collapses APIs into two tools.
- But most SaaS MCP endpoints lack controls — here's how to protect your Claude Code workflows.
What Changed — Cloudflare's MCP Governance Suite

Cloudflare wrapped Agents Week by shipping three things that matter to anyone running Claude Code with MCP:
- MCP Server Portals — Aggregate multiple upstream MCP servers behind Cloudflare Access authentication. One entry point, centralized auth.
- Code Mode — Collapses thousands of API endpoints into two tools:
searchandexecute. Runs in a sandboxed Cloudflare Worker. They claim this drops context costs by 99.9%. - Shadow MCP Detection — New category in Cloudflare Gateway to monitor unauthorized MCP connections.
Also: AI Gateway now sits between MCP clients and model providers for usage tracking.
The Governance Gap — What's Actually Happening
Here's the uncomfortable truth from the Reddit thread: most SaaS vendors whose MCP endpoints people actually connect to are shipping with zero controls. No per-feature toggles. No server allowlists. No audit logs. The admin panel says "enable AI: yes/no" and that's it.
Why? Because adoption isn't being driven by vendors. It's being pulled by users. The classic example:
Marketing wants personalized follow-ups for conference registrants. Someone wires up Claude with MCP connections to the marketing automation tool, the CRM, and the event platform. One prompt: "Pull everyone who registered but didn't show, segment by job title, draft three messages per segment, schedule them in HubSpot." Done in 20 minutes. The ops team would have spent two days.
This is exactly how Claude Code users are operating. And it's exactly why you need governance.
How This Plays Out For Claude Code Users
Two paths emerge:
Path A: Infrastructure-layer governance (Cloudflare's bet). Controls live with network providers. Faster to ship, centralizes visibility, but can't do per-feature granularity.
Path B: App-layer governance. SaaS vendors ship per-feature toggles, MCP allowlists, audit logs. More granular, but slower to materialize.
Neither is obviously right. But here's what you can do today with Claude Code:
1. Audit Your MCP Connections
Run this in your terminal:
# List all configured MCP servers in Claude Code
cat ~/.claude/claude.json | jq '.mcpServers'
Review every endpoint. Ask: Does this SaaS vendor have any MCP controls? If not, you're trusting the all-or-nothing toggle.
2. Add a CLAUDE.md Safety Section
# MCP Governance Rules
- Never execute destructive actions on production MCP endpoints without explicit user confirmation
- Log all MCP tool calls to a local file for audit
- Before connecting a new MCP server, verify it uses authentication (API key, OAuth, or Cloudflare Access)
3. Test Cloudflare's Portal
If you're already on Cloudflare, the portal approach is worth testing. Set up:
- Create a Cloudflare Access application
- Configure it as an MCP server portal
- Point your Claude Code MCP config at the portal instead of individual servers
{
"mcpServers": {
"my-portal": {
"command": "npx",
"args": ["-y", "@cloudflare/mcp-portal-client"],
"env": {
"CLOUDFLARE_ACCESS_CLIENT_ID": "your-id",
"CLOUDFLARE_ACCESS_CLIENT_SECRET": "your-secret"
}
}
}
}
4. Watch for Shadow MCP
If your org uses Cloudflare Gateway, enable the Shadow MCP detection category. It'll flag unauthorized MCP connections — critical if someone wires up a personal Claude Code session to a production API without telling anyone.
What This Means For Your Workflow
MCP is powerful. Claude Code with MCP connections to your CRM, marketing tools, and databases can do in minutes what took days. But the Reddit thread captures the tension perfectly: "is anyone testing the Cloudflare portal stuff? building your own gateway? or just running unmanaged and assuming this all sorts itself out?"
Don't assume it sorts itself out. Start with an audit. Add a CLAUDE.md governance section. Test the Cloudflare portal if you're on their stack. And push your SaaS vendors for per-feature MCP controls.
The infrastructure-layer and app-layer approaches will converge eventually. But right now, the gap is real — and it's your data on the line.
gentic.news Analysis
This story sits at the intersection of two trends we've been tracking: the explosion of MCP adoption (164 million monthly PyPI downloads as of last month, per our coverage) and the enterprise governance scramble that inevitably follows.
Cloudflare's move is strategic. They're positioning as the infrastructure layer for AI agent connectivity — a role that aligns with their existing Zero Trust and Gateway products. But as the Reddit thread notes, this only works if you're already in the Cloudflare ecosystem.
For the broader Claude Code ecosystem, the real story is the governance vacuum. Anthropic developed MCP as an open standard (we covered the November 2024 launch), but they left the control plane to the ecosystem. That's by design — but it means Claude Code users need to build their own governance until SaaS vendors catch up.
The 99.9% context cost reduction claim from Cloudflare's Code Mode is worth watching. If it holds, it could change how Claude Code users architect MCP connections — fewer, more powerful tools instead of hundreds of granular endpoints. That's a pattern we expect to see more of as MCP matures.