What Claude Code's Telemetry Actually Shows
Claude Code ships with built-in OpenTelemetry (OTel) instrumentation. This isn't just basic metrics—it's structured, application-level telemetry that captures every significant action: tool calls, prompts, permission decisions, and API requests. This creates a complete audit trail that traditional endpoint detection and response (EDR) tools miss.
Your EDR shows process trees and commands, but fragments the session. You see git clone, npm install, and keychain access as isolated events. Claude Code's OTel events connect them: they show the original prompt that triggered the sequence, what the model was attempting, and how each action fits into the broader task. This context is critical for distinguishing legitimate development work from suspicious activity.
Two Data Streams: Metrics vs. Events
Claude Code exports two separate OTel streams, and you need to understand the difference:
Metrics (OTEL_METRICS_EXPORTER): Time-series counters aggregated over 60-second intervals. These track session counts, token usage, costs, and lines of code modified. Useful for dashboards and cost tracking, but too aggregated for security detection.
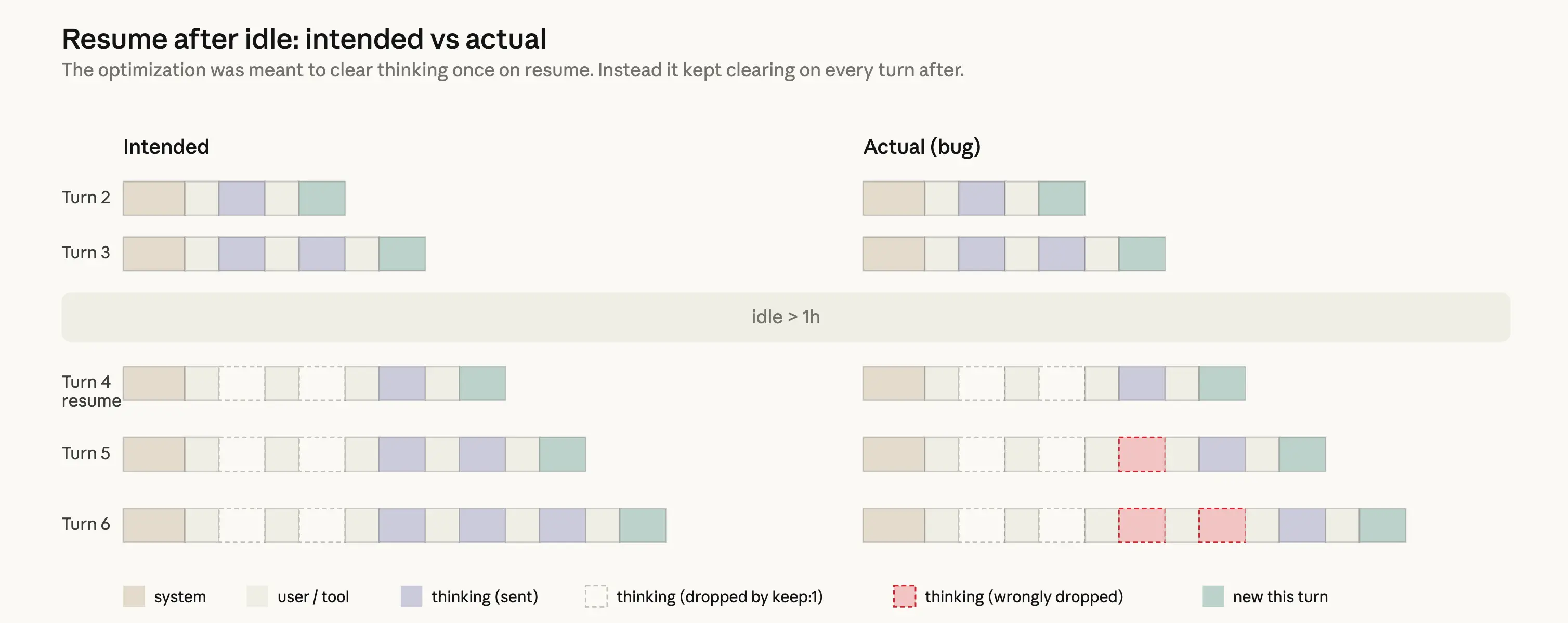
Events (OTEL_LOGS_EXPORTER): Structured log records emitted every 5 seconds by default. Each event corresponds to a specific action: every bash command, tool decision, API call, and error. This is what you need for detection engineering and audit trails.
Configuring only metrics leaves you blind to command-level activity. For security monitoring, you need both streams enabled.
How to Enable It Right Now
Add these environment variables to your shell configuration (.bashrc, .zshrc, etc.):
export CLAUDE_CODE_ENABLE_TELEMETRY=1
export OTEL_METRICS_EXPORTER=otlp # For dashboards and cost tracking
export OTEL_LOGS_EXPORTER=otlp # For security detection and audit trails
export OTEL_EXPORTER_OTLP_PROTOCOL=grpc
export OTEL_EXPORTER_OTLP_ENDPOINT=http://your-collector:4317
For team-wide enforcement, configure these via the managed settings file at /Library/Application Support/Claude Code/ (macOS) or equivalent location for your OS.
What This Means for Your Workflow
Once enabled, you'll get structured JSON logs for every Claude Code session. Each event includes:
- The original user prompt
- Tool calls and their parameters
- Permission decisions (why Claude decided to run a command)
- Command execution results
- Error messages and stack traces
This transforms debugging from guesswork to precise investigation. When a Claude Code session produces unexpected results, you can trace exactly which prompt led to which command, and why permissions were granted or denied.
Security Implications for Development Teams
For detection engineers, this telemetry fills the gap between endpoint telemetry and LLM activity. Traditional security tools see Claude Code as a black box executing commands. With OTel events, you can:
- Detect prompt injection attempts: See when user input deviates from normal patterns
- Audit permission decisions: Understand why Claude chose to execute sensitive commands
- Reconstruct attack chains: Connect seemingly unrelated commands back to a single malicious prompt
- Establish baselines: Define normal usage patterns for different developers and roles
Without this context, legitimate development activity (like setting up a new GitLab environment) can trigger false positives because EDR sees keychain access and bash history searches without understanding they're part of a sanctioned workflow.
Limitations to Know
The source notes this is application-level telemetry, not system-level. It won't capture everything happening on the machine, only what flows through Claude Code. Also, the 5-second export interval means near-real-time monitoring, but not instantaneous.
For comprehensive coverage, you still need traditional EDR alongside Claude Code's OTel events. The combination gives you both the "what" (commands executed) and the "why" (prompt context and permission chain).