A senior security researcher at Anthropic has publicly stated that the company's Claude AI model is a more effective security researcher than he is, citing concrete financial results from vulnerability discovery.
What Happened
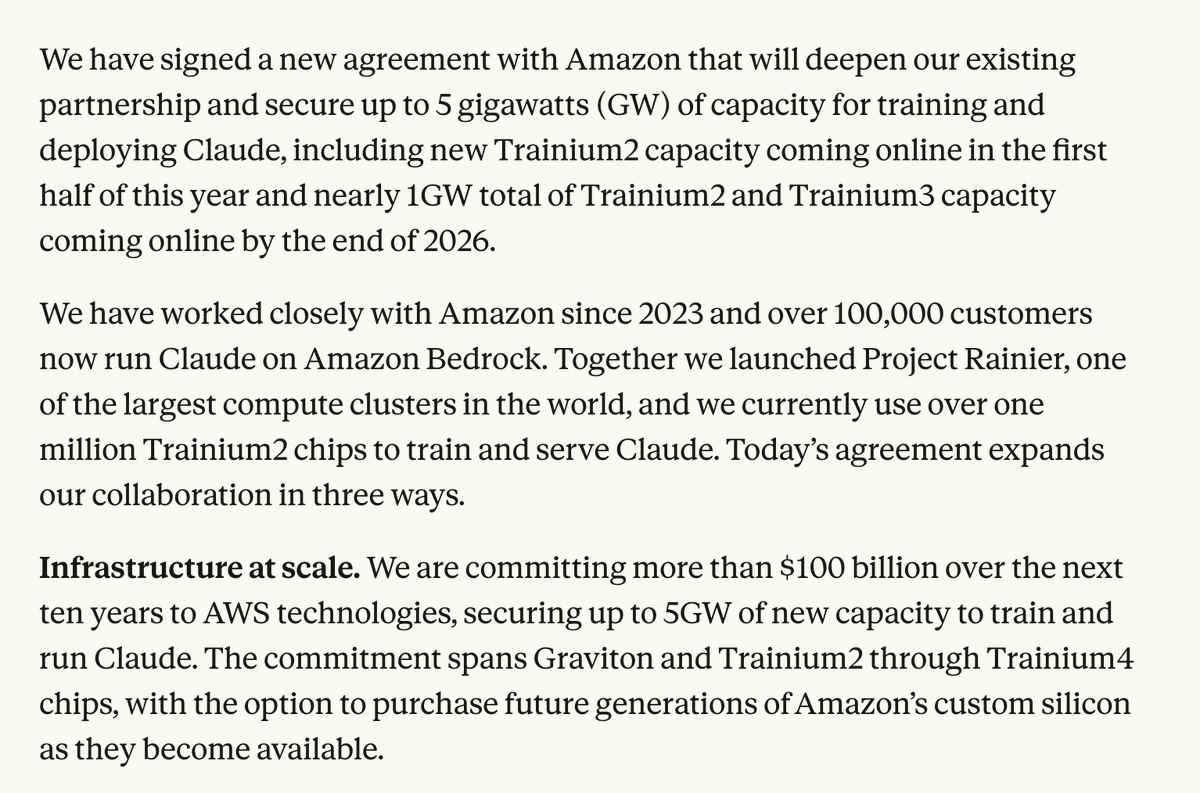
Nicolas Carlini, a prominent AI security researcher at Anthropic with over 67,000 academic citations, made the claim in a public discussion. He stated that Claude has demonstrated superior capability in finding security vulnerabilities compared to his own expertise. The AI has reportedly generated $3.7 million in earnings from discovering and exploiting vulnerabilities in smart contracts—self-executing contracts on blockchain platforms.
Additionally, Carlini noted that Claude successfully identified security flaws in Ghost, an open-source publishing platform with over 52,000 stars on GitHub. This suggests the AI's vulnerability discovery capabilities extend beyond blockchain to traditional software systems.
Context: AI in Security Research
The use of AI for security auditing represents a natural evolution in both fields. Large language models trained on vast codebases can potentially identify patterns, logic flaws, and common vulnerability patterns that might escape human reviewers. Several companies, including Google (with its Project Zero) and startups like ShiftLeft, have been exploring AI-assisted code review and vulnerability detection.
Anthropic's Claude, known for its strong performance on coding benchmarks, appears to have been applied systematically to security research with measurable financial outcomes. The $3.7 million figure likely comes from bug bounty programs or ethical exploitation of vulnerabilities in decentralized finance (DeFi) protocols, where rewards for critical flaws can reach seven figures.
Technical Implications
While specific technical details of how Claude was prompted or fine-tuned for security work weren't provided in the source, the results suggest several possibilities:
Code Understanding at Scale: Claude's ability to parse complex smart contract code (often written in Solidity or Rust) and identify exploitable conditions indicates deep semantic understanding of programming logic and blockchain-specific patterns.
Adversarial Testing Capability: The mention of "exploiting" smart contracts suggests Claude isn't just identifying potential vulnerabilities but generating working proof-of-concept exploits—a more advanced capability requiring understanding of system states and transaction sequences.
Cross-Domain Application: Finding vulnerabilities in Ghost (a JavaScript/Node.js application) demonstrates the model's versatility across different programming languages and software architectures.
What This Means in Practice
For security teams and developers, this development signals that AI-assisted code review is moving from theoretical promise to practical utility with direct financial impact. The $3.7 million earnings represent one of the first publicly disclosed cases of an AI system generating substantial revenue through security research.
gentic.news Analysis
This disclosure from a respected researcher like Carlini carries significant weight in the AI security community. Carlini, known for his work on adversarial examples and model extraction attacks, represents the intersection of AI safety and traditional cybersecurity. His endorsement of Claude's capabilities suggests Anthropic may be developing specialized security-focused versions of their models, potentially as a product offering or internal tool.
The timing is notable. This follows increased industry focus on AI-assisted development tools, with GitHub Copilot, Amazon CodeWhisperer, and Google's Gemini Code Assist all competing in the AI coding assistant space. However, most public demos focus on code generation rather than security auditing. Anthropic appears to be differentiating by emphasizing Claude's analytical and adversarial capabilities rather than just its generative ones.
This also aligns with broader trends in AI alignment research. As models become more capable, ensuring they can identify and help fix security vulnerabilities—rather than exploit them maliciously—becomes crucial for responsible deployment. Anthropic's constitutional AI approach, which emphasizes harmlessness and helpfulness, may be particularly well-suited to security applications where the model must operate within ethical boundaries while probing system weaknesses.
The financial aspect is particularly revealing. Earning $3.7 million from bug bounties provides concrete validation of capability beyond benchmark scores. It demonstrates that Claude can identify vulnerabilities that actual blockchain systems are willing to pay significant sums to fix—a real-world stress test of practical utility.
Frequently Asked Questions
How did Claude AI earn $3.7 million from smart contracts?
Claude likely participated in bug bounty programs for blockchain protocols and decentralized applications. These programs reward security researchers for responsibly disclosing critical vulnerabilities. The substantial earnings suggest Claude found multiple high-severity flaws in valuable DeFi systems, with individual bounties potentially ranging from tens of thousands to over a million dollars for the most critical issues.
What makes Claude particularly good at security research compared to other AI models?
While specific architectural details haven't been disclosed, Claude's strengths likely stem from Anthropic's focus on reasoning capabilities, constitutional AI training that emphasizes helpfulness and harmlessness, and potentially specialized fine-tuning on security-relevant datasets. The model's strong performance on coding benchmarks suggests robust code understanding, which is foundational for vulnerability discovery.
Is Claude finding vulnerabilities in production systems ethical?
Yes, when conducted through proper channels. Responsible vulnerability disclosure involves finding flaws, reporting them to the affected organization (often through bug bounty platforms), and allowing time for fixes before any public disclosure. The $3.7 million earnings indicate organizations willingly paid for these discoveries through established bounty programs, following ethical security research practices.
Could this technology be used maliciously to find and exploit vulnerabilities?
Like any security tool, AI-powered vulnerability discovery has dual-use potential. However, Anthropic's constitutional AI approach and safety-focused training likely include safeguards against malicious use. The fact that Claude is earning bug bounties—rather than exploiting vulnerabilities for profit—suggests it's being deployed ethically within established security research frameworks.