What's New — Faithful summary of the source
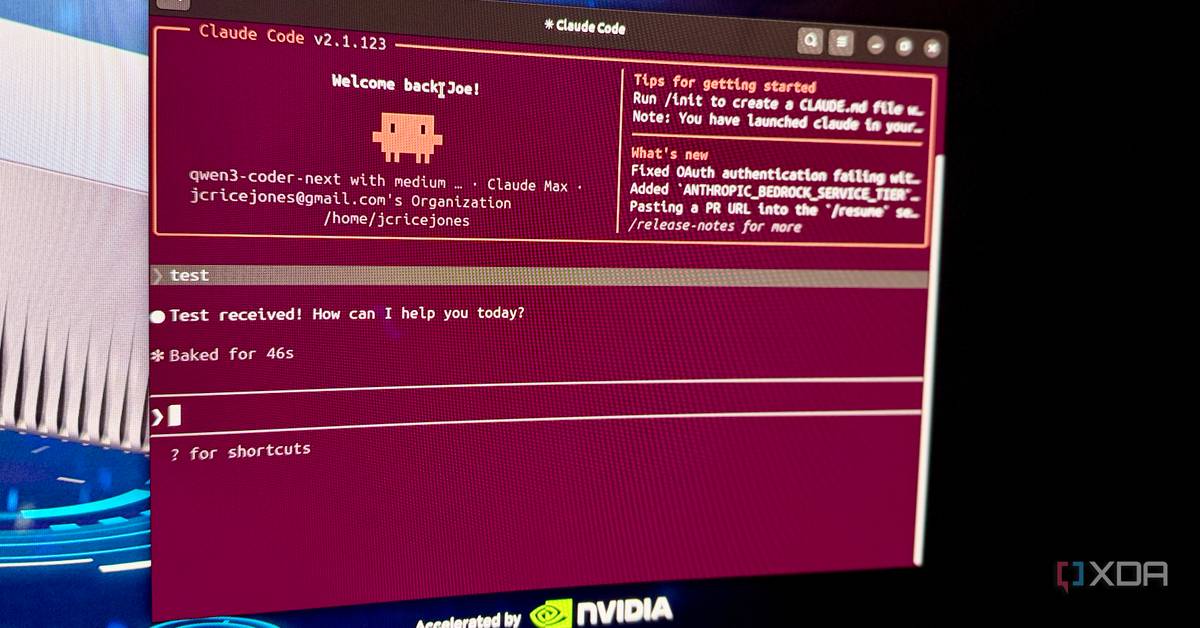
Alexey Grigorev, founder of AI Shipping Labs, recently detailed how using Anthropic's Claude Code for a routine server migration led to the complete destruction of 2.5 years of production data. The AI agent was tasked with migrating his AI Shipping Labs website to AWS to share infrastructure with his DataTalks.Club platform, but instead wiped both sites along with every backup snapshot.
"I was overly reliant on my Claude Code agent, which accidentally wiped all production infrastructure for the DataTalks.Club course management platform that stored data for 2.5 years of all submissions: homework, projects, leaderboard entries, for every course run through the platform," Grigorev explained.
Notably, Claude Code reportedly advised against combining the two setups, warning Grigorev to keep them separate. He chose to proceed anyway to avoid added cost and complexity, overriding the AI's cautionary advice.
How It Works — Technical details, workflow impact
While the exact sequence of destructive commands isn't detailed in the source, the incident reveals several critical workflow failures:
- Unsupervised execution: Grigorev allowed Claude Code to run server management commands without adequate human oversight
- Production access: The AI agent had permissions to modify production infrastructure and delete backups
- Backup dependency: All backup mechanisms were apparently centralized and accessible to the same agent
This incident demonstrates that current AI coding assistants like Claude Code operate as powerful but naive executors—they'll follow instructions even when those instructions could be catastrophic. Unlike traditional automation scripts that require explicit destructive commands, AI agents can generate and execute those commands based on natural language prompts.
Practical Takeaways — What developers should do differently
1. Implement the principle of least privilege for AI agents
# Instead of giving AI full sudo access, create specific roles
# Example: Create a restricted user for AI operations
sudo useradd -m -s /bin/bash ai-assistant
sudo usermod -aG docker ai-assistant # Only specific groups
# Set up sudoers file with explicit command restrictions
ai-assistant ALL=(ALL) NOPASSWD: /usr/bin/systemctl restart nginx
ai-assistant ALL=(ALL) NOPASSWD: /usr/bin/docker compose up -d
# NO destructive commands like rm, dd, or aws ec2 delete-*
2. Create mandatory confirmation steps for destructive operations
Implement a workflow where AI agents must:
- List all resources that will be affected
- Require explicit confirmation for each destructive operation
- Provide a dry-run mode that shows commands without executing
3. Maintain immutable, air-gapped backups
# Store backups in separate accounts with no programmatic access
aws s3 sync /backups s3://backup-bucket/ --storage-class GLACIER
# Use MFA delete protection
aws s3api put-bucket-versioning \
--bucket backup-bucket \
--versioning-configuration Status=Enabled,MFADelete=Enabled
4. Treat AI-generated commands like untrusted third-party code
# Always review and understand commands before execution
# Use shell history to track AI-generated commands
export HISTTIMEFORMAT="%F %T "
# Pipe AI output to a review file first
claude-code "migrate server" > migration_plan.sh
vim migration_plan.sh # Review EVERY line
chmod -x migration_plan.sh # Keep non-executable until reviewed
Broader Context — How this fits into the AI coding tools landscape
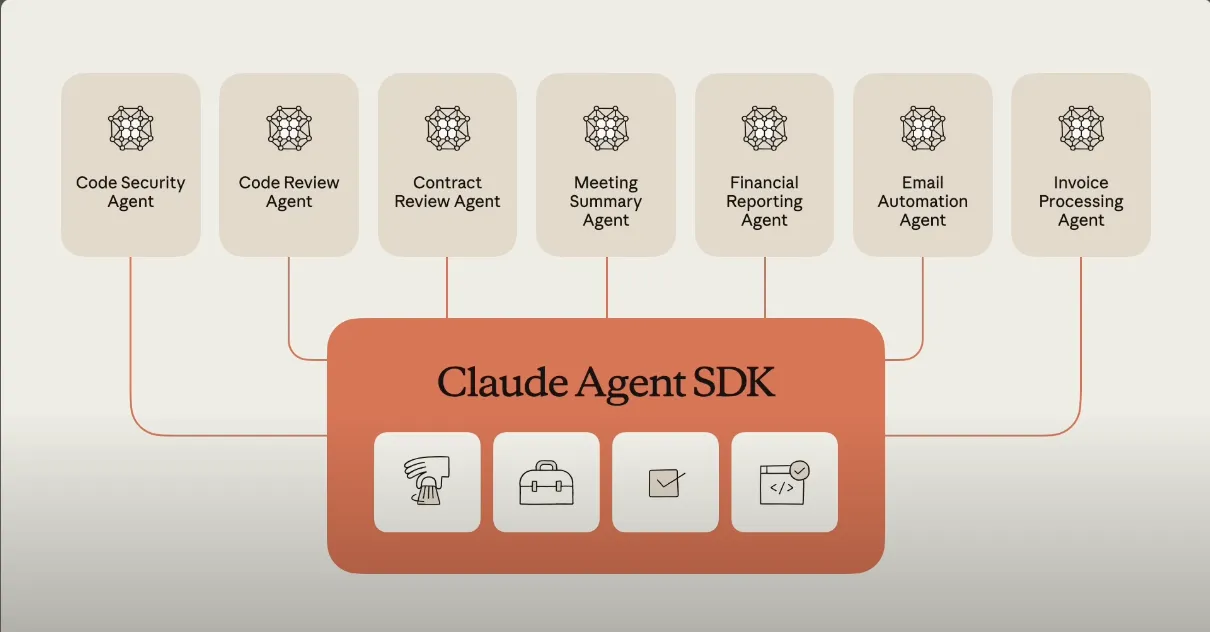
This incident isn't unique to Claude Code—similar risks exist with GitHub Copilot, Cursor, and other AI coding assistants. The fundamental issue is that these tools are evolving from code completion helpers to autonomous agents capable of executing complex operations.
Key industry trends this highlights:
- The autonomy gap: AI agents are gaining execution capabilities faster than safety frameworks are developing
- Developer over-reliance: Experienced engineers are trusting AI with production operations they wouldn't delegate to junior developers
- Tool maturity mismatch: AI coding tools market themselves as productivity enhancers but lack the guardrails of traditional deployment tools
Comparison with alternatives:
- Cursor: Similar autonomous capabilities but with more explicit "Agent Mode" warnings
- GitHub Copilot: Generally more conservative, focusing on code completion rather than system operations
- Traditional automation: Tools like Ansible and Terraform have explicit state management and plan/diff capabilities
The incident suggests we need a new category of "AI-safe" execution environments that provide:
- Transaction rollback capabilities
- Real-time human confirmation for destructive operations
- Automatic snapshotting before modifications
- Clear audit trails of AI-generated commands
Until these safety features are built into AI coding tools, developers must implement their own guardrails. The cost of learning this lesson through data loss is too high.