The False Choice: Security or Productivity
Claude Code's --dangerously-skip-permissions flag is a productivity powerhouse. It lets the agent run autonomously as your user, with full access to SSH keys, cloud credentials, and your entire filesystem. No approval prompts. No interruptions.
Most developers never turn it on. Instead, they sit in manual approval mode, clicking through endless approve this file write? dialogs. This is a human CAPTCHA that provides fake security. As the source article points out, any prompt injection or malicious config file can bypass these approvals. The code runs before you see the prompt. You're trading real productivity for an illusion of safety.
Recent CVEs like CVE-2025-59536 and CVE-2026-21852 confirm the threat: simply cd-ing into a malicious repo can execute arbitrary shell commands or exfiltrate your API key. The agent itself has even been documented finding path traversal exploits to escape its own sandbox. The built-in sandbox (based on sandbox-exec or bubblewrap) forces this binary choice: restricted but safe, or powerful but dangerous.
The Real Solution: OS-Level Containment
The solution isn't more prompts; it's better isolation. The goal is to create an environment where the agent has full autonomy but cannot reach anything dangerous. If it can't touch your ~/.ssh/ directory, your AWS config, or your npm credentials, then the --dangerously-skip-permissions flag is no longer dangerous.
This is an OS-level problem. Seatbelt profiles and simple deny lists aren't sufficient because they operate on the same principle as the manual prompts: trying to block bad actions. A robust solution creates a contained filesystem and network namespace where only approved resources are available.
Implementing Safe Autonomy Today
You don't need to build a tool from scratch to apply this principle. You can create a secure, disposable workspace for Claude Code using existing containerization.

Using Docker for a Disposable Workspace:
Create a Dockerfile that sets up a minimal development environment with only the tools and project code you need.
FROM ubuntu:22.04
RUN apt-get update && apt-get install -y git curl nodejs npm python3 python3-pip
WORKDIR /workspace
# Copy ONLY the project code, not your home directory
COPY ./my-project /workspace
# Run as a non-root user
RUN useradd -m -u 1000 developer
USER developer
Build and run the container, mounting only the project directory:
docker build -t claude-safe .
docker run -it --rm -v $(pwd)/my-project:/workspace claude-safe /bin/bash
Inside this container, you can install and run Claude Code. The agent has full root-like access within the container, but it cannot reach your host machine's SSH keys, npm cache, or any credentials not explicitly copied into the image.
Using a Dedicated User Account:
On your local machine, create a new, limited user account specifically for Claude Code.
# Create the user
sudo useradd -m -s /bin/bash claude-agent
# Set a password
sudo passwd claude-agent
# Switch to the user and set up a minimal environment
sudo su - claude-agent
Configure this user's home directory to contain only the project files and necessary tools. Use filesystem permissions (chmod, chown) to ensure this user cannot read from your primary user's home directory. Then, run Claude Code as this user. This provides a strong isolation layer at the OS level.
Your New Workflow
- Context is Key: Before starting a session, explicitly define the project's scope and the resources it's allowed to use in a
CLAUDE.mdfile. For example: "You are working within the/workspacedirectory. Do not attempt to access files outside this path. The required dependencies are listed inpackage.json." - Launch in the Container: Start your Docker container or switch to the dedicated user.
- Run with Full Power: Use
claude code --dangerously-skip-permissionswithout fear. The agent can runnpm install, edit files, and execute git commands autonomously, dramatically speeding up your workflow. - Review, Then Integrate: Once the agent completes its task, review the changes from the safety of your host machine before committing them to your main repository.

This approach flips the script. Instead of trying to block every possible bad action, you start from a position of zero trust and explicitly grant access only to what's necessary. It turns the dangerous flag into a pure productivity tool.
gentic.news Analysis
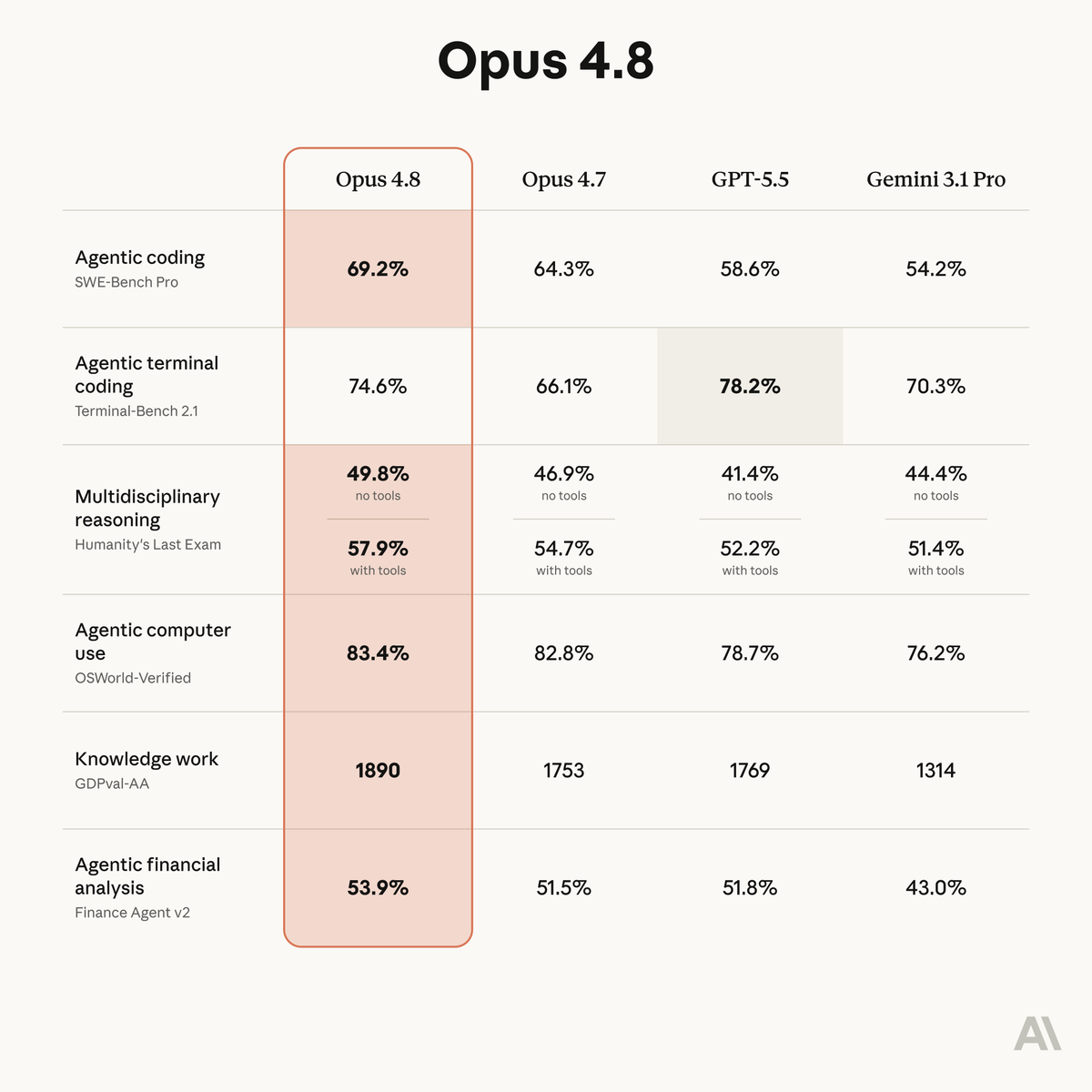
This development highlights a critical, evolving tension in agentic coding tools. As Claude Code's usage surges—it's appeared in 70 articles this week alone—the community is moving beyond basic features to solve foundational problems of security and trust. The recent Claude Code OAuth bug and telemetry cache penalty issue show that stability and user control are top of mind.

The source article's focus on CVEs and sandbox escapes aligns with a broader trend of increased scrutiny on AI agent security. This isn't a Claude-specific issue; competitors like Cursor face the same exposures but with less public visibility due to Anthropic's transparent advisory process. The push for safe autonomy directly supports the productivity gains promised by recent features like the onboarding workflow that reduces codebase understanding time to 4 hours.
Solving the security-productivity paradox is the next frontier. As developers seek to integrate tools like the new Gemini Flash MCP server or build content pipeline CLIs, they need a foundation that doesn't force them to choose between safety and speed. The OS-level containment model provides that foundation, enabling the full potential of autonomous agents.