The Vulnerability — First-Token-Only Evaluation
A critical flaw in Claude Code's permission system allows dangerous commands to bypass deny lists when chained with other operations. The deny rule evaluator only checks the first token of a Bash command. If you've added git clean to your deny list, it will block git clean -fd but allow git fetch && git pull && git clean -fd.
This isn't theoretical. Two independent reports (GitHub issues #36637 and #31523) document the same root cause. The problem affects both deny lists and allow lists — the parser evaluates only the initial command token, then permits or blocks the entire compound expression based on that single check.
Why This Matters for Your Daily Workflow
Claude naturally chains commands because it's efficient and follows standard shell practices. When you ask Claude to "update dependencies and clean up," it might generate:
git fetch && npm install && git clean -fd
If git clean is in your deny list, you'd expect protection. But the evaluator sees git fetch first, finds no match, and allows the entire chain. Your working tree disappears.
This isn't about adversarial prompts. Claude isn't trying to bypass your rules — it's following its natural command-chaining behavior while the permission system fails to parse compound expressions correctly.
The Working Fix — PR #36645
A community-submitted fix (PR #36645) adds proper compound command parsing to Claude Code's PreToolUse hooks. The 573-line implementation:
- Splits commands on
&&,||,;, and| - Checks each segment independently against deny/allow rules
- Blocks the entire expression if any segment violates rules
- Includes 34 passing tests
You can review the implementation at github.com/anthropics/claude-code/pull/36645.
Immediate Protection — Bash Guard Script
While waiting for the official fix, you can implement a local guard. Create ~/.claude/bash-guard.sh:
#!/bin/bash
# Compound command guard for Claude Code
check_command() {
local cmd="$1"
# Split on common shell operators
IFS='&&||;|' read -ra parts <<< "$cmd"
for part in "${parts[@]}"; do
part=$(echo "$part" | xargs) # Trim whitespace
first_token=$(echo "$part" | awk '{print $1}')
# Check against your deny list
if [[ " $DENY_LIST " == *" $first_token "* ]]; then
echo "Blocked: '$first_token' in compound command"
return 1
fi
done
return 0
}
# Define your deny tokens
DENY_LIST="git-clean rm dd shred"
# Use in your CLAUDE.md or as a pre-hook
Add this to your CLAUDE.md:
## Security Rules
- Never run `git clean`, `rm -rf`, `dd`, or `shred`
- Use the bash-guard script before executing any shell command
- Test compound commands manually before trusting automated execution
Anthropic's Response — And Why It's Problematic
Anthropic's security team responded that "Claude Code's deny rules are not designed as a security barrier against adversarial command construction. They are a convenience mechanism to constrain well-intentioned agent actions."
This creates two problems:
- It misaligns with user expectations — Developers add
git cleanto deny lists specifically to prevent data loss - It ignores the actual failure mode — This isn't about adversarial construction; it's about Claude's normal command-chaining behavior bypassing incomplete parsing
What You Should Do Today
- Audit your deny lists — Identify commands that could be chained
- Add explicit warnings to your
CLAUDE.mdabout command chaining - Consider OS-level protections — Use Docker containers or restricted user accounts for high-risk operations
- Monitor the PR — The community fix provides a complete solution; pressure for its adoption
- Test compound commands — Before running Claude-generated chains, manually verify each segment
Remember: Claude Code is an agentic tool with real filesystem access. Treat its permissions with the same seriousness you'd apply to any automation running on your production machine.
gentic.news Analysis
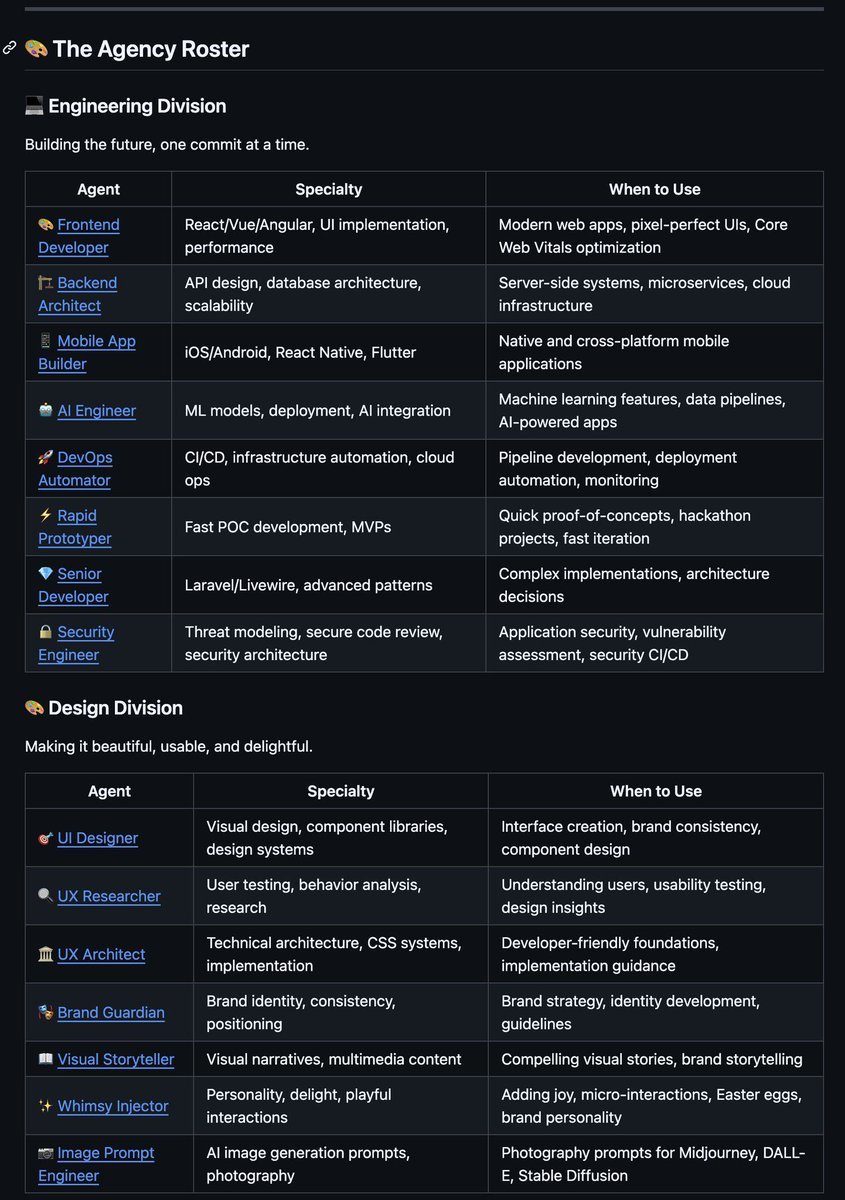
This security flaw emerges as Claude Code adoption accelerates — the tool appeared in 144 articles this week alone, reflecting its rapid integration into developer workflows. The vulnerability highlights a growing pain for Anthropic's agentic coding ecosystem, which has expanded significantly since the March 2026 releases of Auto Mode, the official Git MCP server, and voice capabilities.
The community's rapid response with a tested fix (PR #36645) demonstrates the strength of Claude Code's open development model, similar to how GitHub repositories have previously improved Claude's output. However, Anthropic's dismissal of the report as "informational" contrasts with the tool's positioning as a production-ready coding assistant — especially concerning given Claude Code's integration with Claude Agent frameworks where multiple agents collaborate on complex tasks.
This follows a pattern we've seen before: as AI coding tools gain more autonomy (benchmarks show Claude Code agents average 25 navigation actions per edit), permission systems must evolve beyond simple token matching. The fix aligns with broader industry trends toward more sophisticated agent safeguards, similar to the explicit tool call patterns we recommended in "Fix Your Silent Slash Command Failures."
Looking forward, expect more granular permission systems as Claude Code moves beyond "convenience mechanisms" toward true security boundaries — especially as Anthropic competes with OpenAI and Google for enterprise adoption where such safeguards are non-negotiable.