What It Does — A Governance Layer for MCP
SurePath AI has launched MCP Policy Controls, a security and governance platform designed specifically for the Model Context Protocol (MCP). This isn't a new MCP server; it's a control plane. Its core function is to provide real-time controls over what MCP servers and tools are allowed to be used by AI applications like Claude Code. As Randy Birdsall of SurePath AI states, "MCP is a direct line from generative AI clients to the systems that enable a business to operate." These tools, which can run locally on a developer's machine, are often launched silently by AI desktop apps. This new capability aims to close the visibility gap, giving security teams the ability to adopt MCP safely with oversight from day one, rather than blocking it entirely.
Why Claude Code Users Should Care
If you use Claude Code with MCP servers (like for databases, git, or your internal systems), you're part of the rapid adoption wave. The protocol connects Claude directly to your tools and data, which is powerful but introduces a new attack surface. Traditional firewalls or identity management (IAM) policies aren't built to understand MCP's unique, tool-level interactions. Without specific controls, organizations might be exposing sensitive operations without realizing it. SurePath's argument is that security shouldn't mean shutting down innovation—it should mean managing it intelligently. For developers, this translates to potential corporate policies that will govern which MCP servers you can connect to Claude Code, ensuring safe access to approved tools.
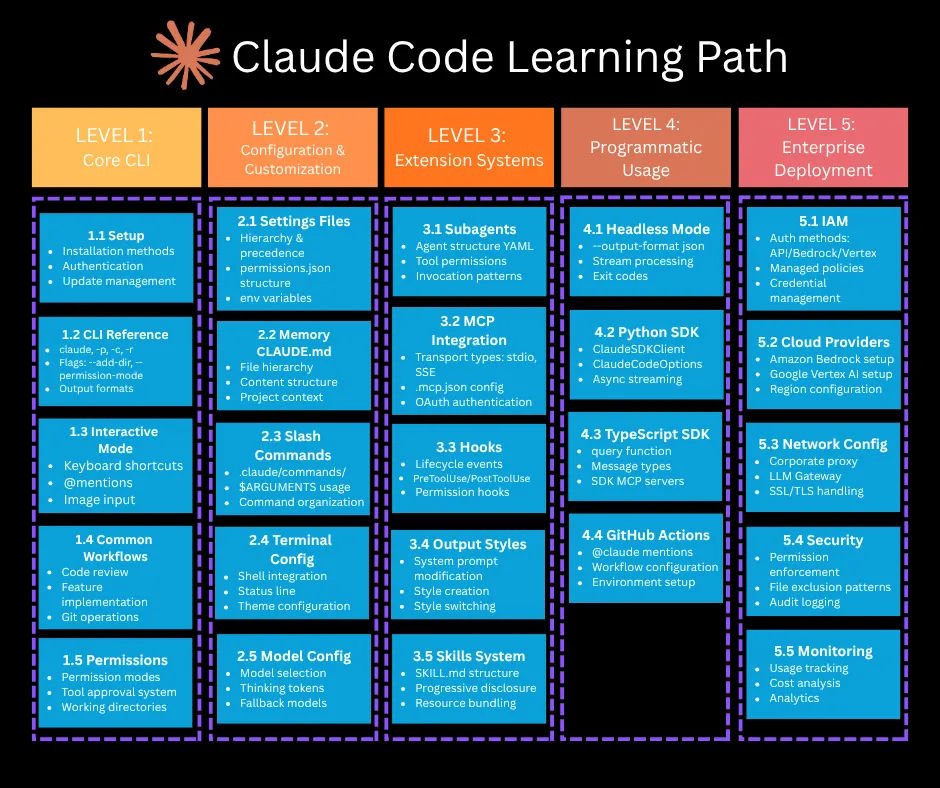
What This Means for Your Workflow
While this is an enterprise platform, its emergence signals a maturation of the MCP ecosystem that affects all users. For individual developers, it underscores the importance of being mindful about the MCP servers you install and run. For teams and companies, it provides a path to standardize and secure Claude Code's extended capabilities.
Adopting a similar mindset can improve your local security:
- Audit Your MCP Servers: Regularly review the MCP servers configured in your
claude_desktop_config.json. Remove any you no longer use. - Understand Server Permissions: Before installing a new MCP server from the community, check what system resources or APIs it requires access to.
- Advocate for Internal Standards: If you're pushing for Claude Code and MCP adoption at your company, you can now point to solutions like SurePath's Policy Controls as a way to address security concerns proactively, rather than facing a blanket ban.
The goal is to keep using powerful tools like the MCP Toolbox for Databases or custom internal servers, but with the appropriate guardrails in place. As MCP becomes the backbone of AI-powered development, managing its access is becoming as critical as managing code repository permissions.