The Technique
A new Model Context Protocol (MCP) server has been developed specifically for Kali Linux. This server exposes Kali's extensive toolkit—including network scanners, vulnerability assessment tools, and exploitation frameworks—as tools that Claude Code can call directly. Instead of manually switching to a terminal, running commands, and parsing output, you can now ask Claude to perform security tasks from within your coding session.
Why It Works
Kali Linux is the de facto operating system for penetration testing and security research, but its power is often locked behind complex, manual command-line workflows. The MCP protocol, which Claude Code uses to integrate with external tools and data sources, provides a perfect bridge. By wrapping Kali's tools in an MCP server, Claude gains structured access to their capabilities. This means Claude can execute a tool, understand its JSON-formatted results, and use that intelligence to plan the next step in a security workflow, all while you stay focused in your editor.
How To Apply It
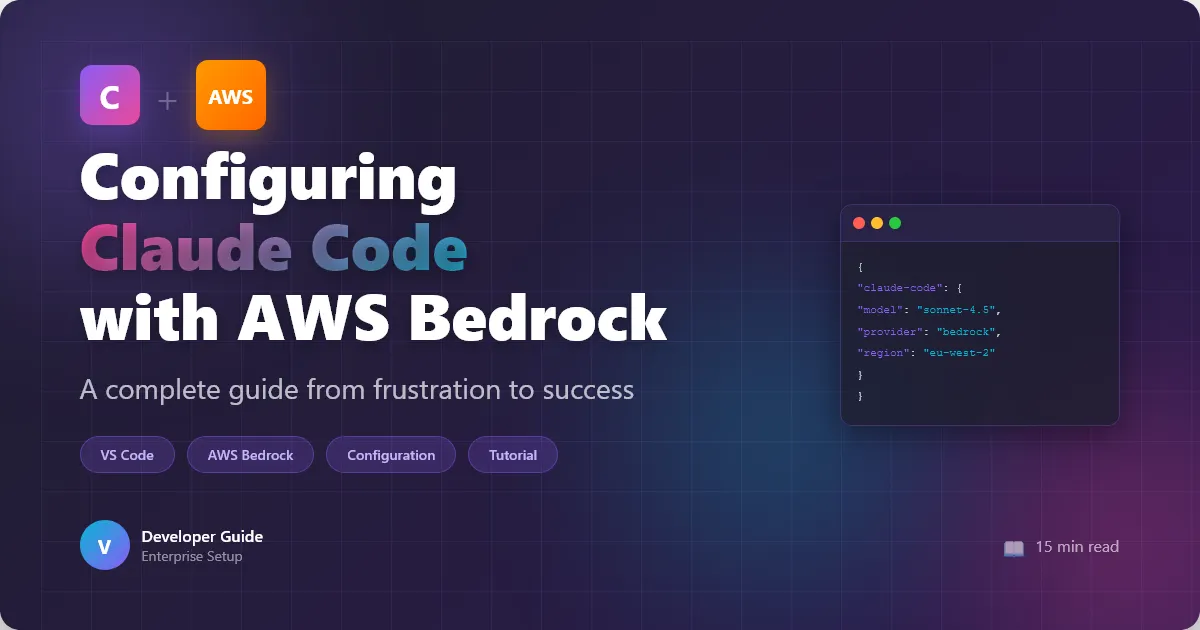
First, you need to set up the MCP server. The exact installation will depend on the server's repository (a search for "Kali Linux MCP server" should find it). Typically, it involves cloning a repo and adding a configuration block to your Claude Code settings.
Add a configuration to your claude_desktop_config.json:
{
"mcpServers": {
"kali-tools": {
"command": "node",
"args": ["/path/to/kali-mcp-server/build/index.js"],
"env": {
"KALI_TOOLS_PATH": "/usr/bin"
}
}
}
}
Once configured and Claude Code is restarted, the new tools will be available.
Example Prompt for Network Recon:
Instead of running Nmap manually, you can now write:
"@Claude, using the Kali tools, please perform a SYN scan on the target subnet 192.168.1.0/24 to identify live hosts and their open ports. Output the results in a markdown table."
Claude will call the Nmap tool through the MCP server, execute the scan, receive the structured results, and format them for you.
Automating a Workflow:
You can chain tasks. For instance:
- Reconnaissance: "Scan
example.comfor open ports 80 and 443." - Analysis: "Based on the banner from port 80, suggest potential next steps for vulnerability assessment."
- Exploitation: "If the server is running Apache 2.4.49, use the Metasploit tool to check for CVE-2021-41773 and provide a proof-of-concept command."
This turns Claude Code into an interactive security partner, capable of orchestrating multi-step penetration tests or security audits without you leaving your development environment.
Key Considerations
- Safety & Ethics: This tool grants significant power. Use it only on systems you own or have explicit permission to test. Claude's built-in ethical guidelines should help, but the responsibility ultimately lies with you.
- Tool Context: The MCP server provides the tools, but Claude needs the context to use them wisely. Be specific in your prompts about targets, scan types, and desired output formats.
- Local Execution: This workflow requires the MCP server and Kali tools to be running on your local machine or an accessible server. It's ideal for local lab environments.